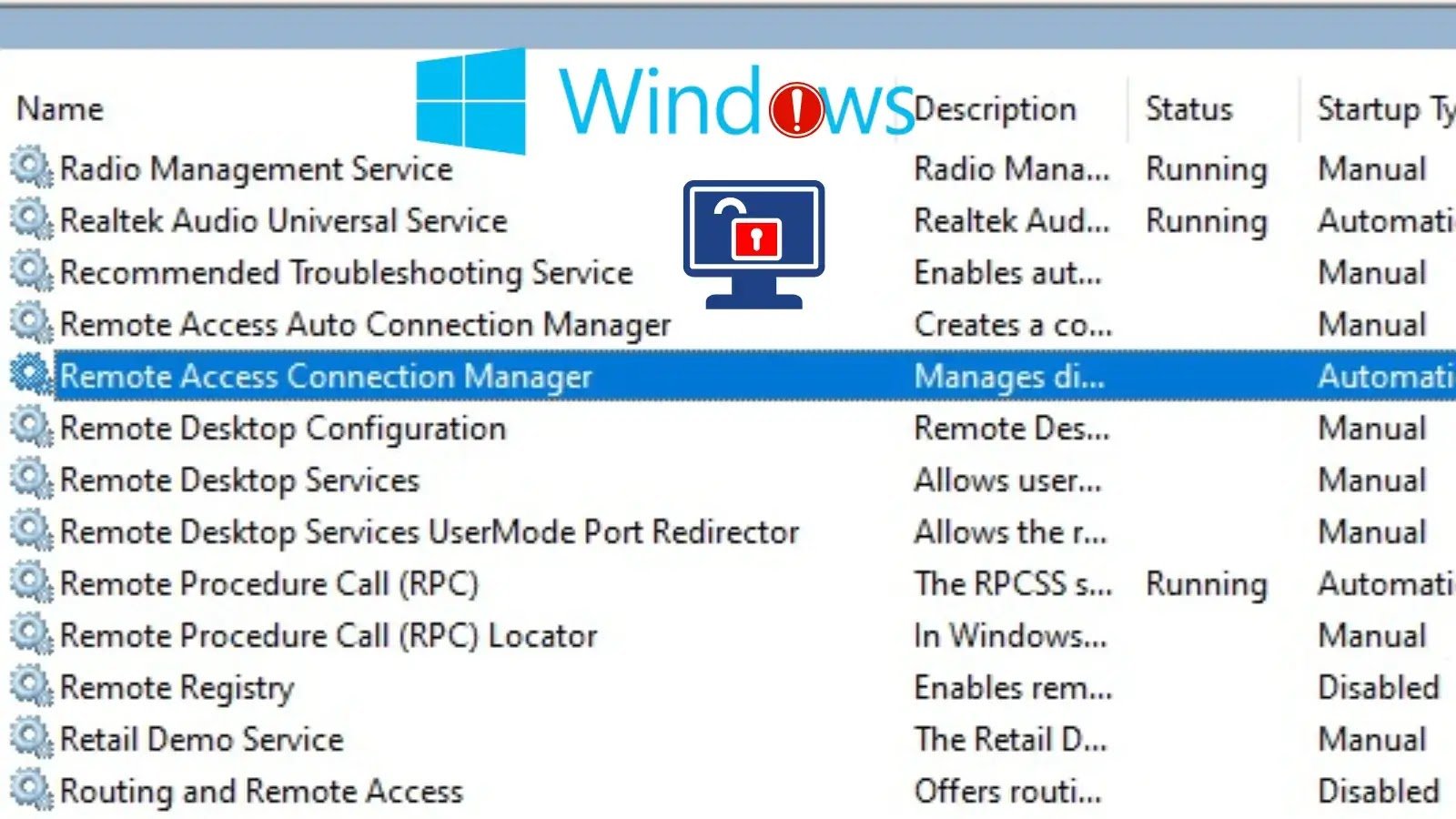
On December 9, 2025, two significant privilege escalation vulnerabilities were unveiled in the Windows Remote Access Connection Manager, identified as CVE-2025-62472 and CVE-2025-62474. These flaws present a serious risk, allowing authorized attackers with minimal privileges to escalate their access to SYSTEM-level permissions on affected systems.
Details of the Vulnerabilities
CVE-2025-62472 is attributed to the mishandling of uninitialized resources within the Remote Access Connection Manager, leading to potential privilege escalation through memory mismanagement. This vulnerability has been assigned a CVSS score of 7.8 and is classified as having Important severity.
In contrast, CVE-2025-62474 arises from inadequate access control mechanisms in the same component, also rated Important with a CVSS score of 7.8. Both vulnerabilities necessitate local access and low user privileges for exploitation, yet once initiated, they require no further user interaction, amplifying their threat in environments where multiple users share systems or where accounts may be compromised.
| CVE ID | Weakness | CVSS Score |
|---|---|---|
| CVE-2025-62472 | CWE-908 (Uninitialized Resource), CWE-416 (Use After Free) | 7.8 |
| CVE-2025-62474 | CWE-284 (Improper Access Control) | 7.8 |
Exploiting either vulnerability grants an attacker complete SYSTEM privileges, representing the highest level of access on Windows systems. Notably, Microsoft has reported no public disclosures or active exploitation of these vulnerabilities as of the announcement date.
The exploitability assessment indicates that CVE-2025-62472 is “Exploitation More Likely,” while CVE-2025-62474 is deemed “Exploitation Less Likely.” This suggests that the uninitialized resource vulnerability may be more straightforward to weaponize, although both vulnerabilities remain in the unproven exploit code maturity stage.
| Operating System | KB Article | Build Number |
|---|---|---|
| Windows Server 2025 | 5072033, 5072014 | 10.0.26100.7462 |
| Windows Server 2022 | 5071547, 5071413 | 10.0.20348.4529 |
| Windows Server 2019 | 5071544 | 10.0.17763.8146 |
| Windows Server 2016 | 5071543 | 10.0.14393.8688 |
| Windows 11 Version 24H2 | 5072033, 5072014 | 10.0.26100.7462 |
| Windows 11 Version 23H2 | 5071417 | 10.0.22631.6345 |
| Windows 10 Version 22H2 | 5071546 | 10.0.19045.6691 |
| Windows 10 Version 1809 | 5071544 | 10.0.17763.8146 |
The vulnerabilities affect a wide range of Windows versions, including Windows Server editions from 2008 to 2025, as well as various Windows 10 and 11 releases. In response, Microsoft has issued security updates across all supported platforms, urging organizations to prioritize patching these vulnerabilities without delay, especially on systems managing sensitive operations or accommodating multiple users.
The prompt availability of official fixes with confirmed remediation levels offers customers essential protection against these privilege escalation threats.
Follow us on Google News, LinkedIn, and X for daily cybersecurity updates. Contact us to feature your stories.