Cybersecurity researchers have unveiled a complex malware campaign that cleverly utilizes Windows shortcut (.LNK) files disseminated through Discord to launch a multi-functional Remote Access Trojan (RAT). This attack exemplifies advanced evasion techniques, skillfully exploiting legitimate Windows binaries while circumventing multiple layers of security mechanisms.
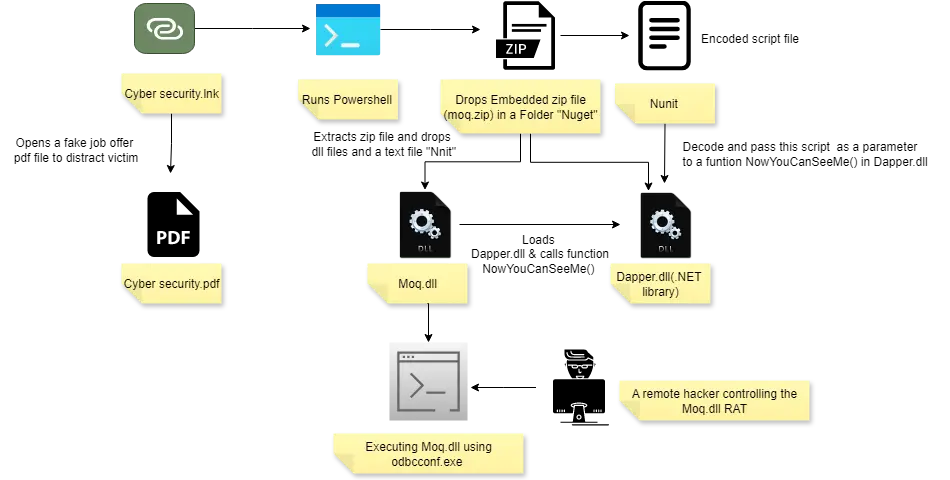
The malicious LNK file, masquerading as “cyber security.lnk,” entices users with a counterfeit job offer PDF, all the while executing PowerShell commands discreetly in the background. Upon activation, the shortcut reveals a decoy document titled “Cyber Security.pdf,” designed to distract victims as it deploys its payload through a meticulously crafted infection chain.
Living-off-the-Land Binary Abuse
A standout feature of this malware is its manipulation of odbcconf.exe, a legitimate Windows command-line utility typically employed for configuring ODBC drivers. By leveraging this Living-off-the-Land Binary (LOLBin), the attack executes a malicious DLL named Moq.dll without raising security alarms.
The PowerShell script extracts an embedded ZIP file containing the malicious payload and executes it using the command: odbcconf.exe /a {regsvr "C:UsersPublicNugetmoq.dll"}. This strategy effectively bypasses conventional security tools by utilizing a trusted Windows binary for nefarious purposes. The malware discreetly creates a hidden “NuGet” folder in the Public directory to house its components, including supporting DLLs such as Dapper.dll and Newtonsoft.dll.
Advanced Evasion Techniques
Moq.dll incorporates several sophisticated evasion strategies to elude detection. It modifies the AmsiScanBuffer function by overwriting its initial six bytes with assembly code that ensures the Anti-Malware Scan Interface (AMSI) consistently fails, effectively neutralizing Windows’ built-in malware scanning capabilities.
In a similar vein, the RAT disables Windows Event Tracing (ETW) by altering the EtwEventWrite function in ntdll.dll, obstructing security solutions from monitoring its activities via event logs. These modifications employ identical byte sequences that redirect both functions to return failure codes immediately.
The malware secures persistence by altering the Windows registry key HKCUSOFTWAREMicrosoftWindows NTCurrentVersionWinlogonShell, guaranteeing that it runs alongside explorer.exe with each user login. It establishes a communication channel with its command and control server at hotchickenfly.info, generating unique machine identifiers for tracking compromised systems.
The RAT boasts capabilities that include capturing screenshots, gathering system information regarding installed antivirus software, and exfiltrating data through Dropbox’s API using hardcoded tokens. To further evade detection, the malware encrypts its communications and commands using AES encryption.
Identified by security researchers from K7 Labs, this threat was initially observed in Israel. The attack underscores the increasing trend of malware authors exploiting legitimate Windows utilities to evade detection while deploying sophisticated RATs capable of extensive system compromise.
To counter such advanced threats, organizations are advised to implement application whitelisting, monitor LOLBin usage, and deploy endpoint detection solutions that can identify behavioral anomalies.
IOC’s
| Hash | Detection Name |
| 7391C3D895246DBD5D26BF70F1D8CBAD | Trojan (0001140e1) |
| 2956ec73ec77757271e612b81ca122c4 | Trojan (0001140e1) |
| 5a1d0e023f696d094d6f7b25f459391f | Trojan (0001140e1) |
| 92fc7724688108d3ad841f3d2ce19dc7 | Trojan (0001140e1) |
Find this Story Interesting! Follow us on Google News, LinkedIn, and X to Get More Instant Updates.