A vulnerability has been identified in Microsoft’s newly integrated Rust-based kernel component for the Graphics Device Interface (GDI) within Windows. This flaw has the potential to trigger a system-wide crash, commonly known as a Blue Screen of Death (BSOD), which brings to light the complexities involved in incorporating memory-safe programming languages into critical operating system components.
Despite Microsoft categorizing the issue as moderate in severity, it raises significant concerns, particularly in enterprise settings where malicious actors could exploit it for widespread disruption. The vulnerability was discovered during a focused fuzzing campaign conducted by Check Point, aimed at identifying weaknesses within Windows’ graphics subsystem. Fuzzing is a testing technique that bombards software with malformed inputs to uncover bugs, and it proved to be a crucial method in this instance.
Utilizing tools such as WinAFL and WinAFL Pet in a controlled test environment, researchers directed their efforts towards the Enhanced Metafile Format (EMF) and EMF+ files. These files, which provide instructions to GDI for rendering 2D graphics, have historically been a target for exploits due to their intricate structures. Starting with merely 16 seed files, the fuzzers quickly revealed a range of crashes, from information leaks to potential code execution risks within user-space components.
The pivotal moment came unexpectedly when repeated system restarts following BugChecks indicated a kernel-level issue. This phenomenon was dubbed a “Denial of Fuzzing” condition, which halted testing and necessitated a shift towards kernel forensics.
Windows Rust-based Kernel GDI Vulnerability
To pinpoint the source of the issue, Check Point enhanced its setup with memory dump analysis using MemProcFS and Volatility, which allowed them to extract mutated files from RAM disks. Through iterative refinement of their corpus, they successfully reduced the time required to reproduce the issue from several days to just 30 minutes across 836 samples.
A clever modification to their harness enabled the streaming of mutations to a remote server via a custom C function and Python listener, ultimately capturing the critical 380,000th mutation that triggered the crash. In-depth analysis revealed the bug resided in win32kbasers.sys, Microsoft’s Rust-rewritten driver for GDI regions. The flaw occurred during the path-to-region conversion in NtGdiSelectClipPath, where an out-of-bounds array access in regionfrompathmut() invoked Rust’s panicboundscheck(), leading to a SYSTEMSERVICEEXCEPTION.
The root cause was traced back to a malformed EmfPlusDrawBeziers record, characterized by mismatched point counts (17 points declared as 4) and irregular coordinates, compounded by a wide-stroke pen from an EmfPlusObject. This malformed geometry placed undue stress on edge block handling, resulting in a breach of bounds within the singly linked list representation.
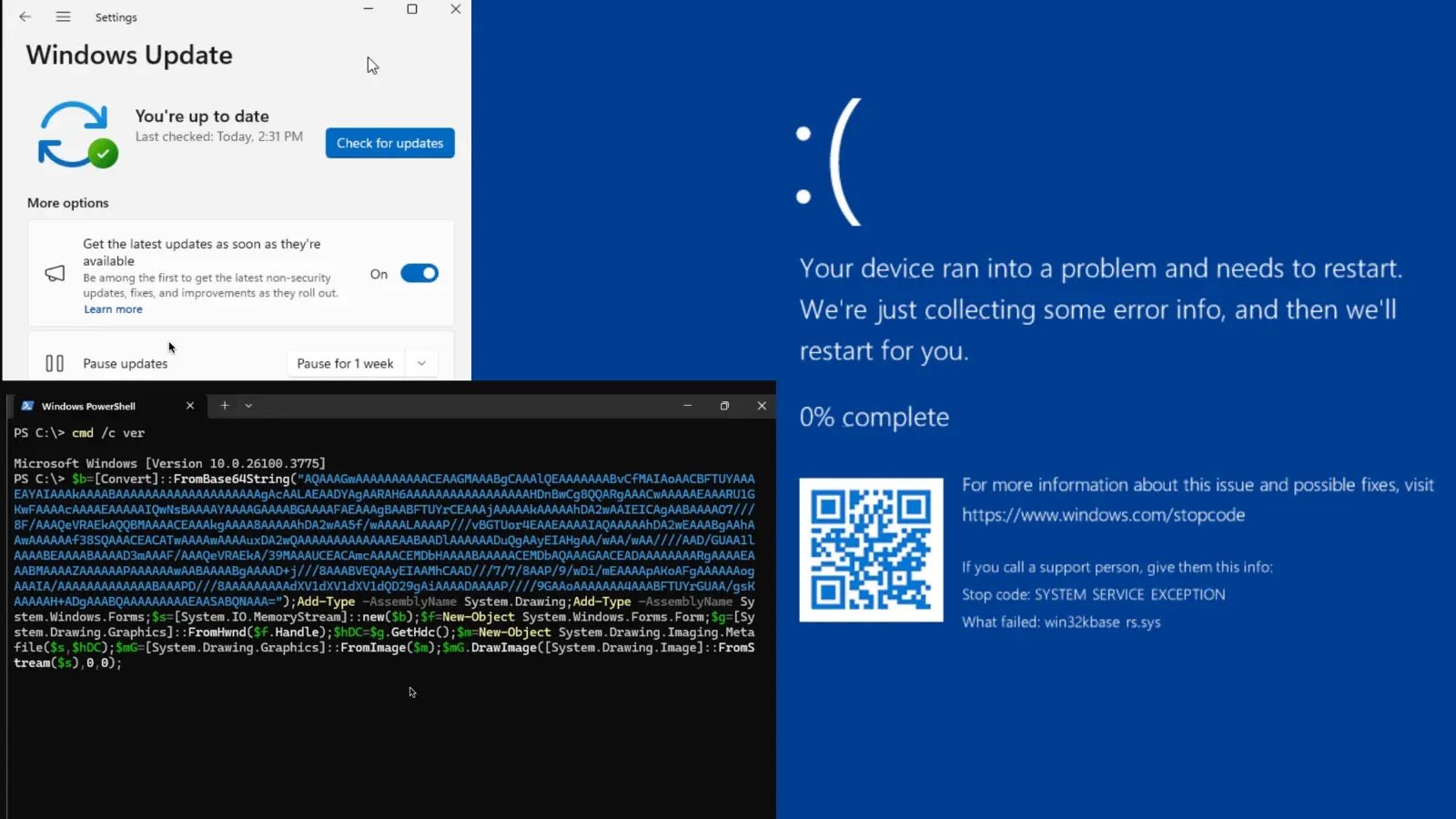
A straightforward PowerShell proof-of-concept illustrated the exploit’s accessibility: embedding the crafted metafile in a Graphics object via System.Drawing resulted in an immediate BSOD, even from low-privilege sessions on x86/x64 Windows 11 24H2. While it did not facilitate direct remote code execution, it posed a significant denial-of-service threat—imagine an insider orchestrating crashes across an enterprise on a Friday evening.
Microsoft addressed the flaw in OS Build 26100.4202 through the KB5058499 preview released on May 28, 2025, which expanded the driver by 16KB and introduced hardened logic. Key modifications included the addition of dual edge-handling routines: addedgeoriginal() and a bounds-checked addedgenew(), controlled by a feature flag. The full rollout followed in June, although initial testing indicated that the flag was disabled.
Check Point promptly reported the vulnerability; however, Microsoft’s MSRC classified it as a non-critical denial-of-service issue, asserting that Rust’s panic mechanism functioned as intended. This incident marks one of the first publicly acknowledged Rust kernel bugs since its integration, which was heralded at BlueHat IL 2023 for enhancing security. While Rust effectively mitigates overflow issues, it does not eliminate design flaws or incomplete testing. As Windows continues to embrace memory safety, such occurrences serve as a reminder to developers that language alone cannot resolve all vulnerabilities. Comprehensive fuzzing and validation processes remain essential to prevent “alarm systems that blow up the house.”
Follow us on Google News, LinkedIn, and X for daily cybersecurity updates. Contact us to feature your stories.