Norton Antivirus has a score of 8.3/10. It offers extensive parental controls on some plans, cloud backups for sensitive data, and a high-quality safe browser. However, its identity theft protection features are limited to US-based users, it has higher resource usage than most competitors, and reaching human customer support can be difficult.
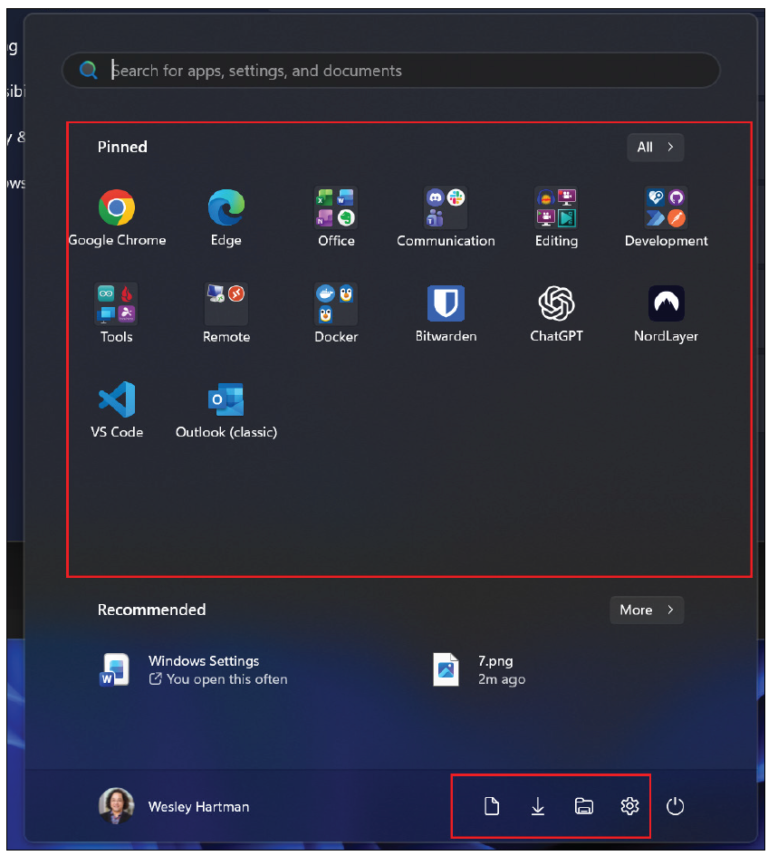
Norton began as an antivirus company in 1982 and has expanded to include a password manager, safe browser, cloud backups, and privacy monitoring tools. The LifeLock plans provide identity theft protection and insurance for US users. The antivirus software features easy setup, optimization tools for Windows and MacOS, scam detection, and privacy monitoring.
Norton offers various plans, including Norton AntiVirus Plus, Norton 360 Standard, Norton 360 Deluxe, and Norton 360 with LifeLock Select Plus, each with different features and pricing. The plans can cover multiple devices, with costs starting at a competitive rate for the first year.
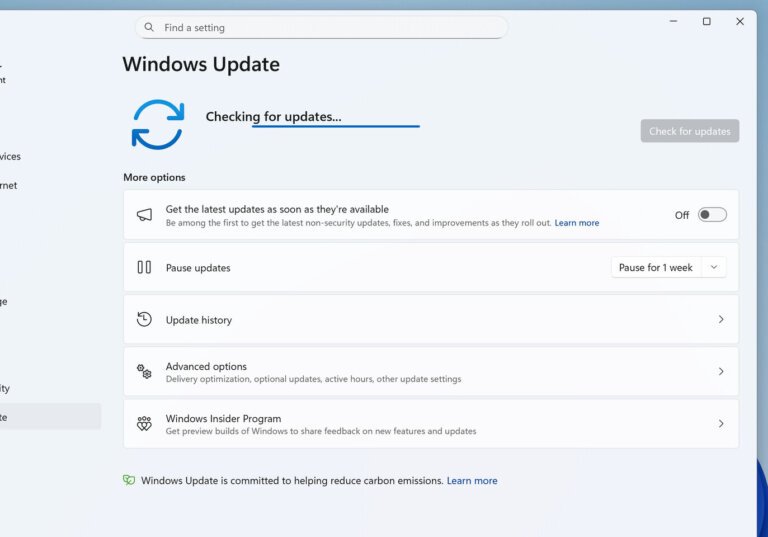
Norton’s antivirus software includes real-time protection, manual and automated scans, and scan scheduling. Its parental controls are a notable feature, and while cloud backups are available, storage may be limited. Free tools include a password manager, data breach scan, and safe browser.
Norton’s usability is straightforward, with an intuitive account setup and installation process. The antivirus operates with moderate resource usage, maintaining a low footprint during routine tasks.
Norton has a strong reputation for malware detection, maintaining a perfect security ranking from AV-Test and high online detection rates from AV-Comparatives. Its password manager and backup systems use AES-256 encryption, and its VPN follows a no-logs policy.
Customer support options include a community forum, knowledge base, and 24/7 live chat and phone support, though email support is not available.
Norton is considered a good value for families and budget-conscious users, with pricing starting at an affordable rate for single-device coverage. It is suitable for users seeking active threat protection and parental controls, though alternatives like Bitdefender or Malwarebytes may be better for those prioritizing efficiency and advanced features.