Creating an Android app has become accessible even for those without coding expertise, involving several straightforward steps:
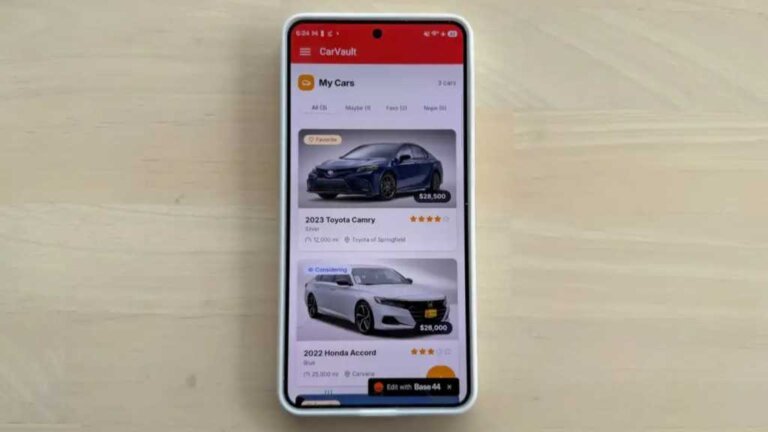
1. Brainstorm a unique app idea that addresses a gap in existing applications, such as an app for taking notes during car test drives.
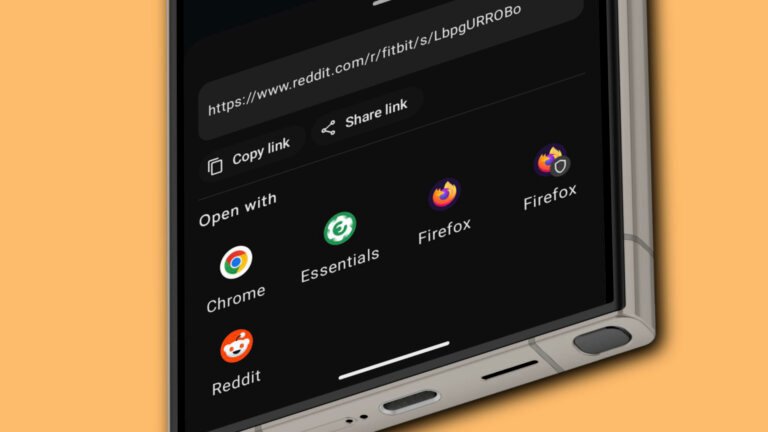
2. Use AI app builders like Base44, which require no coding knowledge, to create the app. After setting up an account, users can prompt the platform to generate an app interface and name.
3. Test the web version of the app thoroughly to ensure all features work smoothly, with troubleshooting support available through the platform.
4. Launch the app by signing up for a Google Play Store developer account for publishing or sideloading it for personal use. Services like AppMyWeb can help transform the web app into a mobile application, requiring users to adjust device settings for installation.
The entire process can be completed in about 15 minutes.