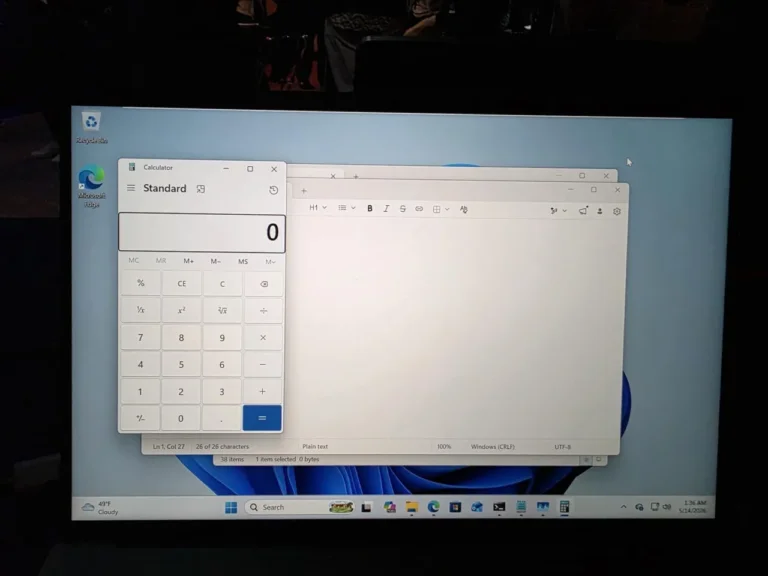
In April 2026, a blog post from Microsoft's Windows Learning Center claimed that most Windows 11 users could rely solely on Windows Security (Defender) for antivirus protection, citing features like Microsoft Defender Antivirus, SmartScreen, and ransomware mitigation. The blog was later removed without explanation, leading to speculation about its definitive claims. Microsoft stated that Windows Defender was sufficient for typical users with default settings and regular updates, while cautioning against using multiple antivirus engines. Independent testing from AV-Test consistently ranks Microsoft Defender highly, but AV-Comparatives noted limitations in offline protection and the reliance on cloud-based intelligence. The blog's removal was viewed by some as a constructive step towards realistic security guidance. Microsoft continues to provide third-party antivirus vendors with significant access to Windows, and the rise of AI-generated threats is complicating the cybersecurity landscape. Despite the controversies, Microsoft has made significant advancements in Windows Security, making it a viable option for many users.