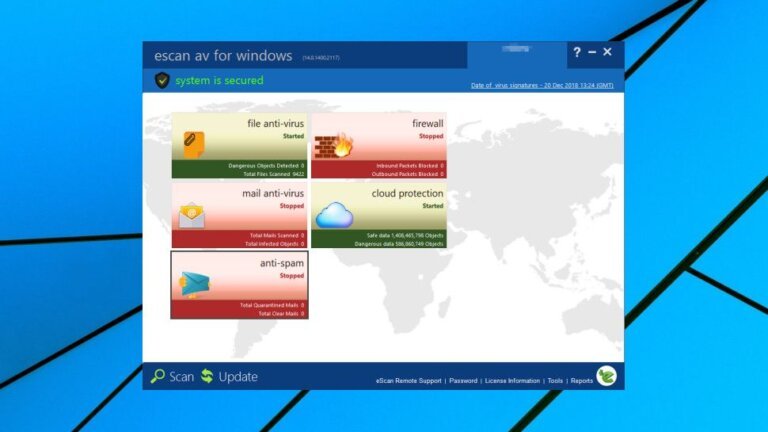
Recent reports indicate that the antivirus program eScan experienced a security breach, leading MicroWorld Technologies to conduct an internal investigation. A threat actor exploited compromised update servers to distribute malware to users who downloaded updates during a two-hour window on January 20, 2026. The exact number of affected users is unknown, but the company has isolated the compromised infrastructure and refreshed credentials while assisting impacted users. The eScan product itself was not altered, and the victims were limited to a specific regional cluster. The malware, identified as CONSCTLX, operates as a backdoor and downloader, allowing attackers to maintain access and execute commands on infected devices. The identity of the attackers is unknown, but North Korean cybercriminals previously exploited eScan's update mechanism in 2024. MicroWorld Technologies has provided support to millions of customers but has not disclosed the total number of eScan users.