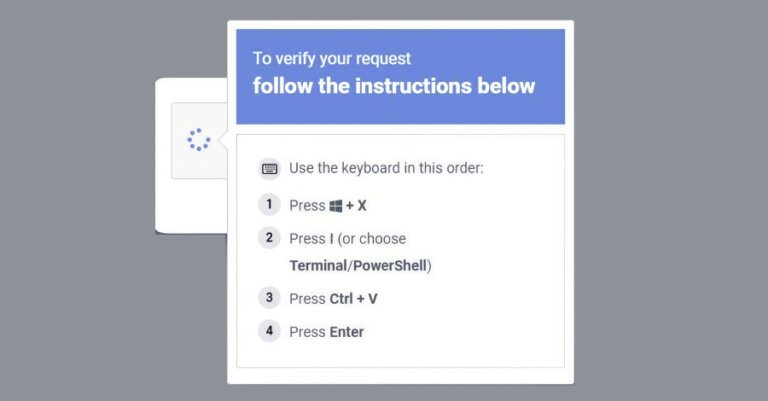
The FBI and CISA issued a joint public service announcement about Russian hackers targeting commercial messaging applications like Signal and WhatsApp. The hackers use social engineering tactics to deceive users into giving up account access, including impersonating support personnel and prompting users to click on malicious links or provide sensitive information. Although the hackers have not yet bypassed the apps' end-to-end encryption, compromised accounts can lead to serious consequences, such as reading messages and launching further phishing attacks. The agencies recommend that users enhance their cybersecurity measures to protect against these threats. This campaign is part of a broader trend to undermine the security of messaging apps, with previous warnings about spyware and attempts to infiltrate Signal users, especially in conflict zones.