A critical local privilege escalation (LPE) vulnerability affecting Microsoft Windows has recently surfaced, following the public release of a Proof-of-Concept (PoC) exploit. This vulnerability, tracked as CVE-2026-20817, is embedded within the Windows Error Reporting (WER) service, presenting a significant security concern.
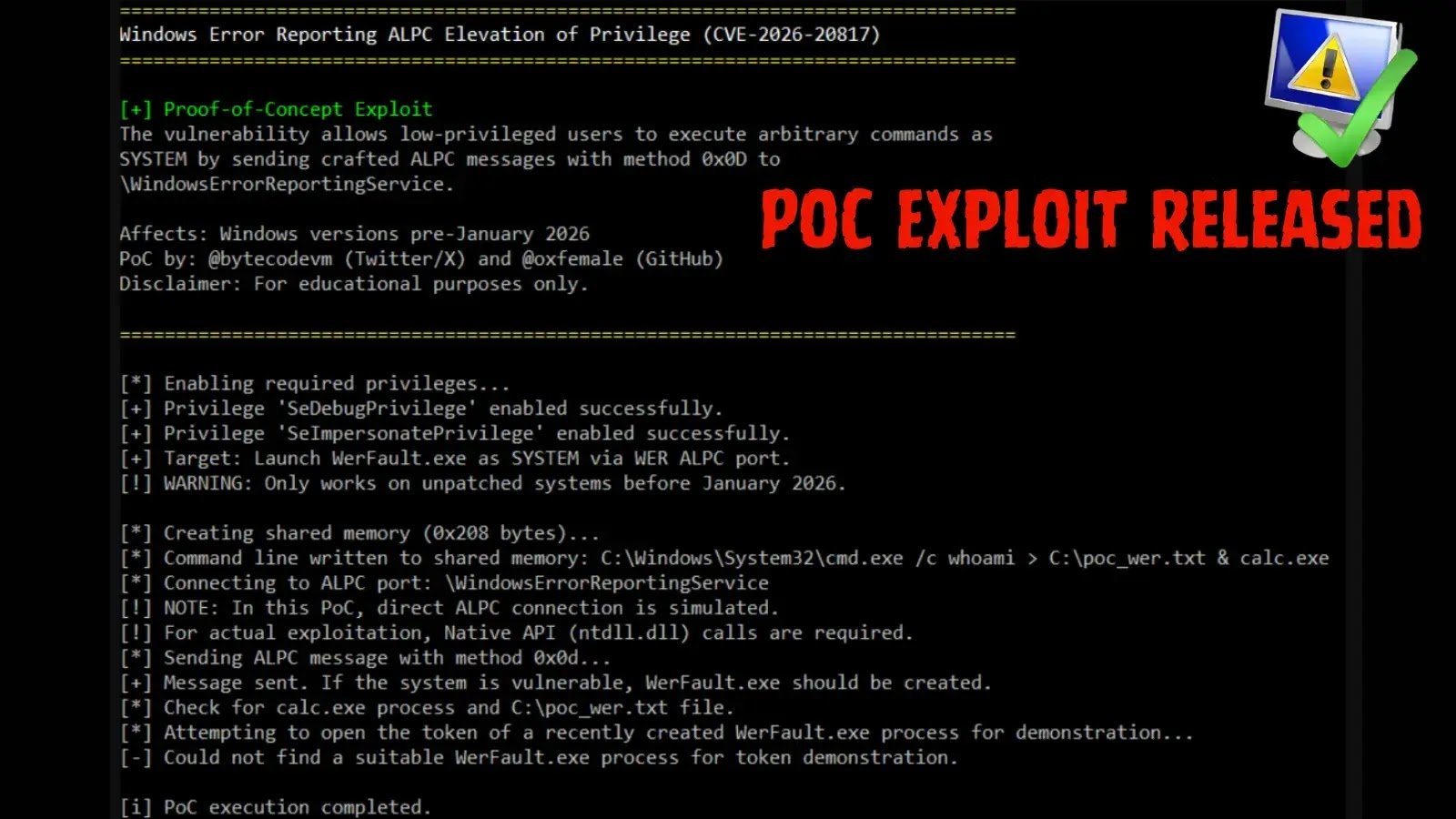
The flaw allows an authenticated user with low-level privileges to execute arbitrary malicious code with full SYSTEM privileges. The detailed research, along with a C++ PoC exploit, was made available on GitHub by security researcher @oxfemale (also known as @bytecodevm on X/Twitter).
This release brings to light a notable security gap in Windows’ error-reporting mechanisms for interprocess communication, particularly involving the Advanced Local Procedure Call (ALPC) protocol. The WER service exposes a specific ALPC port named WindowsErrorReportingService to facilitate communication with other processes.
According to the researcher’s findings, the vulnerability specifically resides in the SvcElevatedLaunch method, identified as method 0x0D. The WER service fails to properly validate the calling user’s permissions, enabling an attacker to manipulate the service into launching WerFault.exe with custom command-line parameters sourced from a shared memory block.
Exploit Execution Steps
To successfully trigger the exploit, an attacker follows a straightforward sequence of actions:
| Action | Description |
|---|---|
| Create Shared Memory | Create a shared memory block containing an arbitrary, malicious command line. |
| Connect to WER ALPC Port | Establish a local connection to the Windows Error Reporting (WER) ALPC port. |
| Send ALPC Message (Method 0x0D) | Send an ALPC message using method 0x0D, including the client process ID, the shared memory handle, and the exact command-line length. |
| Trigger Command Execution | The WER service duplicates the handle and launches WerFault.exe with the supplied command line. |
Given that the WER service operates at a high-privilege level, the newly spawned process inherits the SYSTEM token. This token encompasses critical permissions, such as SeDebugPrivilege (which allows debugging any process) and SeImpersonatePrivilege (which allows impersonating any user). While it does not grant SeTcbPrivilege to act as part of the operating system itself, the obtained privileges still provide extensive system access.
The vulnerability impacts a wide range of operating systems, including all versions of Windows 10 and Windows 11 prior to January 2026, as well as enterprise server environments running Windows Server 2019 and Windows Server 2022. Microsoft officially addressed this vulnerability in the January 2026 Security Update.
Organizations and system administrators are strongly advised to apply the latest security patches immediately to safeguard their networks. Additionally, security teams should monitor their environments for unusual WerFault.exe child processes and irregular SYSTEM token behaviors to detect potential exploitation attempts.
Follow us on Google News, LinkedIn, and X for daily cybersecurity updates. Contact us to feature your stories.