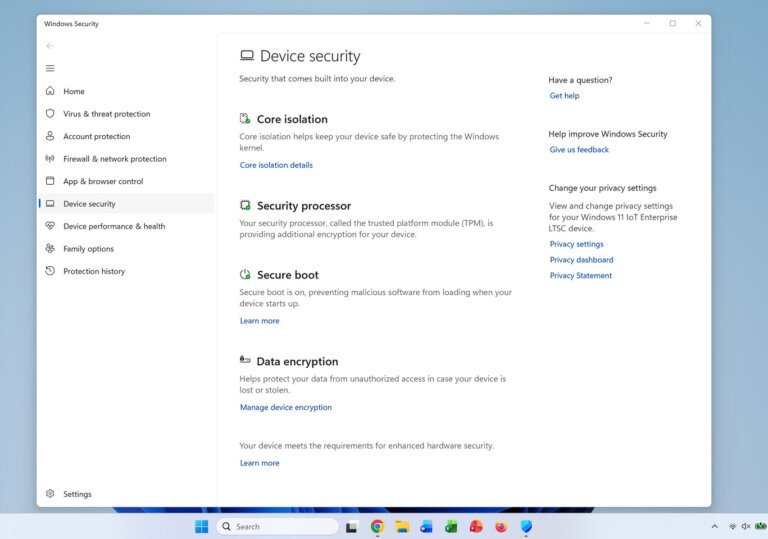
Windows 11 has introduced a feature that allows users to verify the status of their Secure Boot certificates directly from system settings, simplifying the process ahead of the June 2026 expiration deadline. This update enhances accessibility and empowers users to maintain system security against vulnerabilities. Secure Boot helps prevent unauthorized software and malware from loading during startup, and confirming certificate status can mitigate risks associated with system breaches.