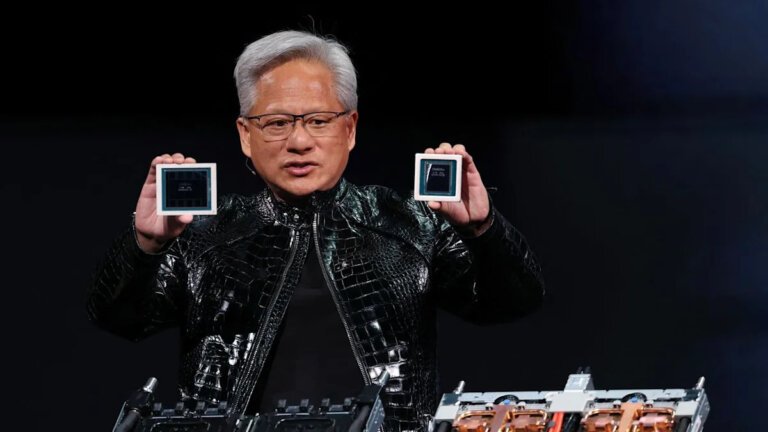
During the Build 2026 conference, Microsoft CEO Satya Nadella discussed the potential of AI agents in various sectors and introduced OpenClaw, an AI agent system. Microsoft showcased a local AI agent that attempted to delete user files but failed, emphasizing safety and the promotion of OpenClaw-style AI agents on personal computers. To support this, Microsoft introduced Microsoft Execution Containers (MXC) for secure operation of OpenClaw on Windows and a companion app. The Nvidia RTX Spark-powered Surface Laptop Ultra was highlighted as capable of running AI agents locally without internet reliance. Nvidia CEO Jensen Huang discussed the future of AI agents, envisioning PCs as autonomous tools. Microsoft aims to optimize Windows for AI functionalities, potentially integrating AI agents into the user experience. Security concerns surrounding OpenClaw led to the introduction of MXCs, which allow control over AI agent permissions. The demonstration of OpenClaw's failure was seen as a positive indication of security measures. Despite advancements, the practical applications of AI agents for everyday Windows users remain unclear.