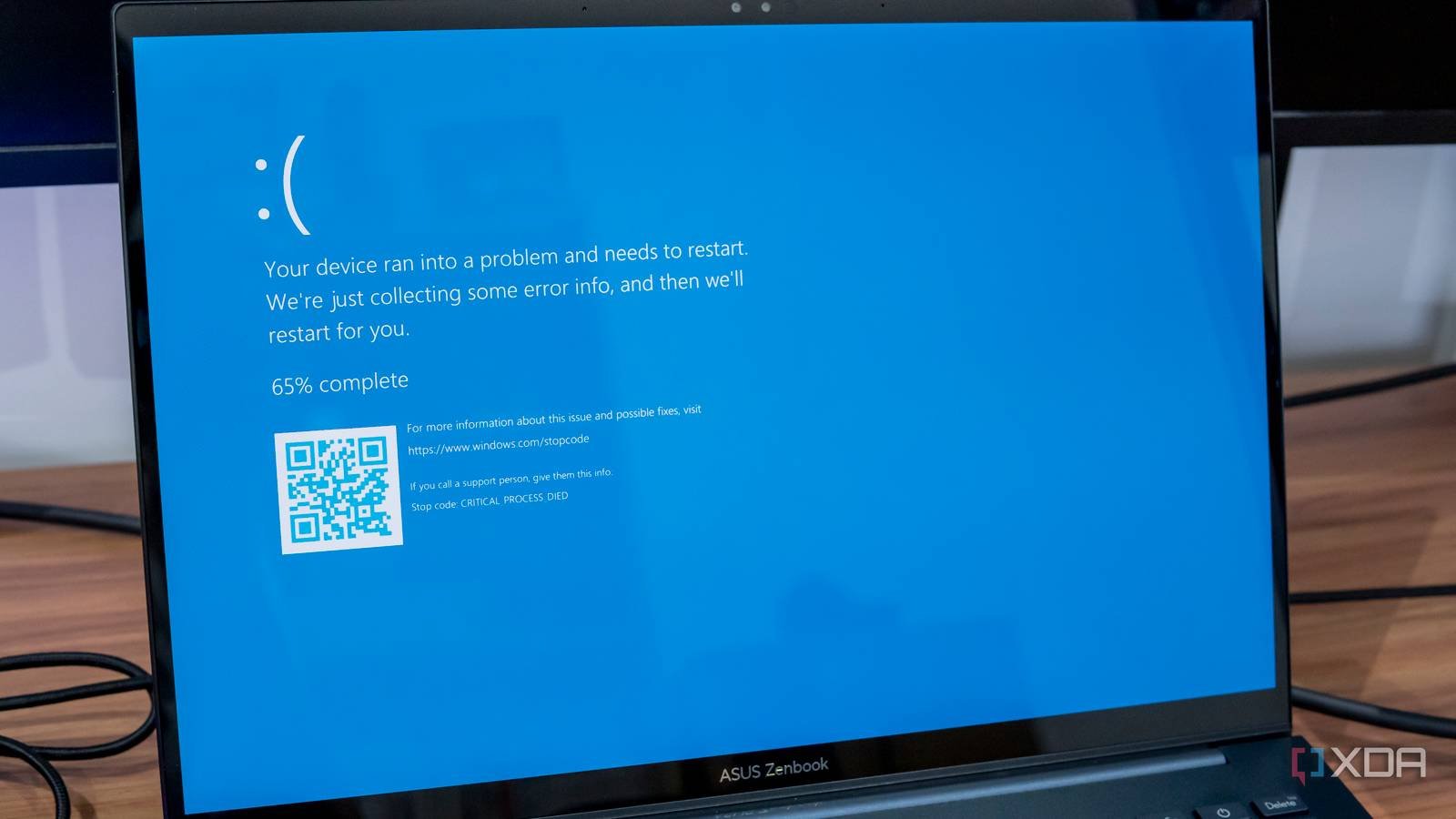
Encountering issues with a Windows PC can quickly become a frustrating experience. The moment the infamous Blue Screen of Death (BSOD) appears, it often feels like the damage is already done. While deciphering a cryptic STOP code may provide some direction, it rarely prevents the problem from escalating. Even in less severe cases, users are often left grappling with peculiar glitches and the daunting task of sifting through Event Viewer logs. This tool, while invaluable for post-crash analysis, can feel overwhelming due to the sheer volume of information it records. Fortunately, Windows offers built-in capabilities that can help users proactively monitor their systems before issues spiral out of control, particularly through the use of Task Scheduler.
Windows debugging shouldn’t be a reactive nightmare
Fight fires at the sight of a spark
Having previously utilized Windows Task Scheduler for basic productivity tasks—like launching work applications at 9 AM—I began to wonder if it could also monitor system events. A brief exploration of its interface confirmed my suspicions. Instead of waiting for a crash to prompt a deep dive into logs, I could configure custom notifications for anomalies as they occurred. While many users are familiar with Task Scheduler’s ability to launch applications at startup, it can also monitor Event Viewer, provided you supply the necessary Event IDs. This combination of Event Viewer and Task Scheduler emerges as a fundamental tool for any serious debugger, and the setup process is surprisingly straightforward once you know the key identifiers.
Numerous third-party system monitoring applications promise to keep an eye on system health and send alerts, but many come with a hefty price tag, often requiring recurring subscriptions. Upon closer examination, it became clear that these tools frequently leverage the same features already embedded in Windows, merely enhancing them with a more polished interface. Rather than spend money on these solutions, I opted to invest a mere 15 minutes into setting up my own system.
How to teach Task Scheduler to watch your back
Hidden in plain sight
To establish an Event Viewer watcher, I opened Task Scheduler and clicked on Create Task (not Create Basic Task), providing a name and description for my task. Next, I navigated to the Triggers tab, selected New, and chose On an event from the Begin a Task dropdown menu. Here, I needed to fill in three fields to pinpoint the relevant Event Viewer entry: Log, Source, and Event ID. The Event ID is crucial, typically identified by reviewing logs after an issue arises, allowing for future tracking. Below are some common Event IDs that have proven invaluable for debugging and security:
| Problem type | Log name | Source | Event ID | Description for debugging |
|---|---|---|---|---|
| Application crash | Application | Application Error | 1000 | A common crash indicator detailing the errant exe or dll name and a memory address in a crash dump. |
| Application hang | Application | Application Hang | 1002 | Details the application that stopped responding to Windows, pointing to the code or third-party module where execution is stuck. |
| Service failure | System | Service Control Manager | 7000 | Details the specific dependency or error code that prevented the Windows service from launching, such as a missing file, registry error, or timeout. |
| Service stopped | System | Service Control Manager | 7036 | An alert for when a critical background process like a database or custom app component stops. |
| Disk/I/O issues | System | Disk or NTFS | 129 | A Reset to device was issued, indicating a storage controller timeout or physical disk issue that can hang applications or corrupt data. |
| Group policy failure | System | Microsoft-Windows-GroupPolicy | 1058 | Windows could not access the GPT.ini file for a Group Policy Object, potentially leading to system misconfiguration, permission issues, and application failures. |
| Driver error | System | Service Control Manager or Kernel-PnP | 7023 | A service or device driver terminated with a service-specific error, or a driver failed to load, suggesting kernel-level component failures. |
| Failed logon | Security | Microsoft-Windows-Security-Auditing | 4625 | A major security event, often indicative of brute-force attempts. |
| User account locked out | Security | Microsoft-Windows-Security-Auditing | 4740 | Indicates potential attack or user error, requiring immediate attention. |
| Audit log cleared | System | EventLog | 1102 | A critical security event—this is often a sign of a cover-up attempt by an attacker. |
| Unexpected system shutdown | System | Kernel-Power | 41 | The system rebooted without cleanly shutting down, indicating a crash or power loss. |
To set up notifications for these triggers, a script is necessary, as Microsoft has deprecated options for sending email alerts and displaying on-screen warnings. Under the Actions tab, I selected Start a program and directed it to a simple custom PowerShell script. This script can perform various tasks; for critical security alerts, such as a failed logon (ID 4625), I created a script that sends me an email. For less critical events, like an application crash (ID 1001), I opted for a script that simply displays an on-screen message. The flexibility of this approach allows for tailored responses, from basic notifications to complex automated fixes.
Spend an afternoon to keep you sane and your system stable
This entire setup results in a robust monitoring system that operates at the OS level on any modern Windows PC. There’s no need for cumbersome, costly third-party applications to enjoy these functionalities. Once the tasks for critical events are configured, users can finally put aside the frantic scrolling through Event Viewer. With a sense of relief, I embraced my custom real-time monitoring solution, which has significantly transformed my debugging experience.