A recent phishing campaign has emerged, targeting users of messaging applications, prompting alerts from the Cybersecurity and Infrastructure Security Agency (CISA) and the Federal Bureau of Investigation (FBI). This situation underscores a critical reality in cybersecurity: the vulnerability often lies not in the technology itself, but in human behavior.
Phishing Campaign Targeting Messaging Apps Bypasses Encryption
This particular phishing initiative is notable for its approach. Rather than exploiting software vulnerabilities, the attackers are honing in on the users. Evidence indicates that, despite the presence of encryption, thousands of accounts have been compromised worldwide. Once attackers gain access, they can read private messages, access contact lists, and even send messages as the victim, leading to further phishing attempts.
How the Phishing Campaign Works
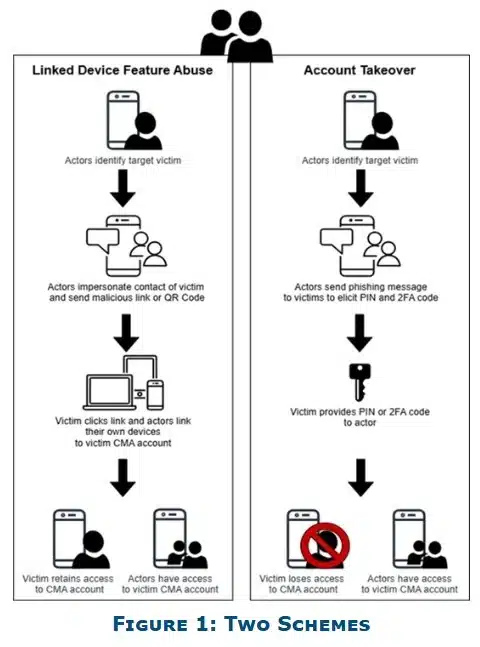
CISA and the FBI have detailed that the phishing campaign primarily employs social engineering tactics. Attackers impersonate official support accounts within messaging platforms, dispatching messages designed to elicit immediate user action. These messages may:
- Encourage users to click on malicious links
- Request verification codes or PINs
- Suggest account “recovery” actions
Should a user comply, attackers can link their device to the victim’s account or seize complete control. In some instances, the attackers escalate their efforts by deploying malware, complicating containment efforts. Notably, platforms like Signal have been specifically targeted, although these tactics can be applied across various messaging applications.
Why This Phishing Campaign Targeting Messaging Apps Matters
The simplicity and scale of this phishing campaign render it particularly alarming. Unlike more complex cyberattacks, phishing requires minimal technical expertise yet achieves high success rates. CISA and the FBI have highlighted this fact, noting that “Phishing remains one of the most unsophisticated, yet effective means of cyber compromise, often rendering other protections irrelevant, including end-to-end encryption.”
Key Recommendations for Users
To mitigate the risks associated with this phishing campaign, authorities recommend that users adopt fundamental yet effective cybersecurity practices:
- Pause before responding: If a message seems suspicious, refrain from engaging or sharing sensitive information.
- Avoid unknown messages: Treat unexpected or unusual requests cautiously, even from known contacts.
- Check links carefully: Do not click on unfamiliar or dubious links.
- Monitor group chats: Be vigilant for duplicate or fake accounts in conversations.
- Use built-in security features: Enable protections such as message expiration where applicable.
- Report incidents quickly: Notify security teams or report to authorities like the Internet Crime Complaint Center (IC3).
Users should also remember that legitimate support services will never request verification codes or send account recovery links via direct messages.
A Persistent Cyber Threat That Relies on Human Behavior
The reliance of this phishing campaign on human behavior, rather than technical vulnerabilities, is particularly concerning. Attackers exploit urgency, confusion, and trust—elements that technology alone cannot address. The warnings from CISA and the FBI emphasize the necessity for users to remain vigilant. Strengthening personal cybersecurity practices is now as crucial as the security features embedded within the platforms themselves. As messaging applications continue to be integral to both personal and professional communications, this campaign serves as a poignant reminder that the weakest link in cybersecurity is often the user.