Cybersecurity researchers at zLabs have identified a growing menace to mobile payment security, revealing more than 760 malicious Android applications that exploit Near Field Communication (NFC) and Host Card Emulation (HCE) technologies. These applications are designed to steal payment data and facilitate fraudulent transactions.
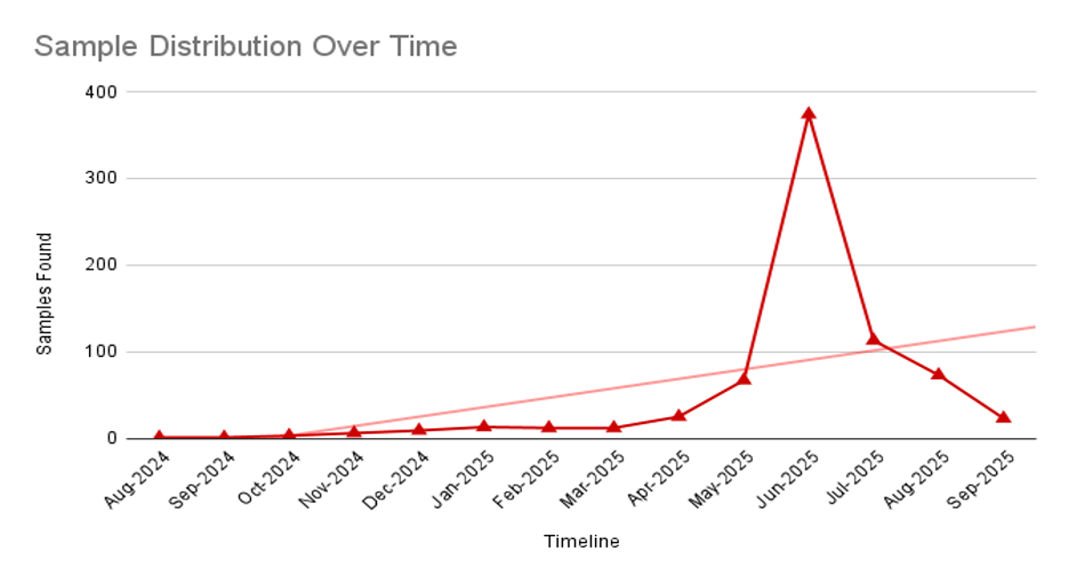
Since April 2024, this intricate campaign has transformed from sporadic incidents into a coordinated global operation, targeting financial institutions in various countries. The malware’s reach has expanded significantly, now affecting users in regions such as Russia, Poland, the Czech Republic, Slovakia, and Brazil.
To execute their plans, threat actors have established around 70 command-and-control servers, supplemented by numerous Telegram bots and private channels for data exfiltration and operational coordination. The malicious applications masquerade as approximately 20 legitimate entities, primarily focusing on Russian banks like VTB Bank, Tinkoff Bank, and Promsvyazbank, while also targeting international institutions such as Santander, PKO Bank Polski, Bradesco, and mobile payment platforms like Google Pay.
Technical Operation and Data Exfiltration Methods
The malicious applications utilize various operational strategies to compromise payment credentials. Some variants act as scanner and tapper tools, where one application extracts card data while another interacts with Point of Sale systems to finalize unauthorized purchases. Other variants are dedicated solely to harvesting card information, sending it directly to specified Telegram channels. Automated messages relay device identifiers, card numbers, expiration dates, and EMV fields to the attackers.
These applications are designed to minimize user interaction by presenting simplified, full-screen interfaces that closely resemble legitimate banking portals, often employing WebView components. The malware encourages users to set the application as the default NFC payment method, while background services quietly intercept NFC events.
The attack chain activates a Host Card Emulation HostApduService during NFC payment events, enabling real-time relay of Application Protocol Data Units (APDUs) between compromised devices and attacker-controlled infrastructure. This command structure allows for bidirectional communication between infected devices and command servers through WebSocket.
Critical commands include registration sequences that transmit hardware identifiers and NFC capabilities, APDU relay operations that forward terminal requests to servers for crafted responses, and Telegram notification functions that deliver exfiltrated data to the attackers. Additional commands manage device pairing status, PIN requests, and forced application updates.
Defense Evasion and Obfuscation Techniques
To evade detection, threat actors employ advanced defense-evasion strategies, including name masquerading to impersonate legitimate financial institutions and government services, such as Russia’s Gosuslugi portal and central banking authorities. The malware utilizes code obfuscation and software packing techniques, specifically leveraging JSONPacker to hide malicious functionality from static analysis tools.
This campaign marks a significant escalation in NFC-based financial fraud, illustrating how threat actors exploit Android permissions to carry out device-level theft of payment credentials. The ongoing growth of this threat indicates that NFC relay abuse is likely to remain a persistent challenge for mobile payment ecosystems, necessitating increased vigilance regarding applications that request NFC payment privileges.
Find this Story Interesting! Follow us on Google News, LinkedIn and X to Get More Instant Updates