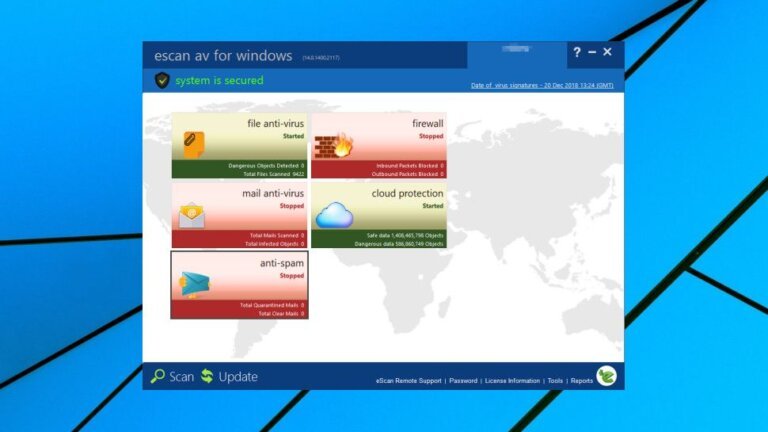
Windows 11 users face various cyber threats, making antivirus software essential. Many users mistakenly believe they are adequately protected by Windows Defender, which, while improved, may not be sufficient against modern threats. Effective antivirus solutions provide real-time protection, monitor behavior, and block phishing attempts, adapting to evolving threats. Key features to consider include low system impact, unobtrusiveness, and comprehensive protection across multiple devices. Popular antivirus options for 2026 include Bitdefender, Surfshark One, Norton, and Avast. Free antivirus tools offer basic protection but lack advanced defenses against phishing and ransomware. Paid solutions enhance security with features like real-time monitoring and additional privacy tools. Proper installation and configuration are crucial for optimal performance and protection. Users should choose antivirus software based on their individual habits and needs, ensuring it integrates seamlessly into their daily routines.