In recent weeks, a particularly insidious email scam has emerged, posing a significant threat to unsuspecting users. Cybercriminals are sending out counterfeit invitations—often styled as party or work-related activities—that, when clicked, install a backdoor into the victim’s computer system. This seemingly innocuous action can grant hackers full control over the device, leading to potentially devastating consequences.
Here’s how the scam happens
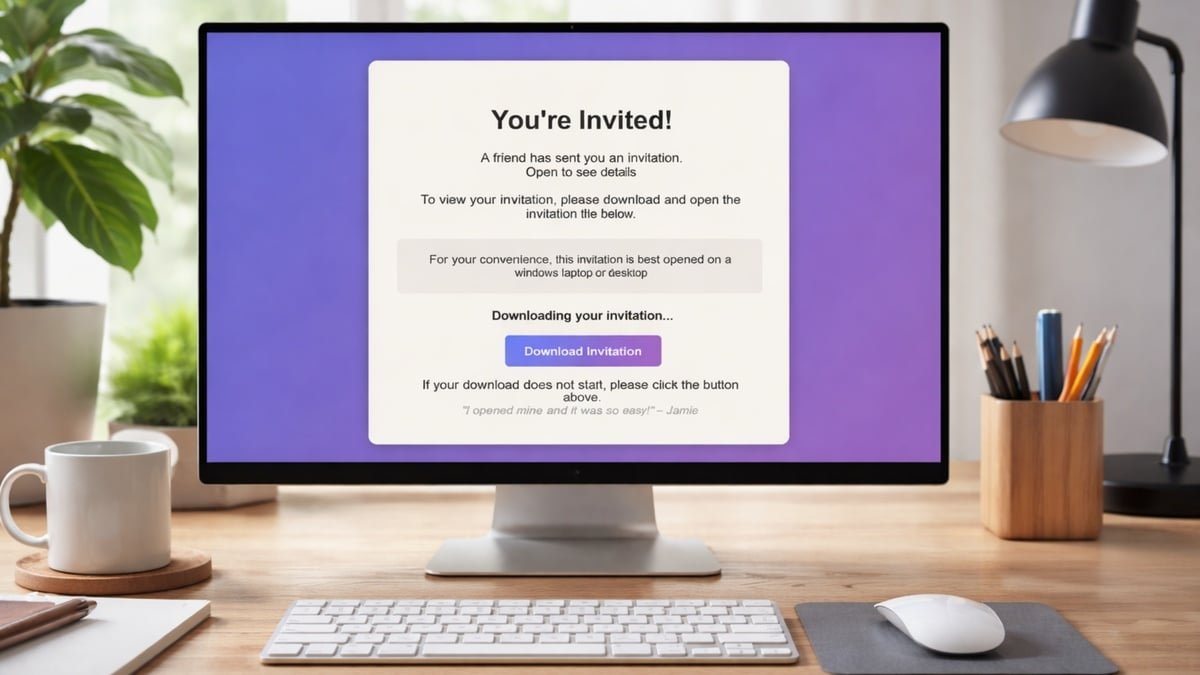
Even I found myself on the brink of falling victim to this scam. A colleague reached out for feedback on a project, and I clicked on the link provided in the email. Instead of directing me to a feedback form, I was taken to a page that prompted me to download an invitation file.
My instincts kicked in at this point; I had anticipated a straightforward form, not a file download. Nevertheless, I proceeded to download the file named “invites.msi.” For context, an MSI file is a Windows Installer package, a format commonly used by Microsoft for software installations on Windows PCs. This was yet another red flag, and my suspicions grew stronger.
To investigate further, I ran the MSI file in a secure environment and discovered that it would have installed ScreenConnect, a legitimate remote support tool favored by IT teams. However, in the hands of malicious actors, this software could allow them to monitor your screen, access files, deploy additional malware, and extract saved credentials.
Because ScreenConnect is a legitimate tool, it often goes undetected by Windows security measures and antivirus programs, which may not flag it as suspicious. In fact, when I checked the installer file with VirusTotal, only six out of sixty-three security engines identified it as malicious. By the time one realizes something is amiss, it may already be too late.
What to do if you’ve already fallen for this scam
If you suspect that you have fallen prey to this scam, it is crucial to act swiftly, assuming a full system compromise. The following steps, while not pleasant, are essential for regaining control:
- Disconnect the affected computer from the internet. Disable Wi-Fi or unplug the Ethernet cable to terminate the attacker’s active session and halt any further data transfer.
- Check for any remote management software that may have been installed. On Windows, navigate to Settings > Apps > Installed Apps (or “Apps & Features” on older versions) and look for unfamiliar entries, particularly anything labeled “ScreenConnect Client” or “ConnectWise.” If found, uninstall it immediately.
- After uninstalling, verify that the associated Windows service is removed. Press Windows key + R, type services.msc, and check for any services related to ScreenConnect or similarly named remote clients. If any remain, that’s a cause for concern.
- Run a comprehensive antivirus or endpoint security scan using a reputable tool (I personally recommend Bitdefender). Even if the installer contained legitimate software, attackers may use remote access to introduce additional malware.
- Assume that any passwords used on the compromised computer may have been exposed. From a separate, clean device, change passwords for:
- Email accounts
- Banking and financial services
- Cloud storage
- Social media
- Work accounts
- Password manager (if installed on that PC)
- Enable two-factor authentication on all critical accounts, especially email. If your email is compromised, attackers can reset other passwords and regain access.
- If the affected computer is used for work, inform your IT department immediately. In corporate environments, remote access compromises can lead to broader vulnerabilities within company systems.
- If sensitive financial data, crypto wallets, or confidential documents were stored on the machine, consider performing a full Windows reset. Once someone has had remote access, it can be challenging to ascertain what they modified or extracted.
- To reset Windows, go to Settings > System > Recovery > Reset this PC and select the option to remove everything. Reinstalling the operating system ensures any persistent threats are eliminated.
- Finally, monitor your financial accounts and email activity closely for several weeks. Be vigilant for unfamiliar login alerts, password reset attempts, or new devices appearing in your account security settings.
How this scam started
After confirming that the email I received was indeed from my colleague and not a spoof, I followed up with him and learned that his email account had been compromised. Once attackers gained access to his inbox, they exploited this trusted platform to target his contacts. They didn’t merely send out the malicious link; they actively monitored his inbox, responding to inquiries and reassuring recipients of the email’s legitimacy.
In my colleague’s case, his credentials were likely phished or exposed in a data breach. The underlying issue was a lack of basic security hygiene. He had not enabled two-factor authentication on his email account and was not utilizing a password manager.
Implementing two-factor authentication (2FA) for email accounts would have likely prevented this incident. Even if his credentials were inadvertently revealed, hackers would have been unable to access his account without the second form of verification. Setting up 2FA for your email should be considered essential.
Additionally, a password manager not only facilitates the use of strong, unique passwords for each account but also helps prevent phishing attempts. Password managers typically do not autofill information on phishing sites, serving as a crucial warning sign that the site may not be legitimate. I personally recommend 1Password, but alternatives like Dashlane, Apple Password, and Google Password are also commendable options.
How to avoid falling for this scam
There is a straightforward principle to keep in mind: legitimate online invitations do not require you to download and run an installer file. If an invitation prompts you to download or open an .msi or .exe file, pause and reconsider. This is not how reputable invitation services operate. More generally, refrain from allowing any program to install on your computer unless you are fully aware of its purpose and necessity.
Take your time when any email—regardless of whether it comes from a colleague or friend—requests that you download and execute a file. A seemingly simple “invitation” could lead to serious repercussions.