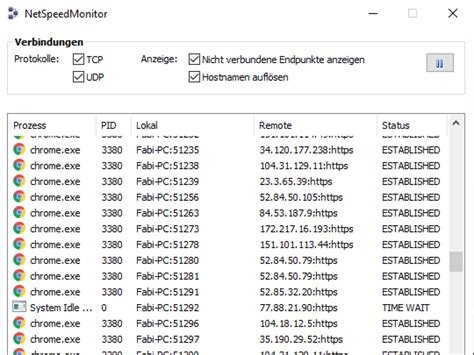
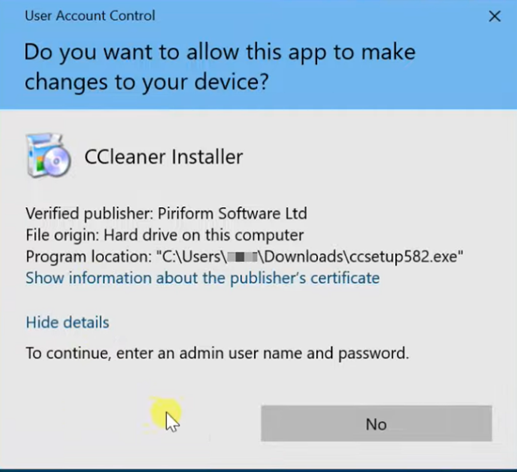
Free antivirus solutions have improved significantly, providing users with protection that was once exclusive to paid software. Major players in the market include Avast, Bitdefender, AVG, and Malwarebytes, each offering distinct features and limitations. While effective against common threats like viruses and malware, these free tools often lack advanced privacy tools and comprehensive security coverage.
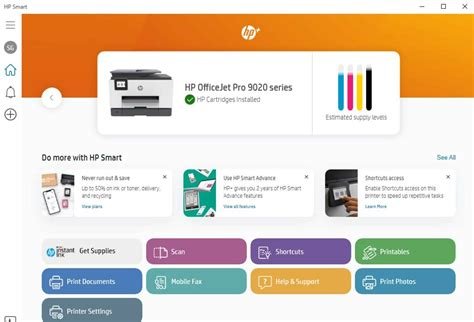
Avast One Basic offers real-time scanning and basic tools like a VPN and system cleanup, while AVG AntiVirus Free provides a streamlined user experience with a focus on simplicity. Avira Free Security includes additional features such as a basic VPN and privacy management tools, making it a more comprehensive free option. McAfee Free serves as an introduction to its broader ecosystem but lacks depth in protection.
Free antivirus tools remain popular due to improved everyday protection, ease of use, and cost-effectiveness, especially for mobile users. They utilize cloud intelligence for better performance and can handle basic security needs. However, they may not suffice for users with high-risk profiles or those needing advanced privacy features.
Key criteria for free antivirus solutions include core protection through real-time monitoring, seamless performance, user-friendly interfaces, and additional valuable tools. Limitations include basic protection against emerging threats, intrusive upgrade prompts, slower updates to threat databases, limited support options, and potential privacy trade-offs.
Alternatives to free antivirus software include Bitdefender, Surfshark One, Norton 360, Avast Premium Security, and Avira Prime, which offer more robust protection and features.