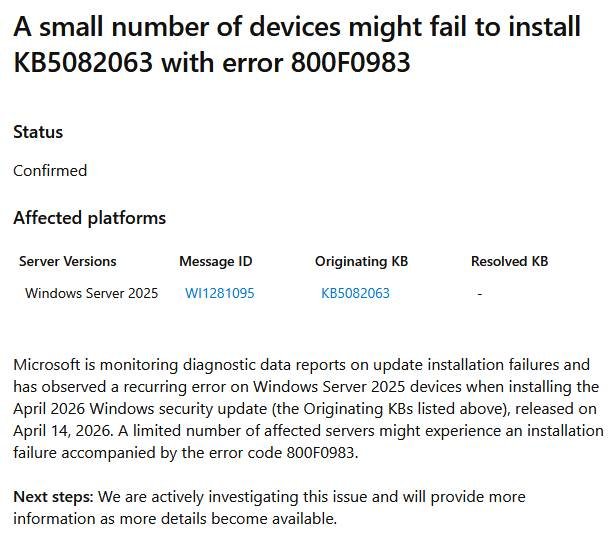
Cumulative update KB508206, released on April 14, 2024, for Windows Server 2025, is causing installation failures for some administrators. Error code 0x800F0983 has been acknowledged by Microsoft as an issue related to the update process, while error code 0x80073712 has been linked to the legacy Windows Media Player application. Reports indicate that the installation of KB5082063 is problematic, particularly on systems configured in German, with users experiencing persistent failures despite attempts to use repair commands. The installation issues may be related to missing files associated with the Media Player language packs, affecting various language configurations.