Emergence of Morpheus Spyware: A Deep Dive into Covert Surveillance
The nonprofit organization Osservatorio Nessuno has unveiled a new spyware known as Morpheus, which is reportedly disseminated through counterfeit Android applications masquerading as legitimate updates. This alarming development underscores the escalating demand for covert surveillance tools among law enforcement and intelligence agencies, fostering a burgeoning market for spyware vendors that often operate under the radar.
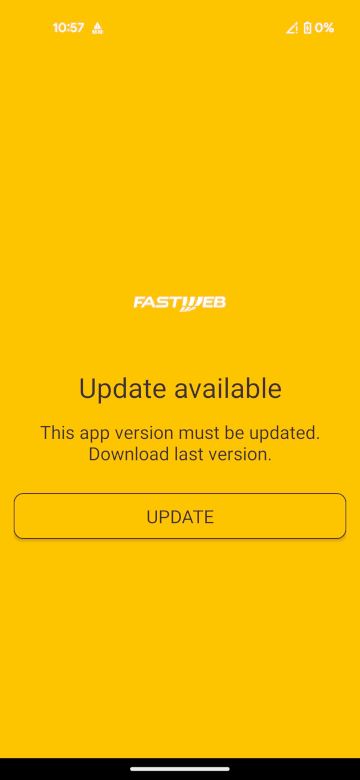
In a familiar tactic employed by low-cost spyware, attackers disrupt a service and manipulate victims into downloading a fraudulent app to restore functionality. In this instance, targets received SMS messages directing them to a website that impersonated an Internet Service Provider (ISP). The initial phase involves a dropper app that installs a concealed second-stage payload. This payload checks for its prior installation and, if absent, deploys itself with minimal user awareness.
The second stage of Morpheus camouflages itself as legitimate system components, utilizing deceptive icons and names to gain user trust. It coerces users into granting perilous permissions, including Accessibility access, which enables it to read screens, interact with applications, and capture sensitive information.
“After granting Accessibility permissions, the spyware initiates a Permission Workflow that creates an overlay featuring a fake update process and a counterfeit reboot screen. In the background, the workflow executes all necessary steps to secure permissions, including enabling Developer Options, activating Wireless Debugging, and establishing a local connection to the ADB daemon,” the report from Osservatorio Nessuno details. “During this deceptive update, the app disables the touchscreen by setting FLAGNOTTOUCHABLE on the full-screen overlay, leaving the user partially incapacitated to respond to the infection.”
Morpheus also ensures its persistence by restarting after device reboots and can request device administrator privileges, complicating removal efforts. This capability facilitates long-term, covert surveillance of the compromised device.
The spyware exploits overlay windows and Accessibility features to seize control of the device and circumvent security measures. By leveraging the powerful SYSTEMALERTWINDOW permission, it presents fake screens—such as updates or reboots—while secretly granting itself permissions in the background, even disabling touch input to restrict user control. Victims can be misled into approving actions, such as linking a WhatsApp account, through a phony biometric prompt.
Moreover, Morpheus activates Wireless Debugging and connects to ADB to obtain elevated privileges, silently securing sensitive permissions while disabling security features like camera and microphone indicators, Play Protect, and antivirus applications.
“In the third phase, the spyware disables several well-known antivirus solutions, including Google’s SafetyCore, Bitdefender, Sophos, Avast, AVG, and Malwarebytes, along with various smaller antivirus applications popular on budget devices,” the report continues. “None of these actions require root access and persist across reboots, as the Android security model treats user-installed anti-malware software like standard applications.”
To ensure its persistence and evade detection, Morpheus adjusts system settings across various Android versions, maintaining comprehensive access to the device.
Analysis of the source code hints at an Italian origin for the spyware, with language clues and references like “aprafoco” and “Gomorra.” The malware is designed to support multiple languages and Android devices, indicating a broader targeting strategy. Its infrastructure employs encrypted configurations, Italian-hosted servers, and domains associated with small ISPs and obscure entities characterized by generic details.
Researchers identified connections between hosting providers, dubious companies, and shared contacts. The phishing domain is registered to a small Italian firm with limited activity, linked to other questionable businesses. Overlapping financial and corporate ties suggest a network of related entities potentially facilitating the spyware operation while obscuring its true ownership.
Osservatorio Nessuno concluded that Morpheus is linked to IPS Intelligence, an Italian firm with over three decades of experience in lawful interception technologies utilized by governments for monitoring communications through telecom and internet providers.
“While IPS Intelligence is a recognized commercial surveillance provider, this is, to our knowledge, the first report connecting them to the distribution and operation of spyware,” the report states. “Morpheus is exceptionally invasive: it can record audio and video, silently pair a WhatsApp device, erase evidence, and deliberately compromise the security of the infected phone, among other malicious capabilities.”
Details regarding the isolation or identification of the sample remain undisclosed, leaving the exact collection and analysis process a mystery.