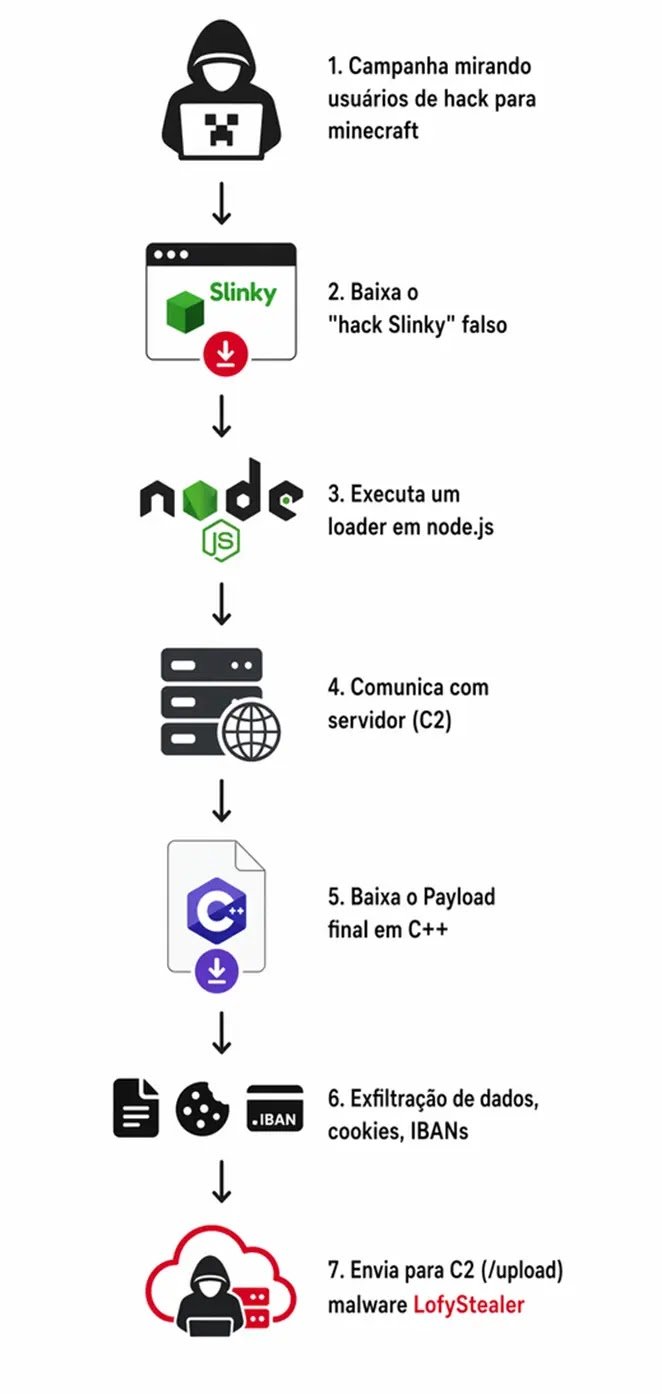
A new infostealer malware called LofyStealer is targeting the gaming community, particularly Minecraft players, by disguising itself as a cheat tool named “Slinky.” It employs a two-stage attack to extract sensitive information from eight major web browsers, including Chrome and Firefox, while evading detection by security software. The malware siphons off cookies, saved passwords, payment card information, and session tokens. Researchers at Zenox.ai identified LofyStealer, linking it to the Brazilian cybercrime group LofyGang, which has been active since October 2022. The malware uses social engineering tactics to appear legitimate and operates as a Malware-as-a-Service platform, offering both Free and Premium tiers to buyers. Its technical sophistication is evident in its method of in-memory browser injection, which allows it to bypass security defenses. The stolen data is compressed and sent to a command-and-control server. Users are advised to avoid downloading unofficial game mods and enable multi-factor authentication to reduce the risk of credential theft. Security teams should monitor for specific behavioral indicators related to the malware's operations.