A new proof-of-concept tool, unveiled on January 11, 2026, showcases a sophisticated method by which attackers can inhibit the launch of antivirus and endpoint detection and response (EDR) solutions during the Windows startup process. This tool, named EDRStartupHinder, exploits the Windows Bindlink API and the Protected Process Light (PPL) security mechanisms, marking a notable advancement in the ongoing battle between security software and malicious actors.
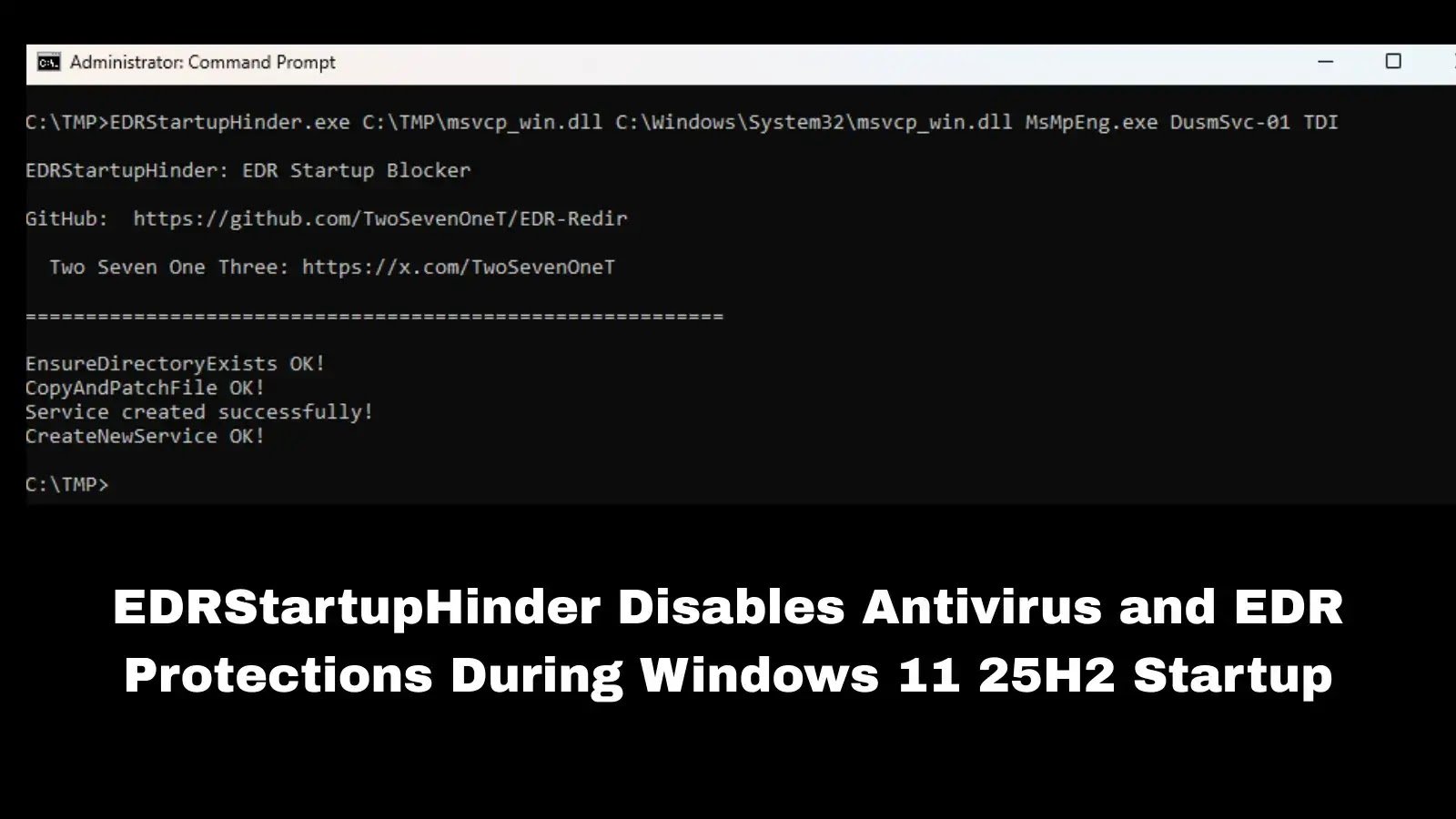
Security researcher Two Seven One Three has developed EDRStartupHinder to effectively block Windows Defender and various commercial security products on Windows 11 25H2 systems. The tool achieves this by redirecting essential system DLLs during the boot sequence, thereby manipulating the Windows bindflt.sys driver.
Technical Attack Methodology
EDRStartupHinder employs a complex four-step attack chain that capitalizes on inherent vulnerabilities within the Windows architecture. The initial step involves creating a malicious service that is configured to launch prior to the targeted security services by adjusting Windows service group priorities.
Subsequently, the tool utilizes the Bindlink API to redirect critical DLLs from the System32 folder—essential for the operation of all Windows processes—to locations controlled by the attacker. The effectiveness of this attack lies in its ability to exploit the protective measures of EDR software.
When an EDR process, which operates under PPL protection, attempts to load a redirected DLL, it encounters an invalid signature due to EDRStartupHinder modifying a single byte in the PE header. As a result, PPL-protected processes refuse to load unsigned DLLs, leading the security software to terminate itself rather than risk operating in a compromised state.
Following the exit of the targeted security process, EDRStartupHinder removes the malicious redirect, ensuring system stability and maintaining a low profile. This cleanup operation allows other Windows processes to continue functioning normally while the security software remains disabled.
Successful execution of this tool necessitates thorough reconnaissance of target systems. Attackers must utilize tools such as Process Monitor and Process Explorer to identify critical DLLs that security products load during startup, particularly those not included in the Windows KnownDLLs registry list, to avoid preloading them into memory.
Additionally, attackers need to ascertain the service group of the targeted EDR software by scrutinizing the ServiceGroupOrder registry key, subsequently configuring their malicious service with a higher priority. A demonstration against Windows Defender revealed that MsMpEng.exe loads msvcp_win.dll at startup, and that services in the TDI group initiate before Defender.
In laboratory tests, EDRStartupHinder successfully prevented Windows Defender from launching on Windows 11 25H2 systems. The researcher also confirmed its effectiveness against several unnamed commercial antivirus and EDR products, opting not to disclose specific vendor names to avert premature exploitation before defensive measures could be established.
This latest attack builds upon the researcher’s previous work with Bindlink exploitation, including EDR-Redir tools that redirected security software folders post-launch. However, EDRStartupHinder signifies a more foundational attack by targeting System32 before security services are initialized, thereby bypassing vendor-implemented folder protection mechanisms.
Security teams can detect this attack vector by monitoring Bindlink activity through bindlink.dll usage, tracking unauthorized Windows service creation, and implementing defense-in-depth strategies. System administrators are advised to establish baseline monitoring for registry modifications related to service groups and startup configurations.
The source code for EDRStartupHinder is publicly accessible on GitHub, raising concerns about its potential weaponization by threat actors. Organizations operating Windows 11 environments with endpoint security solutions are urged to enhance monitoring for service manipulation and DLL redirection activities as immediate defensive measures.
This disclosure underscores the persistent challenges in securing privileged system processes and highlights the potential for security mechanisms like PPL to be turned against the very products they are designed to protect. As of now, Microsoft has not issued any public statements regarding patches or mitigations for this attack technique.
Follow us on Google News, LinkedIn, and X to Get More Instant Updates. Set Cyberpress as a Preferred Source in Google.