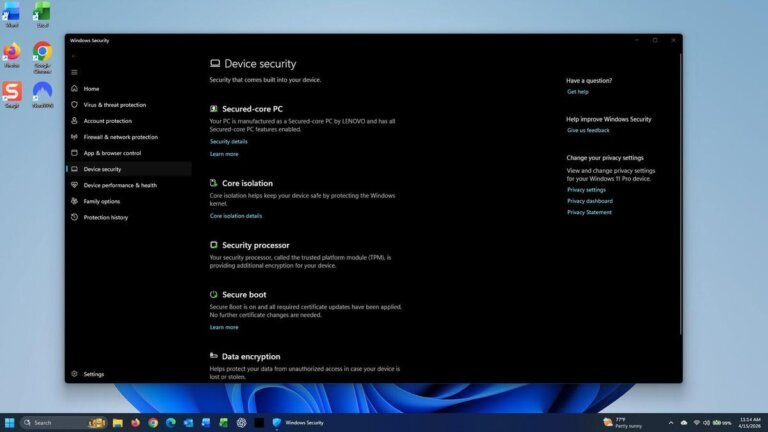
Microsoft has introduced a new feature in Windows 11 and Windows 10 that informs users about the status of Secure Boot as part of the April Patch Tuesday update. This feature includes a visual indicator that shows whether devices have the latest Secure Boot certificates, which protect against bootkit malware. The Secure Boot icon can display in green, yellow, or red, indicating different security statuses: green means secure with no actions needed, yellow indicates a pending safety recommendation, and red signals that immediate attention is required. Users can check their Secure Boot status through Settings in both operating systems. It is important to install the latest Windows updates to ensure devices have the most recent Secure Boot certificates, as older certificates will expire in June. The April updates also address 164 vulnerabilities, including eight classified as critical and two identified as zero-day flaws. Users are advised to prioritize these updates to maintain system security.