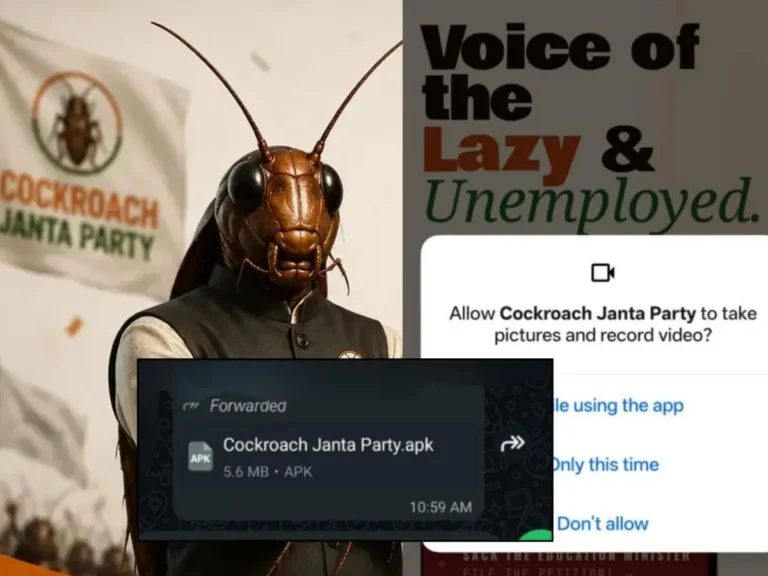
A cybersecurity report released on May 22, 2026, identifies a counterfeit Android application posing as the official app of the Cockroach Janta Party as a significant malware threat. The malicious app, known as Cockroach.Janta.Party, functions as a Remote Access Trojan (RAT) and can infiltrate Android devices, steal sensitive information, intercept communications, and control infected smartphones. The genuine Cockroach Janta Party has no affiliation with this app and is a victim of brand impersonation. The app is distributed through WhatsApp, Telegram, and misleading websites, particularly a rogue domain, cockroachjantaparty[.]org. It targets Android devices running versions 8.0 to 14 and requests elevated permissions, including access to camera, SMS, call logs, and contacts, while misusing the Android Accessibility Service to read on-screen content and grant itself additional permissions. The app contains multiple malicious modules for data exfiltration and uses a Command and Control infrastructure based on the Telegram Bot API. Users are advised to uninstall the app, disable Accessibility permissions, reset banking credentials, enable two-factor authentication, and conduct a full mobile security scan. The legitimate Cockroach Janta Party is encouraged to issue a formal clarification regarding the impersonation.