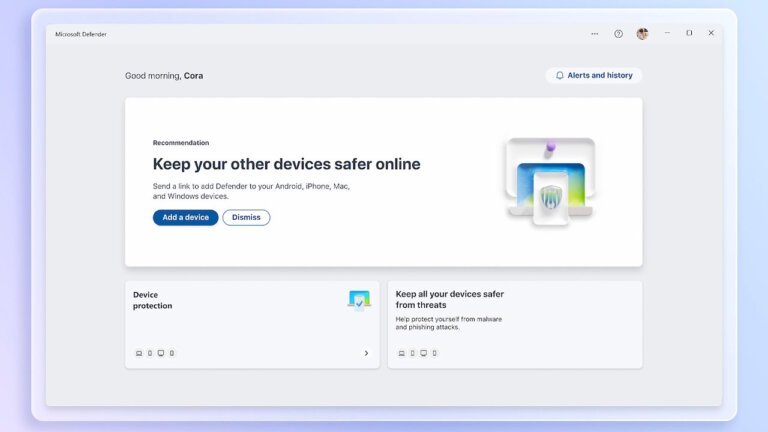
On April 30, 2026, Microsoft Defender misclassified two legitimate DigiCert root certificates as a severe threat, specifically Trojan:Win32/Cerdigent.A!dha, leading to their quarantine and disrupting SSL/TLS validation across affected endpoints. This misclassification was a result of new malware detections introduced by Microsoft in response to concerns over compromised certificates from a DigiCert breach. The false-positive alerts were triggered by the registry entries of the two trusted root certificates, which are crucial for validating SSL/TLS sessions. Microsoft later acknowledged the error and adjusted the alert logic. There was no actual compromise of the DigiCert certificates, as administrators confirmed that the certificate hashes matched the official values. The misclassification stemmed from a failure to properly constrain the detection to only revoked end-entity signing certificates related to a separate incident. This incident follows a pattern of Microsoft Defender misidentifying legitimate software as malicious, as seen in a 2022 incident where Microsoft Office was flagged as a virus. Organizations with restrictive update policies may continue to face SSL/TLS validation failures until they deploy the corrective Security Intelligence version or manually restore the DigiCert roots.