Acronis Threat Research Unit (TRU) has unveiled a comprehensive analysis of the DragonForce ransomware cartel, marking a sophisticated evolution from its predecessors, Conti and LockBit. Emerging in 2023 as a Ransomware-as-a-Service (RaaS) operation, DragonForce has swiftly transitioned into a cartel model, offering white-labeled payloads, customizable encryptors, and a revenue-sharing structure for affiliates. This transformation not only amplifies its operational reach but also complicates efforts to attribute attacks to specific actors.
From RaaS to Cartel: A New Model for Cybercrime
DragonForce’s operations are rooted in the leaked Conti v3 code, showcasing significant overlaps with LockBit Green, particularly in encryption routines, process handling, and backend configurations. By early 2025, the group rebranded itself as the “DragonForce Ransomware Cartel,” enticing affiliates with promises of 80 percent profit shares and dedicated infrastructure support.
This affiliate-driven approach has spawned various ransomware offshoots, including Devman and Mamona, which later rebranded as Global, both utilizing DragonForce’s enhanced encryptor.
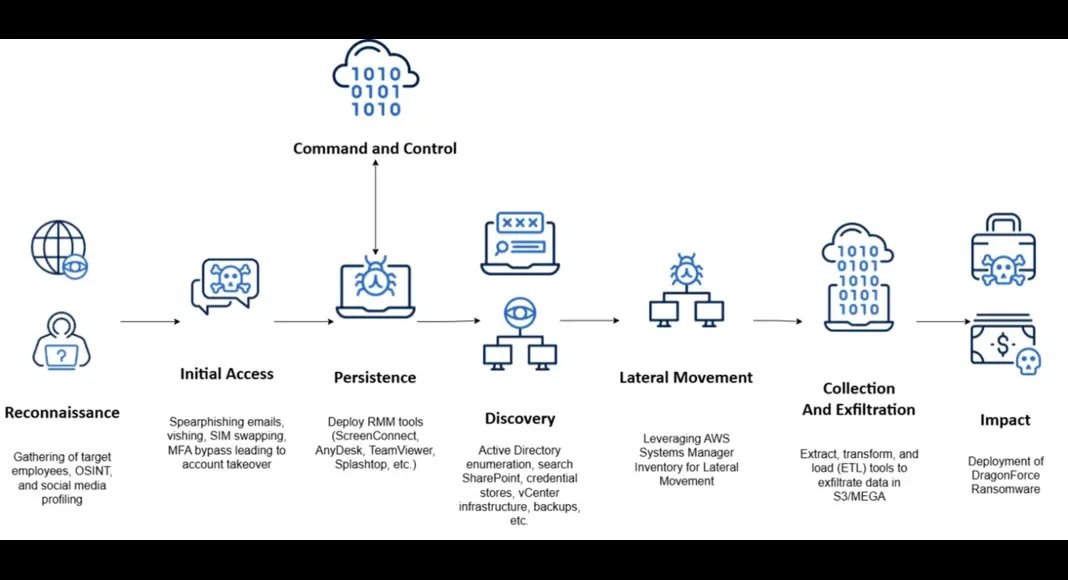
TRU’s report reveals that over 200 victims spanning retail, airlines, insurance, and managed service provider (MSP) sectors have appeared on DragonForce’s leak site since late 2023. The group gained notoriety for its attack on Marks & Spencer, executed in collaboration with Scattered Spider, an initial access broker engaged in phishing, SIM swapping, and multi-factor authentication (MFA) bypass activities. This partnership is part of a broader trend referred to as “Scattered LAPSUS$ Hunters,” linking DragonForce with other threat actors like LAPSUS$ and ShinyHunters in an expanding cybercrime coalition.
Technical Dissection: Conti DNA with BYOVD Capabilities
The analysis of DragonForce samples reveals a clear lineage to Conti, albeit with notable modifications. Developers have transitioned to the MinGW toolchain, resulting in larger binaries that offer unified cross-platform compatibility. Configuration data within these binaries is encrypted using ChaCha20, allowing for customizable extensions, whitelist paths, and encrypted file naming.
A distinctive feature of DragonForce’s latest variant is its incorporation of bring-your-own-vulnerable-driver (BYOVD) techniques. By exploiting signed but vulnerable drivers, such as truesight.sys and rentdrv2.sys, the ransomware can terminate endpoint protection processes by sending system-level control codes via DeviceIoControl APIs. This capability facilitates privilege escalation and evasion of traditional defenses.
Furthermore, the group has enhanced the reliability of its encryption following an article on Habr that exposed vulnerabilities in Akira’s cipher implementation. DragonForce has addressed similar weaknesses, ensuring robust encryption of file headers and content. Files continue to be encrypted with a ChaCha20 key, which is subsequently RSA-encrypted and appended to the file header, mirroring Conti’s structural approach.
The ascent of DragonForce from the remnants of Conti signifies a broader industry shift from isolated ransomware groups to collaborative cybercriminal cartels. Through technical advancements, a focus on recruitment, and strategic partnerships with groups like Scattered Spider, DragonForce has established itself as one of the most active and formidable ransomware ecosystems currently in operation.
Find this Story Interesting! Follow us on Google News, LinkedIn and X to Get More Instant Updates