A sophisticated information-stealing malware known as Lumma Infostealer is making a notable resurgence, posing a significant threat to cybersecurity. This malware specifically targets high-value credentials and sensitive assets on Windows systems, exploiting vulnerabilities in a way that is becoming increasingly alarming.
Distributed through a Malware-as-a-Service (MaaS) model, Lumma Infostealer empowers even less experienced attackers to launch intricate data theft campaigns with relative ease. By simply subscribing to the service, these individuals can access tools that were once only available to skilled cybercriminals.
Phishing campaigns are the primary vehicle for deploying Lumma, often masquerading as cracked or pirated software. These malicious downloads are frequently hosted on legitimate platforms, such as MEGA Cloud, allowing them to evade detection by traditional security measures.
Upon execution, Lumma Infostealer initiates a multi-stage decryption process and employs process injection techniques to activate its payload while remaining hidden from conventional antivirus solutions.
Technical Breakdown of Lumma Operations
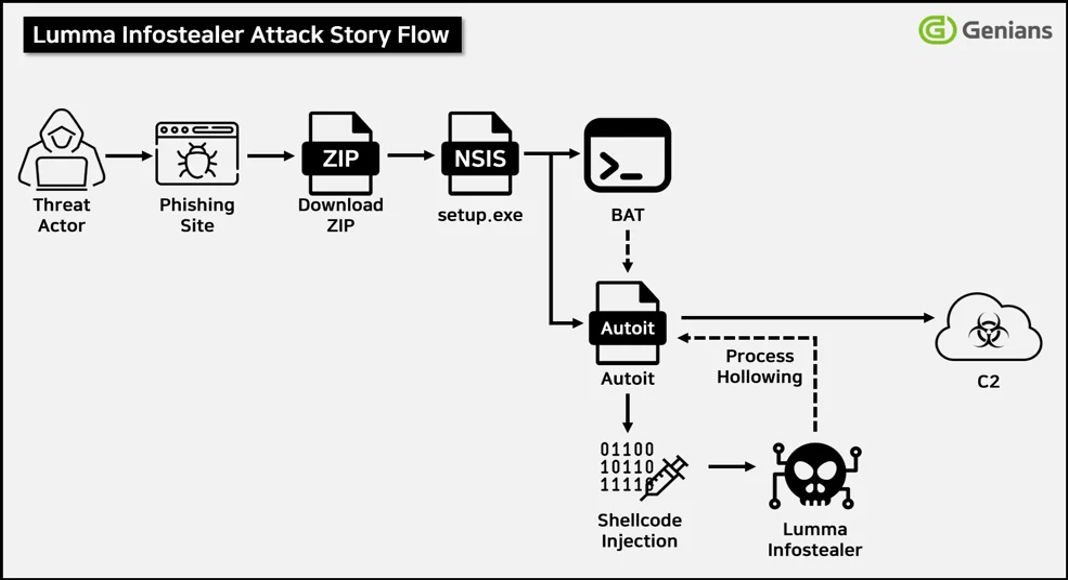
Researchers at Genians Security Center (GSC) have identified that the latest samples of Lumma utilize the Nullsoft Scriptable Install System (NSIS) as a deceptive installer package. When a victim runs the downloaded “setup.exe,” it extracts malicious payloads into the %Temp% directory and launches a counterfeit “Contribute.docx” file via cmd.exe.
This document triggers a sequence of commands that reconstruct a concealed AutoIt-based loader for deploying Lumma’s encrypted core. The AutoIt script employs shellcode injection and process hollowing to embed the Lumma payload within a benign process, effectively masking its actions.
Once the payload is activated, it decrypts command-and-control (C2) domains and establishes communication with remote attacker servers, including rhussois[.]su, diadtuky[.]su, and todoexy[.]su.
Through this connection, Lumma Infostealer systematically gathers stored browser credentials, session cookies, Telegram data, remote access configuration files, and cryptocurrency wallet information. The exfiltrated data is then sent to C2 servers for further exploitation, potentially leading to identity theft, corporate breaches, or the resale of credentials on dark web forums.
To enhance its stealth, the malware checks for running processes to avoid early termination and will deactivate its functions if it detects security solutions such as Sophos, Norton, ESET, Bitdefender, or Avast. Its modular architecture and frequent updates further complicate signature-based detection methods.
EDR-Based Detection and Response
Experts emphasize that effective detection of Lumma Infostealer necessitates behavior-based Endpoint Detection and Response (EDR) systems. These systems are capable of monitoring command chains, file drops, and process relationships in real time.
For instance, Genian EDR provides a visual representation of Lumma’s attack narrative, offering insights into shellcode injection, AutoIt script execution, and network communication events as they unfold.
To mitigate exposure to such threats, security professionals recommend avoiding the storage of credentials in browsers, enforcing multi-factor authentication (MFA), and keeping a vigilant eye on suspicious child processes that may arise from installer files. As Lumma continues to adapt within the MaaS economy, it highlights the growing industrialization of cybercrime and the pressing need for sophisticated, correlational threat monitoring.
IoC (Indicator of Compromise)
- E6252824BE8FF46E9A56993EEECE0DE6
- E1726693C85E59F14548658A0D82C7E8
- 19259D9575D229B0412077753C6EF9E7
- 2832B640E80731D229C8068A2F0BCC39
- diadtuky[.]su
- rhussois[.]su
- todoexy[.]su
Find this Story Interesting! Follow us on Google News, LinkedIn, and X to Get More Instant Updates