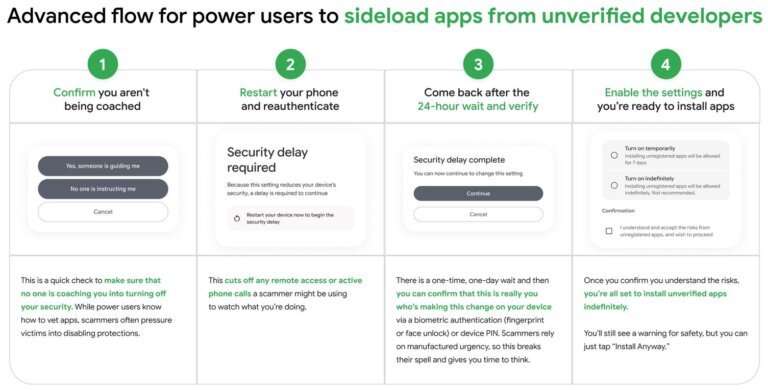
Google is implementing stricter measures for installing Android applications outside of its Play Store, requiring all apps to be signed by verified developers. Users will now access the Allow Unverified Packages setting through Developer Options, with a 24-hour security delay after device restarts. A limited free developer account option allows only 20 device installations, with a fee and government-issued ID required for more. These changes will affect third-party app stores, which must also comply with the new verification requirements. Scammers may still find ways to bypass these restrictions.