In the ever-evolving landscape of mobile technology, the permissions granted to applications on Android devices warrant careful consideration. Users often overlook the potential risks associated with granting extensive access to apps, which can lead to serious security vulnerabilities. For instance, when an app is permitted to access accessibility features, it can perform actions such as hacking passwords, executing transactions, and altering device settings without the user’s explicit consent. This can create an environment where malware proliferates undetected, as untrusted applications can approve changes autonomously.
While some applications genuinely require these permissions to enhance the user experience—particularly for individuals with hearing impairments or visual challenges—it’s crucial to exercise discernment. Apps unrelated to accessibility, such as games or unfamiliar downloads, should not be granted such permissions. To review which applications currently have accessibility access, navigate to the Android Settings, select Accessibility, and tap on Installed apps or Installed services. If you identify any applications that should not have this access, simply disable the toggle for those apps.
Overlay or Appear on Top
Another permission that demands scrutiny is overlay access, often labeled as “Appear on top,” “Display over other apps,” or “Draw over other apps.” This permission allows applications to display content over other active applications. While this functionality can be beneficial—for example, a messaging app using it to show chat bubbles—granting it to suspicious apps poses a significant risk. Malicious applications can exploit this access to overlay fake login screens on banking or social media apps, potentially tricking users into divulging sensitive information or downloading harmful files.
To verify which apps currently possess overlay permissions, go to Settings, select Apps, tap the ellipsis in the top right corner, choose Special access, and then select Appear on top. Review the list and revoke permissions for any untrusted applications.
Install Unknown Apps
Installing applications from unknown sources is another practice that should be avoided unless you are certain of the APK file’s origin. This capability, which is disabled by default for security reasons, allows apps to install software from outside the Google Play Store. Such actions can jeopardize your device’s security and privacy, potentially compromising stored data. Even non-malicious apps can clutter your device with unnecessary installations, consuming valuable storage and system resources.
To check which apps have permission to install unknown applications, navigate to Apps in Settings, tap the ellipsis, select Special access, and then choose Install unknown apps. Revoke permissions for any apps that you do not trust.
Usage Data Access
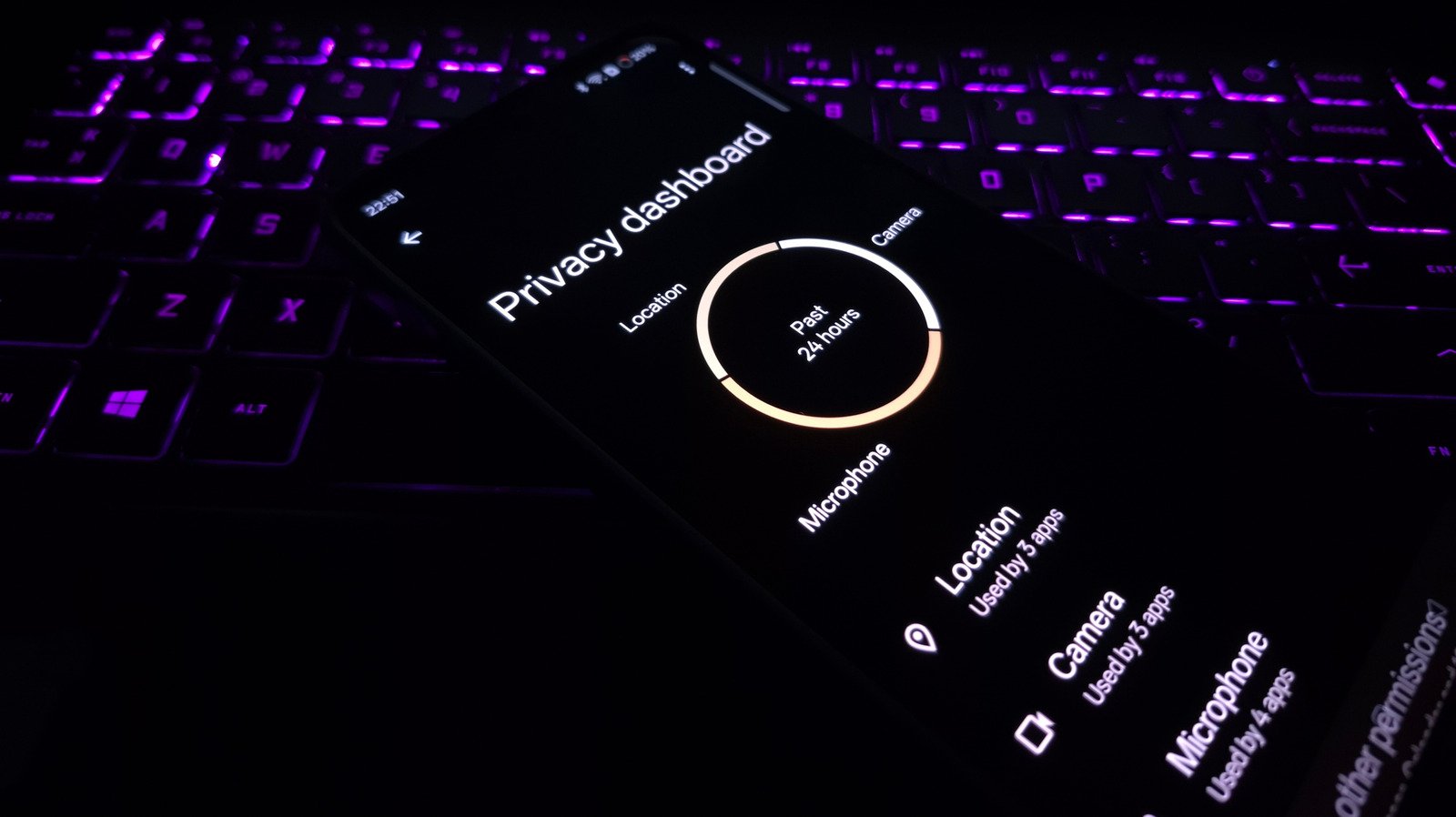
Usage data access is another critical permission that requires attention. When granted, this permission enables apps to monitor your activity, including the frequency and duration of app usage. While this may seem innocuous, it allows applications to compile a profile of your habits and routines, which can be sold to advertisers and data brokers for targeted marketing.
To review which applications have access to usage data, open Settings, select Apps, tap on Special access from the ellipsis menu, and choose Usage data access. Identify any applications that should not be collecting this information and disable their access.
Contacts and SMS Access
Granting apps access to your contacts and SMS can lead to significant privacy concerns. Contacts contain sensitive information, including names, email addresses, and relationships, which can be exploited if accessed by malicious entities. Similarly, SMS messages often include personal conversations and banking one-time passwords (OTPs), which can be intercepted by harmful applications to facilitate unauthorized transactions.
To check which apps have access to your contacts and SMS, navigate to Apps in Settings, tap the ellipsis, select Permission manager, and review the Contacts and SMS sections. Disable permissions for any untrusted applications. It is essential to remember that not all permissions are inherently dangerous; the risk lies in the specific app requesting them. By cultivating a habit of granting permissions that align with an app’s core functionality, you can significantly mitigate potential threats.