Following the October 2025 Patch Tuesday updates, a significant number of Windows users have encountered a perplexing issue: the File Explorer preview pane has ceased functioning for many commonly used file types. What initially appeared to be a mere bug is, in fact, a calculated security enhancement by Microsoft, impacting both Windows 11 and Windows 10. In a decisive move that prioritizes security over user convenience, Microsoft has fundamentally modified a core feature of File Explorer to address a critical vulnerability. The updates, identified as KB5066835 for Windows 11 and KB5066791 for Windows 10, have sparked widespread confusion and disrupted established workflows for users who depend on previewing documents downloaded from the internet.
A Security Fix, Not a Bug
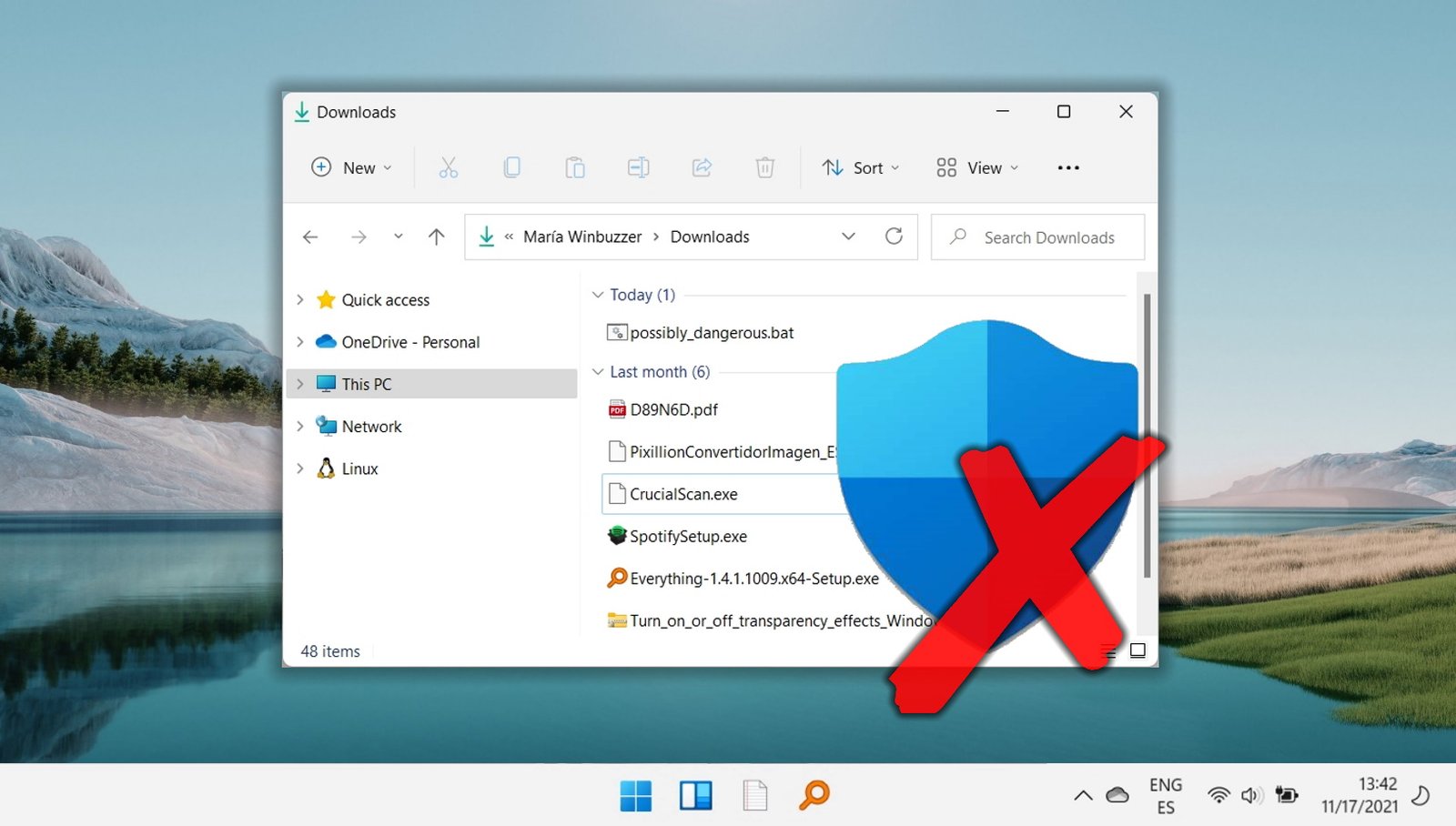
In place of a file preview, users are now met with a warning message. Microsoft’s official support documentation clarifies the situation, stating that the pane will now display the following text: “The file you are attempting to preview could harm your computer. If you trust the file and the source you received it from, open it to view its contents.” This abrupt change has taken many users by surprise, leading to a flurry of complaints on platforms like Reddit. For professionals who verify dozens of new PDF documents daily, this is more than a minor inconvenience. The absence of the preview feature necessitates that each file be unblocked or opened individually, significantly increasing the time and effort required to complete their tasks.
The crux of the issue lies with a security identifier known as the “Mark of the Web” (MotW). Windows automatically assigns this mark to any file downloaded from the internet, synchronized from a cloud service like OneDrive, or accessed from a network share. Microsoft explains, “Preview functionality is disabled by default for files marked with Mark of the Web (MotW), which indicates they originated from the internet Security Zone.” This proactive measure is now the default setting for all such files.
How the NTLM Vulnerability Works
At the core of this change is a serious vulnerability associated with NTLM credential hashes. To fully appreciate the implications, it’s essential to understand how these hashes can be exploited. NTLM (NT LAN Manager) is a suite of Microsoft security protocols. When a user accesses a network resource, their system may send an NTLM hash of their password to verify their identity. In a “pass-the-hash” attack, an adversary does not require the actual password; they merely need to capture this hash. Once obtained, they can reuse it to impersonate the user and gain access to other systems and data on the network. The vulnerability that Microsoft is addressing allowed a malicious file to deceive File Explorer into sending this hash to an attacker-controlled server, simply by being previewed. The company’s support article emphasizes the risk, noting, “This change mitigates a vulnerability where NTLM hash leakage might occur if users preview files containing HTML tags (such as , , and so forth) referencing external paths.” This type of exploit, akin to the one detailed in CVE-2025-24054, is particularly perilous as it requires minimal user interaction. By disabling the preview for files sourced from the internet, Microsoft effectively prevents this covert credential theft from occurring.
Restoring Previews: Workarounds and Risks
For those who comprehend the risks and wish to restore the preview functionality, Microsoft has outlined official workarounds. The most straightforward method is to manually remove the Mark of the Web on a per-file basis. Users can right-click the downloaded file, select Properties, and on the General tab, check the Unblock box at the bottom. Once this change is applied, the preview pane will operate as it did previously for that specific file. For files located on a network share, a broader but potentially riskier solution is available. Users can add the file share’s address to either the Local intranet or Trusted sites security zones via the classic Internet Options control panel. This action instructs Windows to trust all content from that source, but it comes with a significant security trade-off. Microsoft cautions that this will relax the security posture for every file on that share, effectively bypassing the MotW protection entirely for that location.
The New Normal: Security by Default
This initiative by Microsoft reflects a broader industry trend toward a “secure by default” approach. Operating system developers are increasingly willing to introduce user friction to close potential attack vectors. Similar philosophies can be observed in Apple’s macOS Gatekeeper, which scrutinizes applications from unidentified developers, as well as in modern web browsers that prominently display warnings for insecure downloads. For IT administrators, this shift presents new challenges in balancing centrally-managed security policies with employee productivity. While the disabled preview pane may be an inconvenience, it heralds a new era where users and organizations must exercise greater caution in trusting digital content, treating every file from the internet as potentially suspect until proven otherwise.
How to Unblock Downloads in Windows 11
When downloading a file, Windows often blocks it or displays a warning to prevent potential harm to your PC. The Attachment Manager, responsible for this protection, may sometimes block files that are entirely safe. Therefore, it becomes necessary to know how to unblock files on Windows 11 to ensure uninterrupted access.