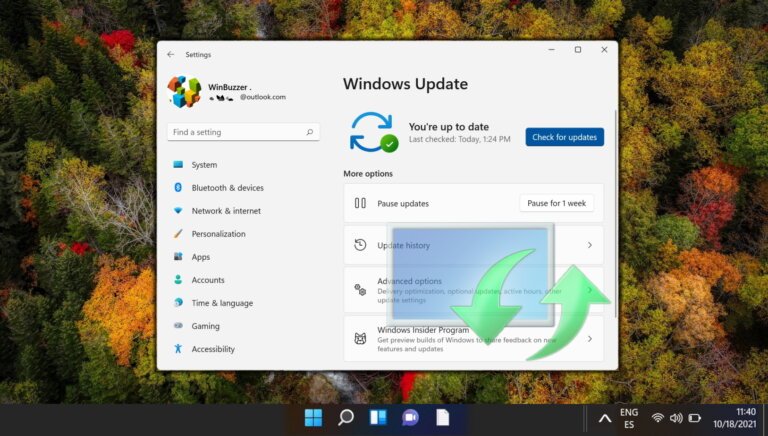
The Windows Insider Program is undergoing changes to improve user experience based on feedback from the community. The channel structure will be simplified into two main options: Experimental and Beta. The Experimental channel will provide early access to features under development, while the Beta channel will showcase features planned for near-term release without gradual rollouts. Users will have the option to select specific Windows core versions and enable or disable features through a new Feature flags page. Additionally, transitioning between channels will now allow for in-place upgrades, preserving apps and settings, except when moving from Experimental Future Platforms. All Insiders will be transitioned to either the new Beta or Experimental channel, with specific transitions outlined for current users in the Beta, Dev, and Canary channels. Commercial customers will see similar changes, while those in the Windows Server Insider Program will not experience alterations.