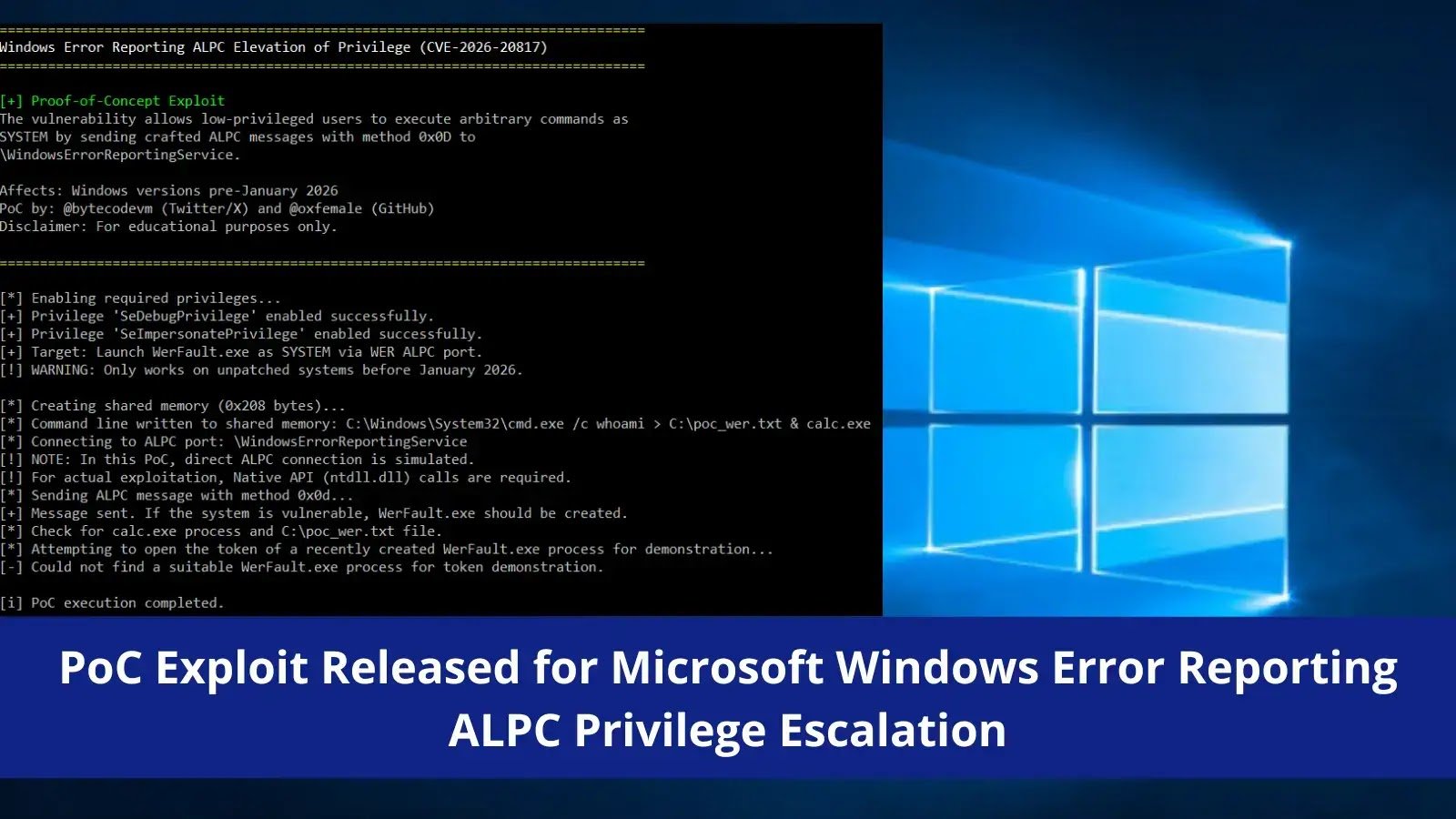
A proof-of-concept (PoC) exploit has recently emerged for CVE-2026-20817, a local privilege escalation vulnerability within the Windows Error Reporting (WER) service. This flaw enables low-privileged users to attain SYSTEM-level access through specifically crafted Advanced Local Procedure Call (ALPC) messages.
Vulnerability Overview
The security researcher known as oxfemale (@bytecodevm) has made a working PoC exploit available on GitHub for CVE-2026-20817, a vulnerability that Microsoft addressed in the January 2026 Patch Tuesday security update. This issue is rooted in wersvc.dll, the primary DLL of the Windows Error Reporting service, which operates under the NT AUTHORITYSYSTEM context and manages crash reports through ALPC ports.
Designated under CWE-280 (Improper Handling of Insufficient Permissions or Privileges), this vulnerability has a CVSS v3.1 base score of 7.8, indicating a significant impact on confidentiality, integrity, and availability.
| Attribute | Details |
|---|---|
| CVE ID | CVE-2026-20817 |
| Severity | High |
| CVSS Score | 7.8 (CVSS v3.1) |
The WER service exposes an ALPC port named WindowsErrorReportingService and facilitates various methods for interprocess communication. The vulnerability is particularly present in the SvcElevatedLaunch method (0x0D), where the service neglects to validate the caller’s privileges before initiating WerFault.exe with user-supplied command line parameters from shared memory.
The exploitation process unfolds in several steps:
- The attacker creates shared memory containing an arbitrary command line (up to 520 bytes).
- A connection is established to the WER ALPC port.
- An ALPC message is dispatched using method 0x0D, which includes the client process ID, shared memory handle, and command line length.
- The WER service duplicates the handle and invokes
ElevatedProcessStart, reading the attacker-supplied command line from shared memory. UserTokenUtility::GetProcessTokenretrieves the WER service’s SYSTEM token, stripping onlySeTcbPrivilegeviaCreateRestrictedToken.CreateElevatedProcessAsUserlaunches the resulting process with SYSTEM privileges and attacker-controlled arguments.
The newly spawned process retains powerful privileges, including SeDebugPrivilege (allowing debugging of any process) and SeImpersonatePrivilege (enabling impersonation of any user), which can facilitate credential theft, persistence, or even complete system takeover.
This vulnerability impacts unpatched versions of the following operating systems:
- Windows 10 (all versions prior to the January 2026 update)
- Windows 11 (all versions prior to the January 2026 update)
- Windows Server 2019 (pre-January 2026 patch)
- Windows Server 2022 (pre-January 2026 patch)
Demonstrations of the PoC have successfully shown exploitation on Windows 11 23H2, where a standard user was able to spawn a SYSTEM-level process via the WER ALPC port.
Detection and Indicators of Compromise
Security teams are advised to monitor for the following indicators:
| Indicator | Event/Source | Recommended Action |
|---|---|---|
| Unusual WerFault.exe or WerMgr.exe spawn with odd command lines | Security Event ID 4688 | Alert and investigate |
| SYSTEM tokens missing SeTcbPrivilege but retaining other elevated privileges | Sysmon Event ID 10 | Investigate immediately |
| Unexpected WER-related arguments or child processes from low-privilege users | Process audit logs | Block and escalate |
| File system changes in WER directories | File integrity monitoring | Review and correlate |
Organizations are urged to apply the January 2026 security patches via Windows Update without delay. If immediate patching is not feasible, a temporary workaround involves disabling the WER service:
sc config WerSvc start=disabled
sc stop WerSvcAdditional hardening measures may include restricting local logon rights to critical systems, implementing application whitelisting policies, monitoring privilege escalation patterns using Sysmon and enhanced process auditing, and validating SYSTEM token integrity across endpoints.
While there have been no confirmed instances of exploitation in the wild, the public availability of a functional PoC significantly heightens the risk of active exploitation.
Follow us on Google News, LinkedIn, and X to Get More Instant Updates. Set Cyberpress as a Preferred Source in Google.