Every Secure Boot-enabled Windows PC has relied on a set of cryptographic certificates issued by Microsoft in 2011 to ensure a secure boot process. These certificates, embedded in the motherboard’s firmware, have quietly safeguarded the integrity of software loading before Windows starts. However, a significant change looms on the horizon: on June 24, 2026, the first of these certificates will expire. While this expiration won’t abruptly halt your PC from booting or receiving regular updates, it will impede the ability to receive future security updates for critical components of the Windows startup process. Microsoft has initiated the rollout of replacement certificates through Windows Update, marking this as one of the most extensive coordinated security maintenance efforts across the Windows ecosystem.
Secure Boot’s trust chain is built on certificates that were never meant to last forever
To grasp the implications of this situation, it’s essential to understand the mechanics of Secure Boot. It operates as a chain of trust, a hierarchy of cryptographic certificates stored within your motherboard’s UEFI firmware, validating every piece of software that runs prior to the operating system loading. At the apex of this chain is the Platform Key (PK), owned by the PC’s manufacturer. This key serves as the root of trust, authorizing changes to subsequent layers. Below the PK lies the Key Exchange Key (KEK), which allows Windows to update the Signature Database (DB) and the Forbidden Signature Database (DBX).
The DB contains certificates that your PC trusts for signing bootloaders, drivers, and firmware components, while the DBX contains signatures of known malicious software that should never execute during boot. Secure Boot checks everything against these databases, ensuring that only trusted software runs. However, with three critical certificates in this chain set to expire—two in June 2026 and one in October 2026—your PC will lose the ability to validate new updates and apply security mitigations, effectively freezing its protections at the expiration date.
The replacement certificates split things up for a reason
The replacement certificates introduced in 2023 are not merely a direct swap; they represent a restructured approach to certificate management. The original Microsoft Corporation UEFI CA 2011 signed everything, including third-party bootloaders and firmware components, creating a broad trust that could lead to unpredictable vulnerabilities. The new structure delineates responsibilities: the Microsoft Corporation KEK 2K CA 2023 replaces the KEK, the Windows UEFI CA 2023 is designated for Windows boot loader components, and a separate Microsoft Option ROM UEFI CA 2023 is established for third-party option ROMs and add-in card firmware. This separation enhances the granularity of Secure Boot’s trust model, a change that was long overdue.
The urgency of this update is underscored by the emergence of BlackLotus, a UEFI bootkit discovered in 2023 that bypassed Secure Boot on fully updated Windows 11 systems. This vulnerability exploited weaknesses in the management of certificate-based trust at the firmware level, allowing attackers to compromise the boot process. Microsoft has been working diligently to revoke vulnerable boot managers, but the complexity of managing these updates has made the process slow and fraught with risks.
Not every PC is in the same boat
Fortunately, not all PCs are facing this impending deadline. Copilot+ PCs and most devices manufactured since 2024 already come equipped with the new 2023 certificates. For those who purchased a new PC in the last couple of years, the transition should be seamless. However, for the majority of Windows PCs still in active use, timely updates are crucial. Microsoft is gradually rolling out the new certificates through Windows Update, with home users on Windows 11 receiving these updates automatically. Enterprise environments, however, require more intricate coordination, as IT administrators must enable diagnostic data and apply firmware updates from the OEM before the Windows certificate update can be successfully implemented.
Windows 10 users are in an especially tough spot
Windows 10 users face a particularly challenging situation. With support for Windows 10 ending in October 2025, devices running this version will not receive the new Secure Boot certificates unless they have enrolled in Extended Security Updates. Microsoft’s recommendation is to upgrade to a supported version of Windows, typically Windows 11, but many users may find themselves locked out due to stringent hardware requirements. This situation leaves a significant number of users with aging machines unable to access updated security measures.
What you should actually do right now
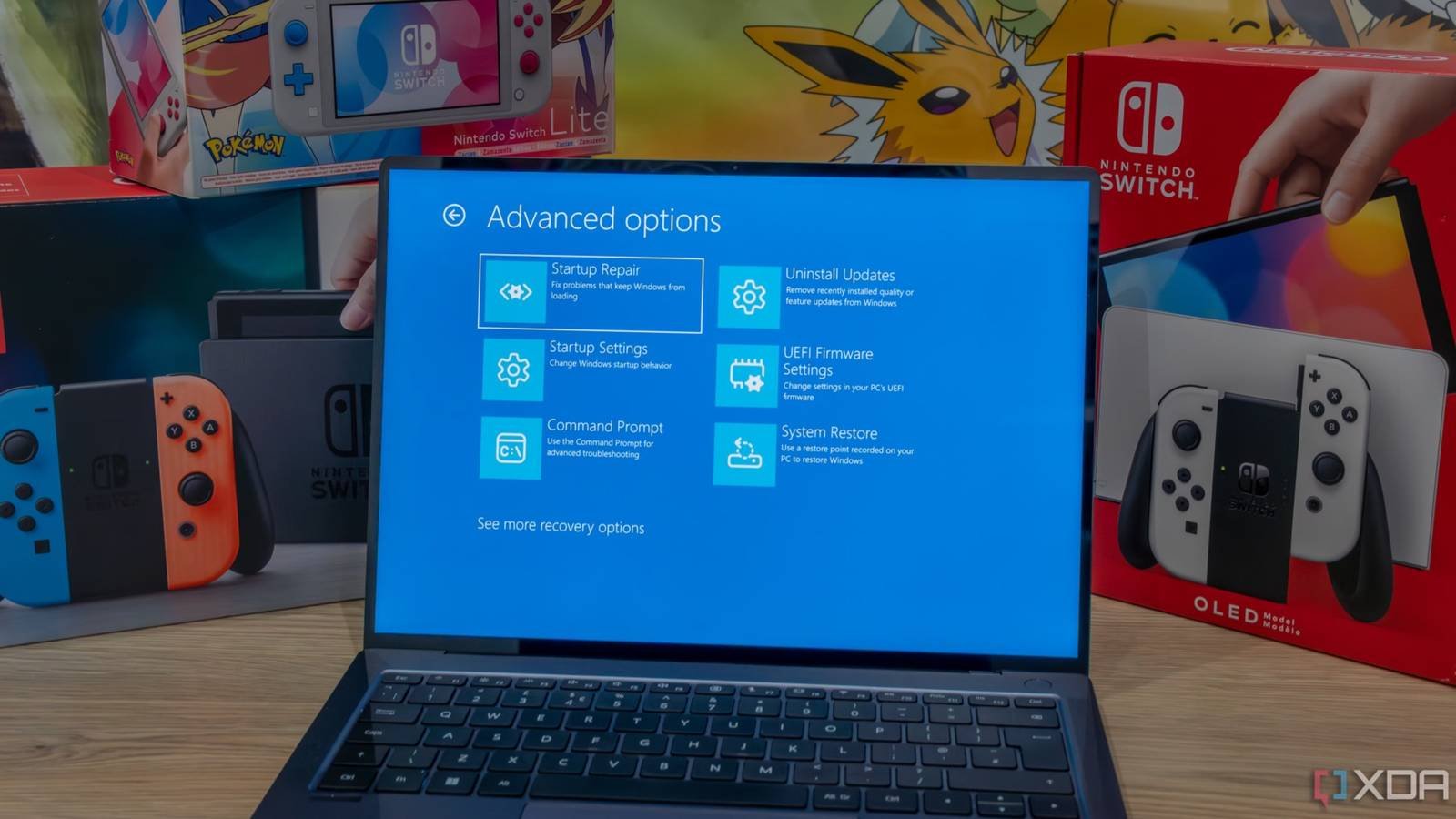
For home users, ensuring that your PC is set to receive Windows updates automatically is essential. Check with your manufacturer for any available BIOS or firmware updates and install those prior to allowing Windows Update to proceed. Keep an eye on the Windows Security app for notifications regarding certificate status as Microsoft rolls out updates.
For enterprise environments, the urgency is heightened. IT administrators should consult the Secure Boot certificate rollout landing page for the latest guidance. Begin by checking the “UEFICA2023Status” registry key to monitor deployments and ensure that OEM firmware updates are applied across all devices before the Windows certificate update occurs. With the expiration dates approaching, the need for proactive measures is clear. The boot chain’s integrity is paramount, as it serves as the foundation for all subsequent security measures within the system.