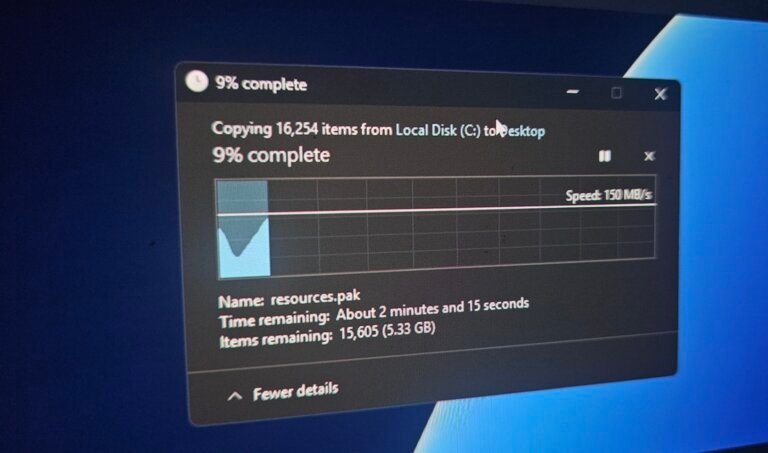
Windows 11 has introduced a dark theme that has received positive feedback, but certain legacy pop-ups, like the Properties tab, still use a light background. Microsoft is working on a dark-themed Properties tab and aims to enhance the dark mode experience across the operating system, as confirmed by senior executive Marcus Ash. He mentioned that there are no specific timelines for updates to legacy tools like the Registry Editor, but improvements are being made for consistency in dark mode across system-level dialogs. Third-party applications that do not adopt dark mode will continue to display in light mode, as Microsoft cannot enforce changes on them. Users currently experience inconsistencies with dark mode, particularly with legacy features that still show a light background. In December 2025, Microsoft rolled out dark mode for most operational dialogs, including those for file deletion and error notifications. Dark mode is now visible in various pop-ups, such as notifications for insufficient disk space and Recycle Bin confirmations. Microsoft is also testing dark mode in Windows Run (legacy).

![This is Android’s new ‘advanced flow’ for sideloading apps without verification, includes one-day waiting period [Gallery]](https://newapp.site/wp-content/uploads/2026/03/this-is-androids-new-advanced-flow-for-sideloading-apps-without-verification-includes-one-day-waiting-period-gallery-768x402.jpg)