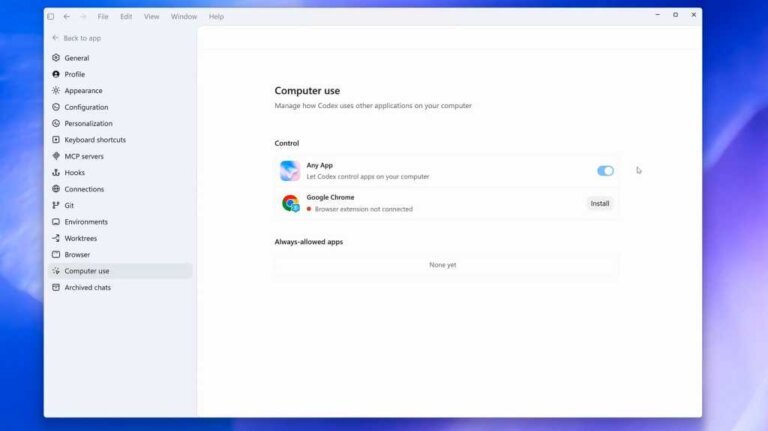
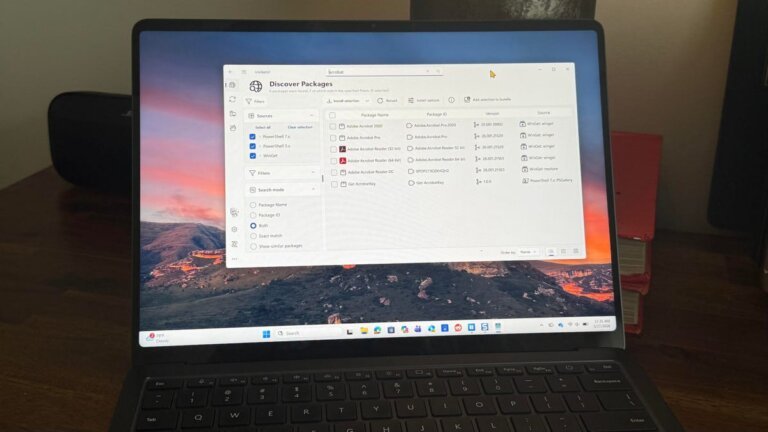
OpenAI has announced that the Codex desktop's Computer Use feature is now available on Windows 11 systems, previously exclusive to macOS. This feature allows Codex to control applications on a user's computer using a virtual mouse and keyboard, enabling it to autonomously navigate the system and execute tasks. Users can direct Codex by referencing their computer or specific applications in their instructions. The feature is integrated with mobile applications, allowing users to manage tasks on their Windows systems from mobile devices. Currently, it is available across all Codex plans, including free tiers, but access may eventually be limited to premium plans.