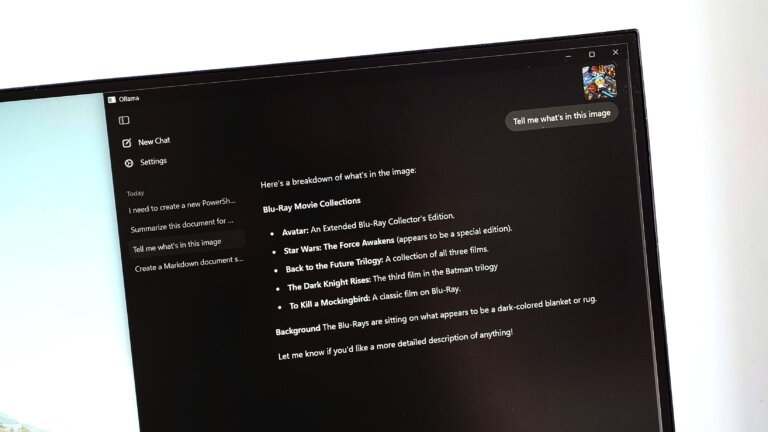
Fraudsters are using counterfeit CAPTCHA confirmation pages to deploy StealC, an information-stealing malware targeting Windows systems. Users are tricked into visiting compromised websites where a fake CAPTCHA prompts them to execute a sequence of keystrokes that runs a malicious PowerShell command. This command connects to a remote server, downloads shellcode, and injects the StealC payload into svchost.exe. Once installed, StealC collects sensitive information such as browser credentials, email data, and cryptocurrency wallet details, facilitating fraud and account hijacking. The malware operates primarily in the system's RAM, making detection difficult.