PhantomRPC has emerged as a significant architectural vulnerability within the Windows Remote Procedure Call (RPC) framework, raising concerns for local privilege escalation to SYSTEM-level access across all versions of Windows. This discovery was unveiled by Kaspersky’s application security specialist, Haidar Kabibo, during his presentation at Black Hat Asia 2026 on April 24. The research outlines five distinct exploitation paths, none of which have been addressed with a patch from Microsoft.
Unlike traditional memory corruption bugs or logic flaws confined to a single component, PhantomRPC exploits a fundamental design weakness in the Windows RPC runtime (rpcrt4.dll). This vulnerability arises when the RPC runtime fails to verify the legitimacy of a responding server during an RPC call to an offline or disabled server.
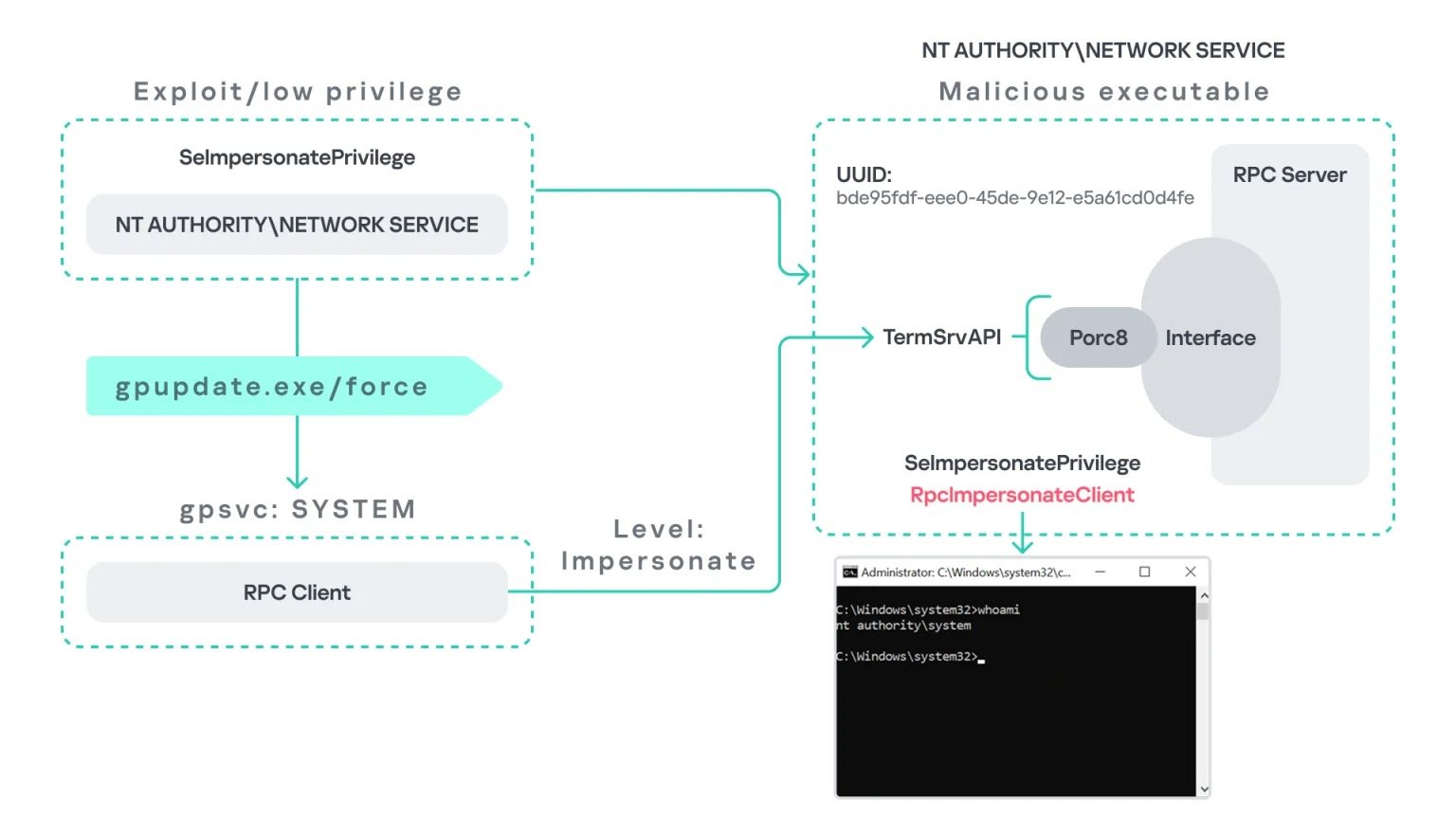
In this scenario, an attacker controlling a low-privileged process, such as one operating under NT AUTHORITYNETWORK SERVICE, can set up a malicious RPC server that masquerades as a legitimate endpoint, intercepting calls intended for the genuine server.
The crux of the exploitation lies in the RpcImpersonateClient API. When a privileged client connects to the fraudulent server with a high impersonation level, the attacker’s server utilizes this API to assume the client’s security context, effectively escalating from a low-privileged service account to SYSTEM or Administrator privileges.
Five Exploitation Paths
Researchers have delineated five specific attack scenarios that highlight the potential risks:
- gpupdate.exe coercion — Executing
gpupdate /forceprompts the Group Policy Client service, running as SYSTEM, to make an RPC call to TermService. If TermService is disabled, the attacker’s counterfeit RPC server can intercept this call, granting SYSTEM-level access. - Microsoft Edge startup — The launch of msedge.exe triggers an RPC call to TermService with a high impersonation level. An attacker positioned with a spoofed endpoint can escalate privileges from Network Service to Administrator without any additional coercion.
- WDI background service — The Diagnostic System Host (WdiSystemHost), which operates as SYSTEM, routinely polls TermService every 5–15 minutes. This automated process allows an attacker to wait for the call without user interaction.
- ipconfig.exe and DHCP Client — Running
ipconfig.exeinitiates an internal RPC call to the DHCP Client service. If DHCP is disabled and a fake server is present, a Local Service attacker can elevate their privileges to Administrator. - w32tm.exe and Windows Time — The Windows Time executable attempts to connect to a nonexistent named pipe
PIPEW32TIME. An attacker can expose this endpoint without disabling the legitimate W32Time service, allowing them to impersonate any privileged user executing the binary.
Microsoft’s Response — No Patch
The vulnerability was reported to the Microsoft Security Response Center (MSRC) on September 19, 2025. Microsoft responded within 20 days, categorizing the issue as moderate severity, citing that the attack necessitates SeImpersonatePrivilege, a privilege already granted by default to Network Service and Local Service accounts. Consequently, no CVE was assigned, and the case was closed without a scheduled fix, according to the Kaspersky report.
In the absence of a patch, organizations are encouraged to implement the following defensive measures:
- Enable ETW-based RPC monitoring to identify
RPCSSERVER_UNAVAILABLEerrors (Event ID 1) in conjunction with high impersonation levels from privileged processes. - Enable disabled services such as TermService where possible, ensuring that legitimate endpoints are occupied and cannot be compromised.
- Restrict SeImpersonatePrivilege to only those processes that absolutely require it, avoiding its allocation to custom or third-party applications.
Kaspersky has made available all tools utilized in this research framework through the PhantomRPC GitHub repository, empowering organizations to audit their environments for potentially exploitable RPC call patterns.
Follow us on Google News, LinkedIn, and X for daily cybersecurity updates. Contact us to feature your stories.