Folder permissions in Windows 11 serve as the gatekeepers of your files, determining who can read, modify, or delete them. Think of them as diligent security guards, ensuring that only authorized individuals gain access. Typically, these guards operate quietly in the background, maintaining order without drawing attention. However, when they malfunction, the disruption is unmistakable. Fortunately, resolving these issues is entirely feasible, and you don’t need to be a system administrator to do so. Let’s explore the common pitfalls and the steps to rectify them.
Quick Reference: Which Method Should You Use?
This guide outlines several methods to address folder permission issues, allowing you to choose the most suitable approach for your situation:
- If you’re facing issues with a single folder and prefer a graphical interface, begin with Method 1 (Security Tab) or Method 2 (Take Ownership). These methods are user-friendly and carry minimal risk.
- For multiple folders or if you require a scriptable solution, opt for Method 3 (icacls in Command Prompt), which is both efficient and powerful.
- Method 4 (PowerShell) caters to advanced users seeking conditional logic, such as resetting permissions based on specific file types.
- Method 5 (Windows Reset) is the last resort, recommended only when the entire permission structure is beyond repair.
Why Folder Permissions Break in the First Place
Folder permission issues can arise from various factors, with the most prevalent being drive or file migration. When files are transferred from another PC, an old hard drive, or a backup, they retain the original owner’s Security Identifier (SID). Since this SID is absent on your current machine, Windows blocks access entirely.
Windows updates can also inadvertently reset or overwrite permissions, particularly in system-adjacent folders. Additionally, malware may lock you out of folders to prevent the deletion of malicious files. Sometimes, the issue is self-inflicted; a user may inadvertently alter permissions, losing their own access in the process. Such scenarios are not uncommon, even among IT professionals.
The symptoms of permission issues are typically consistent: “Access Denied” messages on files you own, application crashes due to inability to access configuration directories, and ownership displayed as “unknown” or an unresolvable SID string in the Security tab. Now, let’s delve into the solutions.
Method 1: Reset Permissions Through the Security Tab
This method is the most straightforward approach in Windows for resetting folder permissions to their default state by discarding any custom settings.
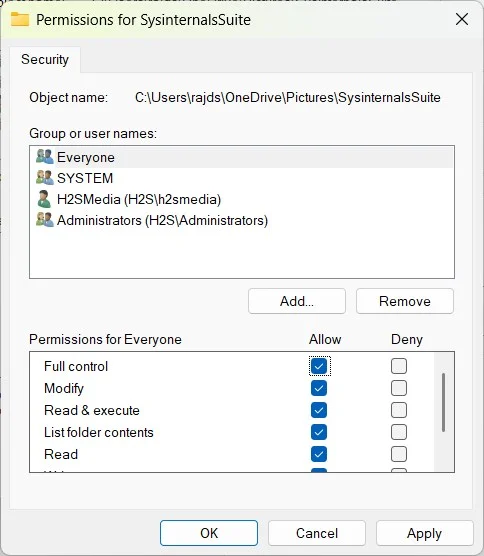
First, verify your account’s basic access level. Click Edit to modify permissions. If your username is listed, select it and ensure that Full Control or at least Read & Execute, List folder contents, Read, and Write are checked under the “Allow” column. If your username isn’t listed, click Add, input your username, hit Check Names to verify, and then click OK. Assign the appropriate permissions for your newly added account and click Apply and OK to close the Edit window.
Next, navigate to the Advanced section of the Security tab. Here, you’ll find a detailed list of permission entries, showing each user, their access type (Allow or Deny), and the scope of that permission.
Ensure your user account appears in this list. If it’s missing, click Add, then Select a principal, type your username, click Check Names, and confirm. Set the “Applies to” dropdown to This folder, subfolders, and files, check Full control under Basic permissions, and click OK.
Finally, enable the checkbox labeled “Replace all child object permission entries with inheritable permission entries from this object” at the bottom of the Advanced Security Settings window. Click Apply and confirm the dialog. This action forces Windows to cascade the updated permissions throughout every subfolder and file within the directory, effectively resolving issues caused by broken inheritance or missing user entries.
Method 2: Take Ownership, Then Reset
In some cases, the Security tab may not allow any modifications, displaying an error when you attempt to click Edit. This often indicates that the folder’s owner is set to an account that no longer exists on your machine.
To regain control, you must first claim ownership. Open the Properties > Security > Advanced window. At the top, you’ll see the current Owner, which may appear as a lengthy SID string instead of a recognizable username. Click Change next to it.
In the “Select User or Group” dialog, enter your username and hit Check Names. Windows will resolve it to the full account path. Alternatively, if you wish to assign ownership to the entire Administrators group, type Administrators instead. Click OK.
Back in the Advanced Security Settings, enable “Replace owner on subcontainers and objects” to apply ownership recursively to everything within the folder.
Next, check the permission entries list in the same Advanced Security Settings window. After changing ownership, your account may still lack an explicit permission entry. If your username is absent, click Add, select principal, type your username, click Check Names, and confirm. Set “Applies to” to This folder, subfolders, and files, and grant Full control. Click OK.
Lastly, enable “Replace all child object permission entries with inheritable permission entries from this object” to reset permissions across the entire directory tree. Hit Apply. For larger folders containing thousands of files, this process may take a few minutes. Allow it to complete without interruption to avoid creating a partially-reset state that complicates matters further.
Method 3: Reset Folder Permissions Using Command Prompt
This method is my preferred choice for most permission resets. It’s quicker than navigating through the GUI, effectively handles deeply nested directory trees, and allows for command scripting for repeated use.
Begin by opening Command Prompt as Administrator — press Win + S, type cmd, right-click Command Prompt, and select Run as administrator. The administrative elevation is crucial, as these commands won’t function from a standard prompt.
First, claim ownership by using the exact path of the folder whose permissions you wish to change or reset:
takeown /F "C:PathToFolder" /R /D YThe /F flag specifies your target folder, /R makes it recursive, and /D Y auto-confirms every prompt, saving you from repetitive confirmations for large directories.
Next, reset the permissions to their inherited defaults:
icacls "C:PathToFolder" /reset /T /CHere, /reset removes custom permissions and restores inheritance from the parent folder. The /T flag applies this recursively to every file and subfolder, while /C instructs icacls to continue despite errors on specific files, preventing the entire operation from halting.
If you need to explicitly grant yourself full control afterward:
icacls "C:PathToFolder" /grant %username%:F /TThe %username% variable automatically fills in your current account name, and :F assigns Full Control. While this third command is not always necessary, it serves as a backup if a folder still shows restricted access after the reset.
Optionally, you can grant the Administrators group access as well:
icacls "C:PathToFolder" /grant Administrators:F /TThis is particularly useful on shared machines or when running applications under different admin accounts. Executing these commands in sequence ensures comprehensive coverage of ownership, inheritance reset, and explicit user access.
Method 4: Use PowerShell for Advanced Permission Resets
PowerShell offers programmatic control that surpasses what icacls can provide. While it introduces more complexity, this method is ideal for scenarios requiring conditional logic or fine-grained filtering.
Open Windows Terminal as Administrator (right-click the Start button > Terminal (Admin)) and execute:
$targetPath = "C:PathToyour-Folder"
$acl = Get-Acl $targetPath
$acl.SetAccessRuleProtection($false, $false)
Set-Acl $targetPath $aclThis sequence retrieves the folder’s current access control list and disables the permission protection flag, re-enabling inheritance from the parent. The changes are then applied back to the folder.
To extend this across an entire directory tree:
Get-ChildItem -Path "C:PathToYour-Folder" -Recurse | ForEach-Object {
$acl = Get-Acl $_.FullName
$acl.SetAccessRuleProtection($false, $false)
Set-Acl $_.FullName $acl
}PowerShell excels in scenarios where you need to reset permissions selectively, such as targeting only .docx files modified within the last 30 days. For a straightforward reset of everything in a folder, however, icacls from Method 3 remains the more efficient option.
Method 5: Windows Reset as a Last Resort or Option
When system-wide permissions are so compromised that Windows exhibits erratic behavior—settings won’t open, applications fail to install, or services crash—a system reset may be the only viable solution.
To initiate a reset, navigate to Settings > System > Recovery and click Reset this PC. Choose the “Keep my files” option, which reinstalls Windows 11 and restores default system permissions while preserving your personal files in user folders. It’s advisable to back up critical data before proceeding, as all installed applications will be removed and will require reinstallation.
Protecting Yourself: Tips for the Future
To safeguard against future permission mishaps, consider the following:
- Back up permissions before making manual edits. Execute
icacls "C:PathToFolder" /save permissionsbackup.txt /Tprior to changes. If issues arise, restore them withicacls "C:Path" /restore permissionsbackup.txt. - Understand the distinction between NTFS and share permissions. NTFS permissions apply at the file system level, enforced regardless of access method, while share permissions activate only during network access.
- Avoid altering system folders. Directories like
C:WindowsandC:Program Filesare protected for good reason. Modifying their permissions can lead to significant system instability.
Troubleshooting: When the Fix Doesn’t Work
Should you encounter persistent “Access Denied” messages after resetting permissions, the most common cause is not running Command Prompt or PowerShell as an administrator. Ensure you are using an elevated session and verify that your user account is a member of the Administrators group.
If a folder remains locked after taking ownership, check if the owner is set to TrustedInstaller. In this case, you’ll need to change ownership from TrustedInstaller to your account first, then reset permissions.
If icacls generates errors during the process, ensure you’re including the /C flag to continue past individual file errors. If errors are widespread, the file system may be damaged. Running sfc /scannow followed by DISM /Online /Cleanup-Image /RestoreHealth can help rectify this before retrying the permission reset.
Lastly, if permissions revert unexpectedly, investigate whether Group Policy is overriding your changes, particularly in corporate environments. Sync tools like OneDrive can also alter permissions during sync conflicts, as can antivirus software on flagged folders.
Frequently Asked Questions
How do I reset permissions for all folders in Windows 11? Open an elevated Command Prompt and execute icacls "C:TargetFolder" /reset /T /C. The /T flag ensures the reset applies recursively to every file and subfolder within the specified directory.
Is it safe to reset folder permissions? Generally, yes for personal folders; it’s often necessary. However, exercise caution with system directories like C:Windows, as incorrect permissions can lead to instability.
What is the icacls command in Windows? It stands for “Integrity Control Access Control List.” This built-in command-line utility allows you to view, modify, back up, and restore file and folder permissions, replacing the older cacls command since Windows Vista.
Why do folder permissions keep changing? Common reasons include Windows updates modifying system permissions, antivirus software restricting access to quarantined files, syncing tools altering permissions during conflicts, and group policy changes enforced by network administrators.