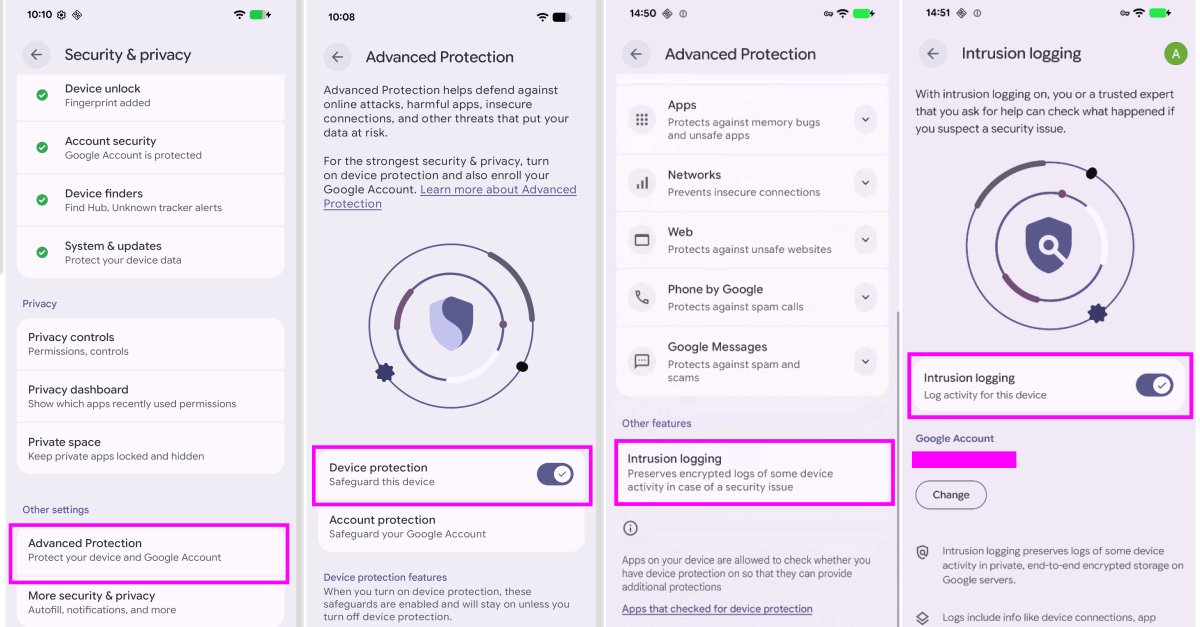
On Tuesday, Google introduced a new opt-in feature for Android users, known as Intrusion Logging, designed to enhance the analysis of sophisticated spyware attacks. This feature is part of the Advanced Protection Mode and aims to provide persistent, privacy-preserving forensic logging that can be invaluable in investigating potential device compromises.
Developed in collaboration with Amnesty International and Reporters Without Borders, Intrusion Logging captures daily device and network activities, offering insights into device behavior and the applications in use. The types of activities recorded include:
- App activity, such as the initiation of app processes
- Installations, updates, and uninstalls of applications
- Network connections, including Wi-Fi and Bluetooth activity, DNS lookups, and IP addresses
- File transfers via USB
- Modifications to system certificates
- Device lock and unlock events
Google ensures that the log data is safeguarded through end-to-end encryption, stored securely on its servers. The encryption keys are protected by the user’s Google Account password and screen lock credentials, preventing access by third parties, including Google itself, except for the device owner.
Reporters Without Borders emphasized the security of this data, stating, “By storing the data on a secure server, even malware installed on the smartphone cannot access, delete, or manipulate it.” The organization further noted that the Intrusion Logging feature facilitates the detection and forensic analysis of advanced attacks that may have previously gone unnoticed.
The encrypted logs are retained for a period of 12 months, after which they are automatically deleted. Users are unable to delete the logs before this expiration, even if they deactivate the feature or close their account. However, they do have the option to download the logs for offline storage if they wish to retain them longer. Google cautions that once these logs are downloaded and decrypted, users bear responsibility for their security, particularly in legal contexts where access to decrypted data may be mandated.
It is important to note that Intrusion Logging also records network events during Chrome’s Incognito mode, such as DNS lookups and IP connections, as it functions at the system level without differentiating between browsing modes. Consequently, while decrypted logs can reveal visited websites, they do not specify the exact pages accessed.
This feature is particularly beneficial for high-risk individuals who suspect they may be targets of advanced surveillance. By sharing their activity logs with trusted security experts, they can facilitate detailed examinations of potential threats.
To access the logs, users can navigate through the Settings app: Security & privacy -> Advanced Protection -> Intrusion Logging -> Access logs. The rollout of this feature is currently underway for devices running the Android 16 December update and newer.
Other Privacy and Security Features Coming to Android
In addition to Intrusion Logging, Google has announced a series of privacy and security enhancements. Among these is a verified financial call feature aimed at combating scams where fraudsters impersonate banks to extract sensitive information from users. When a call appears to originate from a participating bank, Android will verify the legitimacy of the call through the installed banking app. If the app confirms no such outreach is occurring, the call will be terminated automatically.
Other noteworthy updates include:
- Expansion of Live Threat Detection to warn users about suspicious app behaviors, such as SMS forwarding typically exploited by banking trojans.
- Evaluation of downloaded APK files via Chrome for known malware before installation, provided Safe Browsing is enabled.
- Revocation of accessibility services API access from apps not designated as accessibility tools.
- Disabling device-to-device unlocking and Chrome WebGPU support.
- Implementation of scam detection for chat notifications.
- Enhancements to Find Hub’s Mark as Lost feature, allowing for biometric locking of devices marked as lost, thus preventing unauthorized access to tracking features.
- Reduction of the number of PIN or password guesses allowed for third parties with physical access to a device, along with longer wait times between failed attempts.
- Improved device recovery options, making the IMEI number accessible via the lock screen on devices running Android 12 or higher.
- Enhanced privacy controls enabling users to share precise location data temporarily and grant specific contact access to third-party apps.
- Introduction of AISeal with pKVM for isolated processing of AI-related data on-device.
- Expansion of Binary Transparency in Android to verify the integrity of official builds and maintain a public ledger for Google apps and foundational GMS APIs.
- Protection against OTP theft by hiding SMS one-time passwords from most apps for three hours.
- Empowerment of carriers to disable 2G services by default to mitigate vulnerabilities associated with legacy technology.
- Strengthening data protection through the introduction of post-quantum cryptography to guard against future threats.
- Implementation of explicit user controls for opting in and out of features, security guardrails, and transparency when using Gemini on Android.
Eugene Liderman, director of Android security and privacy, stated, “By improving protections against banking scams and extending powerful protections like Live Threat Detection and Android Advanced Protection, we are ensuring that Android remains the most secure platform.”