ESET researchers have recently unveiled two distinct Android spyware campaigns that cleverly masquerade as secure messaging applications, specifically Signal and ToTok. These malicious programs, which have not been found in official app stores, are being disseminated through phishing websites and counterfeit app marketplaces.
First identified in June 2025, these campaigns introduce two previously undocumented malware families: ProSpy and ToSpy. ProSpy presents itself as either a “Signal encryption plugin” or an enhanced version of ToTok, while ToSpy solely imitates the ToTok app. Both strains are meticulously crafted to extract a wide array of sensitive user information and ensure prolonged access to compromised devices.
The operations seem to primarily target users in the United Arab Emirates, capitalizing on the popularity of ToTok in the region and the growing interest in encrypted communication. The distribution strategy heavily relies on social engineering tactics, with malicious websites designed to resemble trusted sources. For example, one ToSpy distribution site deceptively posed as the Samsung Galaxy Store, tricking users into downloading a trojanized ToTok APK.
ToTok, a voice and messaging application developed in the UAE, was removed from both Google Play and Apple’s App Store in 2019 due to surveillance concerns. Despite its removal, the app continues to be used in the region, making it a prime target for impersonation.
ProSpy Campaign
ESET traced the origins of ProSpy back to at least 2024. This malware has been delivered through three phishing sites that advertise fake APKs such as “Signal Encryption Plugin” or “ToTok Pro.” Upon installation, ProSpy requests access to SMS, contacts, and storage. If users grant these permissions, the malware silently begins to collect and exfiltrate data.
The design of ProSpy is particularly insidious, as it avoids detection and resists removal. After installation, it alters its icon and name, masquerading as “Play Services” to blend in with legitimate system applications. When users launch the counterfeit app, they are redirected to the official Signal or ToTok websites, reinforcing the illusion of authenticity.
The types of data exfiltrated by ProSpy include:
- Device metadata and IP address
- SMS messages
- Contacts
- Media files and documents
- Archive formats and APKs
- List of installed apps
This data is temporarily stored in local JSON files before being transmitted to remote command-and-control (C&C) servers.
ToSpy Attacks
In parallel, ESET also discovered ToSpy in June 2025 after its telemetry flagged a suspicious APK from a device in the UAE. Tracing its origins back to mid-2022 based on certificate creation dates and domain registrations, the malware appears to be maintained by a single actor, indicated by consistent coding practices and certificate reuse.
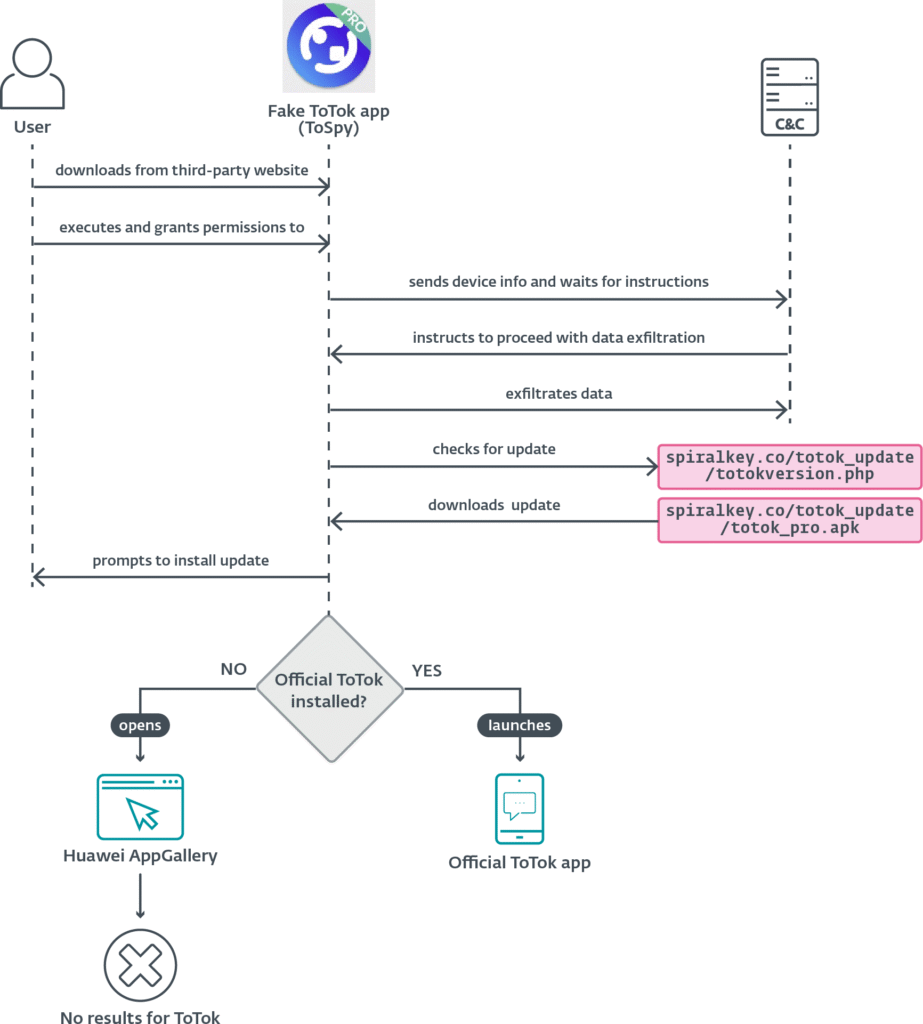
Upon installation, ToSpy requests permissions for storage and contacts, subsequently communicating with a C&C server to await instructions for data theft. Notably, ToSpy actively seeks files with the .ttkmbackup extension, which are utilized by ToTok for chat and settings backups, indicating a targeted effort to extract conversation histories.
The captured data encompasses contact lists, PDF, DOCX, XLSX, MP3, JPG, and TXT files, in addition to device information. This data is encrypted using AES in CBC mode with a hardcoded key before being dispatched to the attacker’s infrastructure.
ToSpy also mimics legitimate app update behavior by querying a remote server and prompting users to manually install new APKs. While researchers have not retrieved these payloads, this functionality suggests an update mechanism capable of replacing older spyware versions with newer ones.
Both ProSpy and ToSpy utilize various methods to maintain long-term control over infected devices, including:
- Foreground services that keep the spyware operational and difficult to terminate
- AlarmManager to periodically restart services if they are stopped
- Broadcast receivers triggered on device boot to reinitialize malicious processes
ESET has noted that the ToSpy campaign remains active, with multiple C&C servers still operational as of October 2025. The researchers have reported their findings to Google, leading to Play Protect now blocking known variants of both ToSpy and ProSpy.