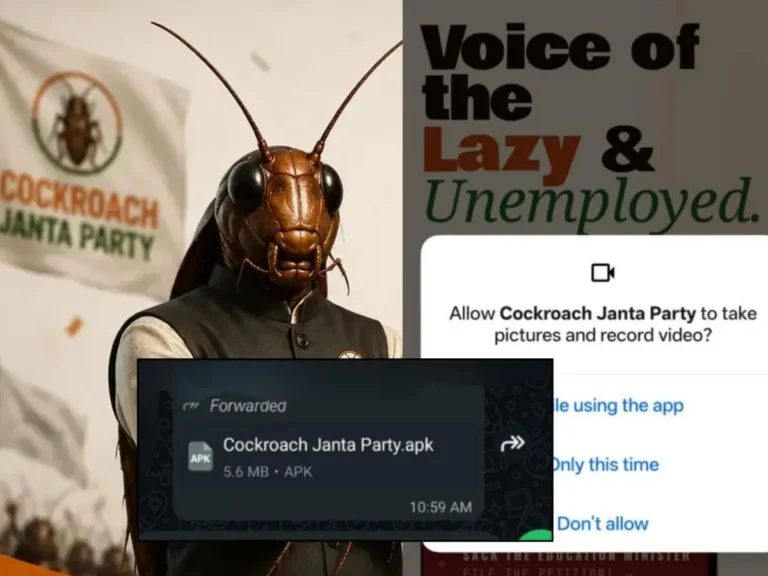
A surge in Windows malware campaigns has been identified, with malicious software hidden in pirated PC games and modified installers for popular franchises like Far Cry, Need for Speed, FIFA, and Assassin’s Creed. Over 400,000 devices globally have been affected, with around 30,000 cases in the United States. The malware, known as the "RenEngine loader," is disguised as a legitimate game launcher and infects systems when users download cracked games. It aims to deploy an infostealer called ARC, which can capture sensitive information such as passwords and cryptocurrency wallets, and may also install other harmful payloads like the Rhadamanthys stealer and Async Remote Access Trojan (RAT). Users often remain unaware of their infection until significant damage occurs. Recommendations for safety include avoiding unofficial downloads, using up-to-date anti-malware protection, and regularly updating software.