A new Remote Access Trojan (RAT) has emerged on underground forums, being marketed as a fully undetectable (FUD) alternative to the legitimate remote access tool, ScreenConnect. This malware is being promoted with a suite of advanced features aimed at circumventing modern security defenses, highlighting a concerning trend in the availability of sophisticated cybercrime tools.
The seller asserts that this RAT achieves zero detections during both static and runtime analysis, positioning it as a formidable threat for initial access and payload delivery operations. Such claims reflect the ongoing efforts by malicious actors to exploit trust and evade detection by mimicking legitimate software and processes.
Bypassing Security With Advanced Evasion
The primary allure of this new RAT lies in its capability to bypass security warnings from both Google Chrome and Windows SmartScreen. The threat actor claims this is accomplished by bundling the malware with a valid Extended Validation (EV) certificate. EV certificates represent a high-assurance digital identity standard, typically causing browsers to display a green bar or the company’s name, which can instill a false sense of security in potential victims.
Additionally, the malware package boasts antibot mechanisms and cloaked landing pages. These features enable the malware to present benign content to security scanners and sandboxes while delivering the malicious payload to actual targets, a common tactic employed to evade automated analysis.
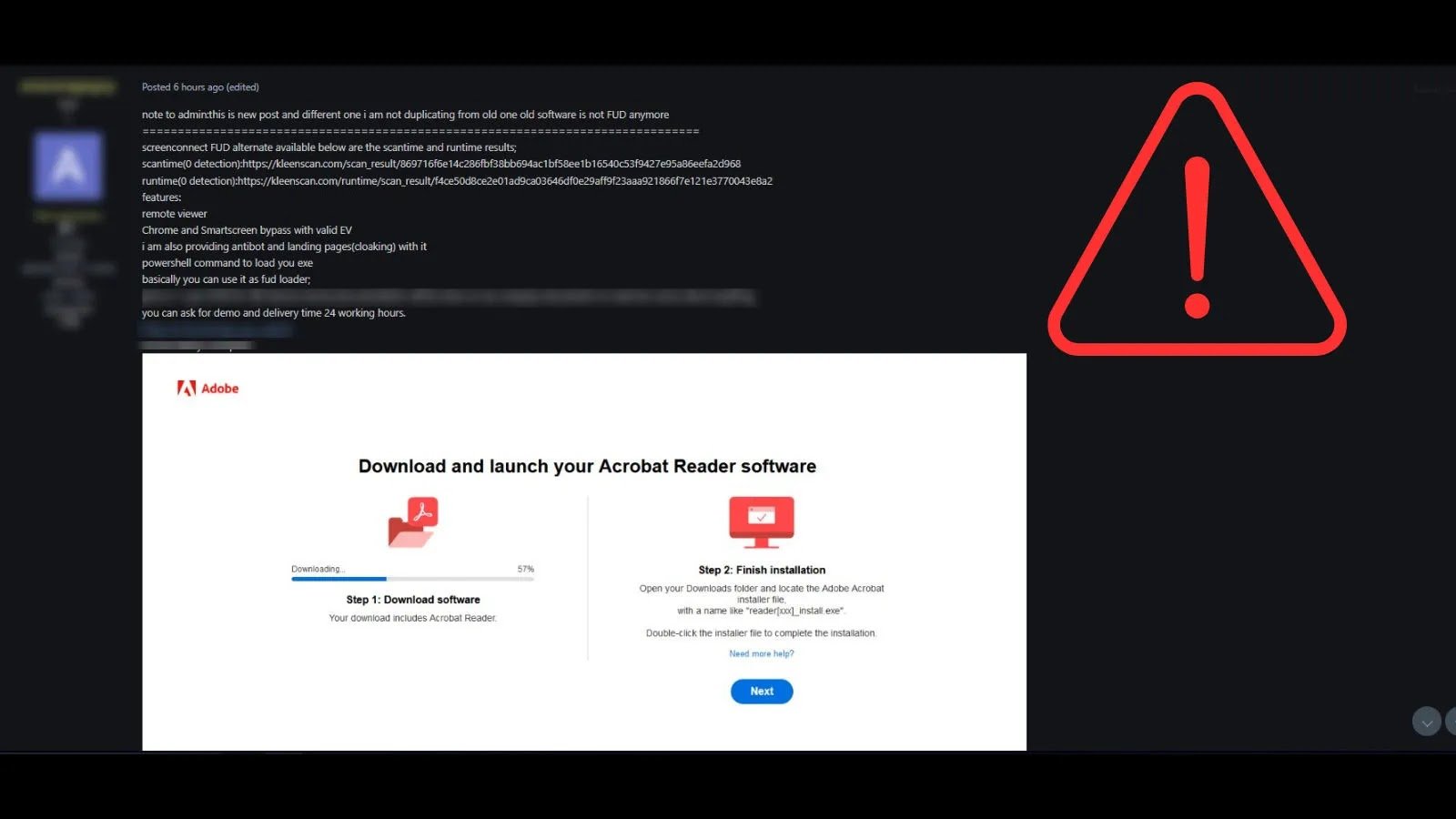
The advertisement showcases a convincing yet fraudulent Adobe Acrobat Reader download page, exemplifying a typical social engineering scheme for malware delivery. According to the seller’s post, the RAT includes a remote viewer, allowing the attacker direct visual control over a compromised machine’s desktop. This functionality facilitates real-time monitoring, data exfiltration, and interactive system manipulation.
Moreover, the tool employs a PowerShell-based command to load its executable, a fileless technique that helps it remain concealed from traditional antivirus solutions that primarily focus on scanning files stored on disk. The actor explicitly mentions that the tool can serve as a “FUD loader,” indicating its primary role may be to establish a persistent and stealthy foothold on a target system before deploying secondary payloads, such as ransomware, spyware, or banking trojans.
The seller further enhances the appeal of this offering by providing a demo and promising delivery within 24 working hours, suggesting a level of professionalism and operational readiness in this illicit service.
Find this Story Interesting! Follow us on Google News, LinkedIn, and X to Get More Instant Updates.