A new tool named DefenderWrite has emerged, showcasing a method that leverages whitelisted Windows programs to circumvent antivirus protections and write arbitrary files into executable folders. This development raises significant concerns regarding malware persistence and evasion tactics.
Crafted by the cybersecurity expert known as Two Seven One Three, DefenderWrite introduces a unique approach for penetration testers and red teams, allowing them to deploy payloads in highly secured locations without requiring kernel-level access. This innovation underscores the persistent challenges faced by antivirus self-protection mechanisms, which typically guard folders containing AV executables against unauthorized modifications to prevent tampering.
By pinpointing system programs that antivirus vendors have whitelisted for updates and installations, attackers can exploit these exceptions to inject malicious DLLs, effectively turning the antivirus’s own defenses against itself.
Exploiting Whitelisted Programs for Arbitrary Writes
The ingenuity of DefenderWrite lies in its ability to systematically scan Windows executables to identify those authorized to access antivirus folders. The tool enumerates all .exe files within directories such as C:Windows and employs process creation along with remote DLL injection to evaluate write capabilities in protected paths.
A custom DLL is utilized to perform the file write operation and report its success or failure, enabling the tool to identify exploitable processes like msiexec.exe without triggering existing defenses. In tests conducted on Windows 11 24H2 with Microsoft Defender version 4.18.25070.5-0, four programs were identified as vulnerable: msiexec.exe, Register-CimProvider.exe, svchost.exe, and lsass.exe.
For example, by launching msiexec.exe and injecting the DLL, it becomes possible to write a file directly into Defender’s installation directory, a technique successfully demonstrated in controlled lab experiments.
This method is not limited to Microsoft Defender; similar whitelisting vulnerabilities have been observed in other antivirus solutions, including BitDefender, TrendMicro Antivirus Plus, and Avast, although specific details remain undisclosed to promote independent verification.
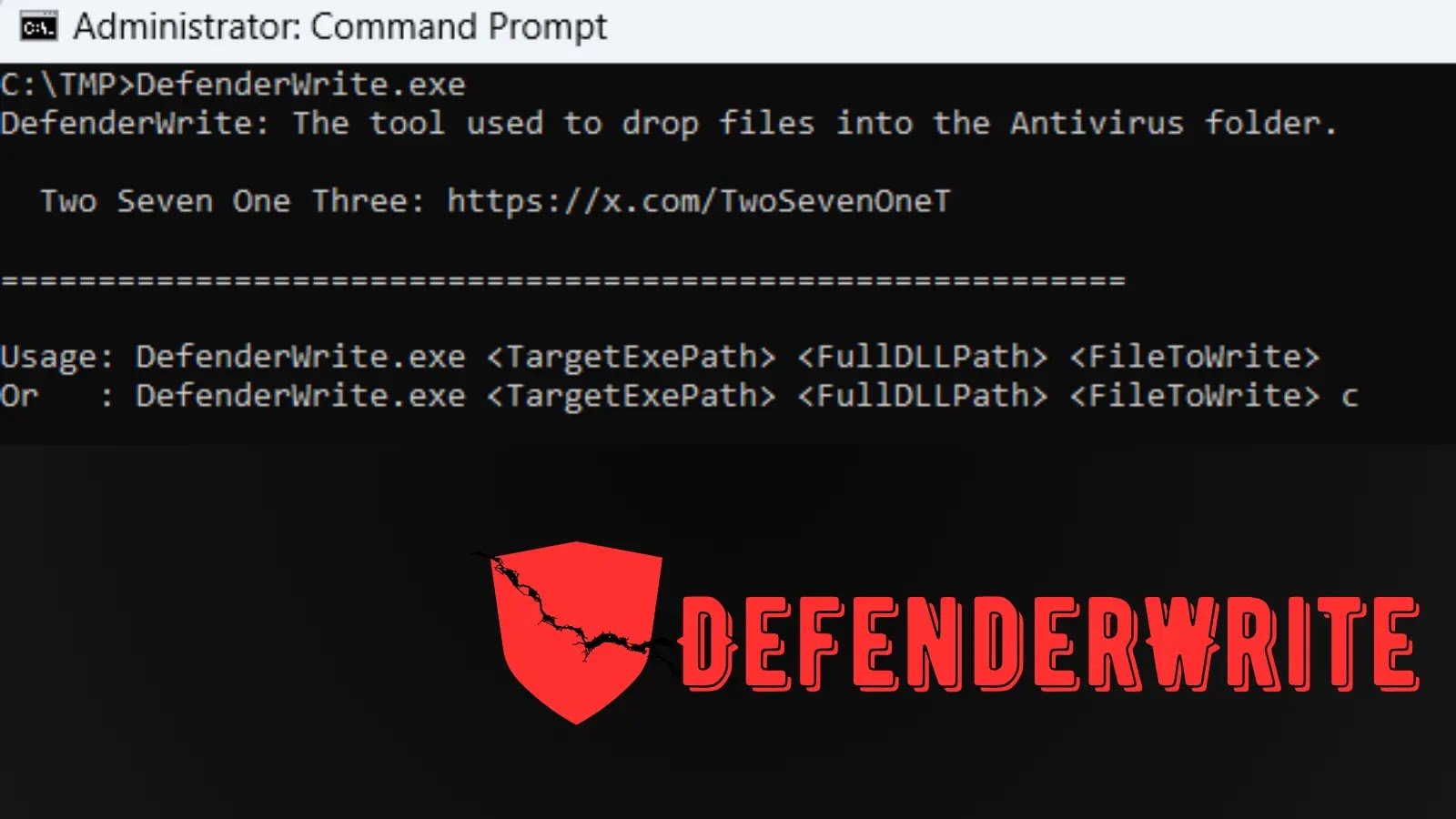
DefenderWrite comes equipped with essential parameters for targeted operations, such as TargetExePath for the host executable, FullDLLPath for the injectable library, and FileToWrite for the destination path within the antivirus folder. An optional “c” flag facilitates the remote copying of the DLL to the specified location.
Additionally, the tool includes a PowerShell script, Run_Check.ps1, which automates the scanning of C:Windows executables and logs those that are whitelisted for potential exploitation. Users have the flexibility to customize this script according to their environment, making it a valuable resource for red team simulations or defensive assessments.
The GitHub repository hosting DefenderWrite provides comprehensive source code and documentation, underscoring the importance of ethical use in authorized testing scenarios. Two Seven One Three, who is active on X as @TwoSevenOneT, shares further insights into penetration testing and encourages community experimentation to bolster antivirus resilience.
Once a malicious payload is placed within an antivirus folder, it benefits from the same protections that shield legitimate files, allowing it to evade scans and potentially establish long-term persistence. This technique highlights the urgent need for antivirus vendors to reassess their whitelisting policies and enhance process isolation during updates. While DefenderWrite does not represent a zero-day vulnerability, it reveals systemic weaknesses that could facilitate real-world attacks if left unaddressed.
Organizations are advised to closely monitor their antivirus update mechanisms and consider implementing layered defenses that extend beyond conventional file permissions. With the tool now publicly available, it is anticipated that its adoption will grow within security research communities, driving the demand for improved protections across widely used antivirus solutions.
Follow us on Google News, LinkedIn, and X for daily cybersecurity updates. Contact us to feature your stories.