Microsoft recently unveiled insights into a significant social engineering campaign dubbed ClickFix, which has been exploiting the Windows Terminal application to initiate a complex attack sequence and deploy the Lumma Stealer malware. This activity, first detected in February 2026, marks a notable shift in tactics, as attackers now guide users to engage with the terminal emulator directly, rather than relying on the traditional method of pasting commands into the Windows Run dialog.
Innovative Attack Techniques
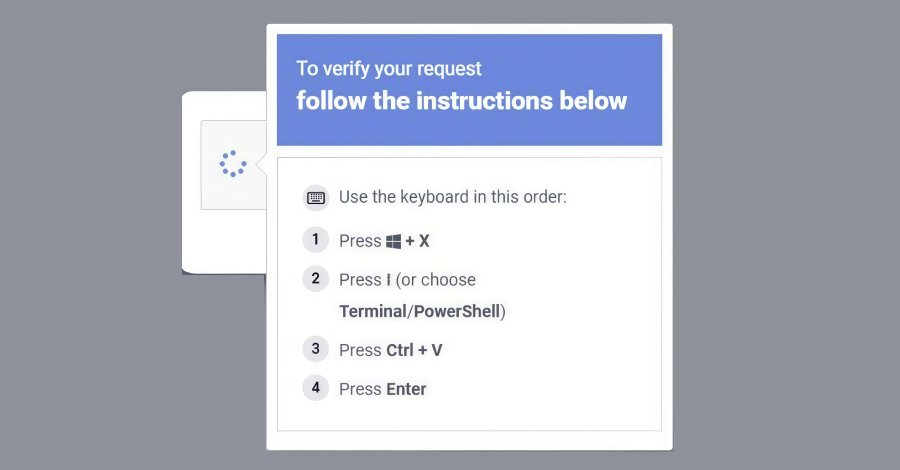
The Microsoft Threat Intelligence team detailed that the campaign instructs targets to utilize the Windows + X → I shortcut to access Windows Terminal (wt.exe). This approach immerses users in a familiar command execution environment, seamlessly blending into legitimate administrative tasks, which enhances its perceived trustworthiness.
What sets this variant apart is its ability to evade detection mechanisms specifically designed to identify misuse of the Run dialog. By leveraging the inherent legitimacy of the Windows Terminal, attackers can manipulate unsuspecting users into executing harmful commands presented through deceptive CAPTCHA pages, troubleshooting prompts, or other verification-style traps.
The post-compromise attack chain is particularly distinctive. When a user pastes a hex-encoded, XOR-compressed command from the ClickFix lure page into a Windows Terminal session, it triggers the opening of additional Terminal and PowerShell instances. This ultimately leads to the invocation of a PowerShell process tasked with decoding the script.
Following this, a ZIP payload is downloaded alongside a legitimate but renamed 7-Zip binary, which is saved with a randomized file name. The utility then extracts the contents of the ZIP file, setting off a multi-stage attack chain that encompasses several critical steps:
- Retrieving additional payloads
- Establishing persistence through scheduled tasks
- Configuring exclusions for Microsoft Defender
- Exfiltrating machine and network data
- Deploying Lumma Stealer using a technique known as QueueUserAPC(), which involves injecting the malware into “chrome.exe” and “msedge.exe” processes
According to Microsoft, the Lumma Stealer specifically targets high-value browser artifacts, including Web Data and Login Data, effectively harvesting stored credentials and transmitting them to infrastructure controlled by the attackers.
Moreover, Microsoft identified a secondary attack pathway. In this scenario, when the compressed command is pasted into Windows Terminal, it triggers the download of a randomly named batch script into the “AppDataLocal” folder via “cmd.exe.” This script writes a Visual Basic Script to the Temp folder (also known as %TEMP%).
The subsequent execution of the batch script through cmd.exe with the /launched command-line argument, followed by its execution via MSBuild.exe, exemplifies the abuse of LOLBins (Living Off the Land Binaries). This script connects to Crypto Blockchain RPC endpoints, suggesting a technique aimed at hiding ether. Additionally, it employs QueueUserAPC()-based code injection into “chrome.exe” and “msedge.exe” processes to extract Web Data and Login Data.