Multiple VPN providers are sounding the alarm over a persistent bug in Android 16 that is causing their services to disconnect unexpectedly, often without any warning for users. Companies such as Proton VPN, Mullvad, WireGuard, and TunnelBear report that this issue tends to arise following routine app updates, leaving devices vulnerable or completely offline until a reboot or reinstallation of the VPN app occurs. Google has acknowledged these concerns through its Issue Tracker, yet has not provided a timeline for a fix.
What VPN providers are seeing on affected Android 16 devices
According to developer notes from the affected applications, the network stack in Android 16 can enter a problematic state when a VPN is updated while still connected. In this state, the VPN app is unable to access the internet, resulting in a perpetual “connecting” loop. Users may not receive any clear error messages, and depending on their settings, they might either lose all connectivity or have non-VPN traffic continue to flow outside the secure tunnel.
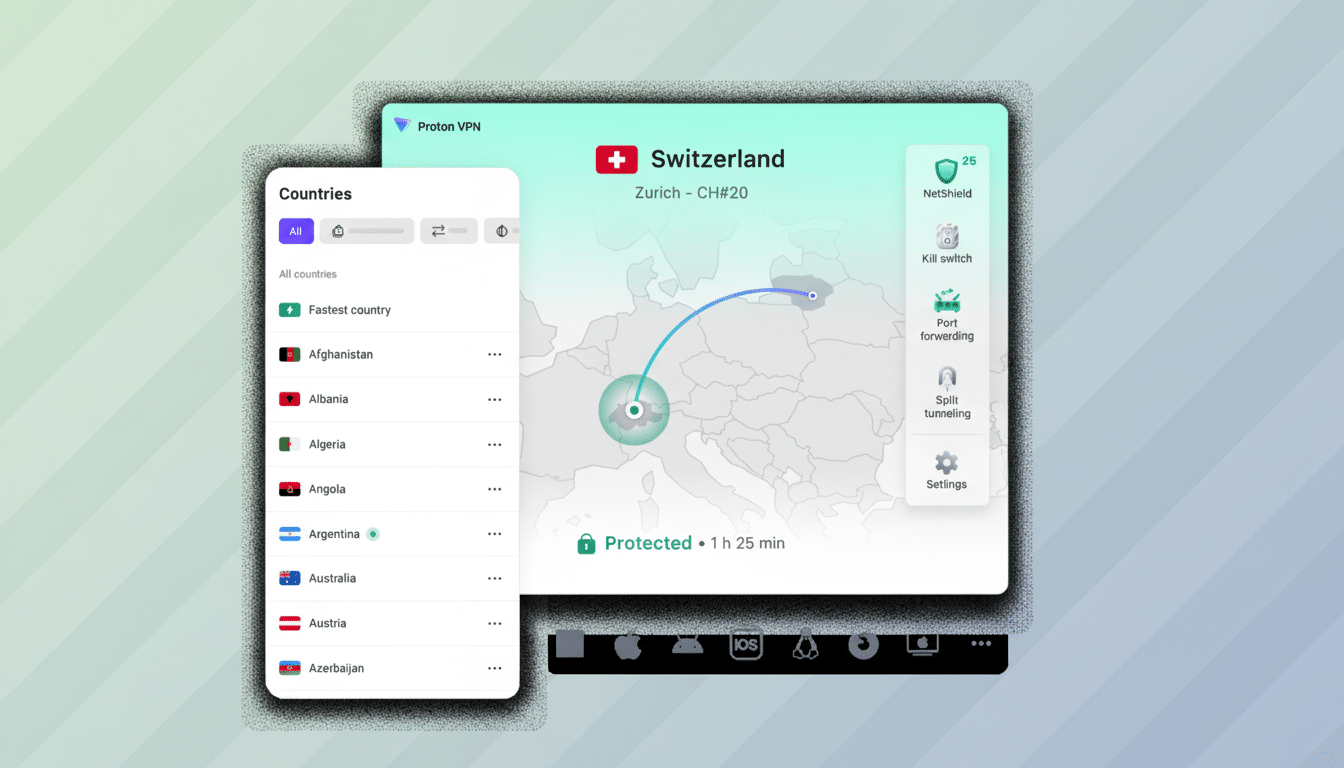
The reports indicate a consistent pattern across various implementations. Proton VPN and Mullvad utilize the standard Android VpnService with a TUN interface, while WireGuard employs its own kernel/user-space driver pairing. TunnelBear operates on a similar stack. The common thread among these providers is the way Android 16 manages the VPN service after an app update occurs while a session is active.
How the Android 16 VPN bug manifests after app updates
Developers suspect that the issue lies in how Android reapplies per-app network rules following an update. When an update is initiated, the system temporarily dismantles and restarts components associated with the app’s unique identifier (UID). If the firewall or routing rules associated with the VPN service are left in a stale or conflicting state, the VPN process is unable to reconnect to the network, even though the user interface continues to indicate that it is attempting to do so.
This failure appears to be intermittent. While providers describe it as infrequent during any single update cycle, it is common enough across millions of devices to generate daily support inquiries. Restarting the VPN app typically does not resolve the issue. A complete device reboot or uninstalling and reinstalling the app can clear the obstructed rules and restore normal functionality.
Why this Android 16 VPN bug matters for privacy and safety
Android incorporates two essential safety features: Always-on VPN, which strives to maintain an active tunnel at all times, and “Block connections without VPN,” which prevents any traffic from bypassing the secure connection. This current bug undermines both functionalities. With lockdown enabled, users may suddenly lose all connectivity without realizing that an app update triggered the disruption. Conversely, with lockdown disabled, the VPN may fail while other applications continue to transmit data, increasing the risk of unintended exposure.
The broader implications could be substantial. StatCounter estimates that Android commands approximately 70% of the global mobile operating system market, while survey data from firms like GlobalWebIndex indicates that around 30-35% of internet users utilize VPNs in some form. Even if the bug affects only a small percentage of sessions, the total number of impacted users could be significant.
Temporary workarounds you can try while waiting for a fix
- Reboot your device immediately if your VPN becomes stuck in a “connecting” state after an app update.
- Manually disconnect the VPN before performing an update, then reconnect once the update is complete.
- Consider pausing auto-updates for your VPN app until a confirmed fix is available, particularly if you rely on always-on or lockdown mode.
- After any update, verify your protection by checking your IP location within the VPN app or using a trusted checker, and ensure that the VPN key icon is displayed in the status bar.
Providers note that generic troubleshooting steps, such as force-closing the app or clearing the cache, are rarely effective. If your device is managed by an enterprise mobility tool, it is advisable to coordinate with IT before altering settings like lockdown mode.
Enterprise and developer stakes for always-on VPN policies
For organizations enforcing always-on VPN and lockdown policies on corporate devices, this bug can inadvertently disrupt access to internal resources and compromise zero-trust policies. This situation elevates operational risks and support costs, particularly for frontline or remote workers who rely heavily on mobile connectivity.
Developers are actively exploring app-side mitigations, such as delaying service restarts immediately following an update, prompting users to reboot, or detecting the blocked state and cycling the VPN in a controlled manner. Ultimately, they emphasize that a platform-level fix is essential to ensure that network rules are accurately reapplied after updates.
What Google says so far and what Android VPN users should watch
Google has acknowledged the reports on its Issue Tracker and indicated that the issue has been escalated to the appropriate teams. However, no patch or timeline has been announced. Due to the sporadic nature of the bug, providers encourage users to submit bug reports and logs when the issue arises to assist engineers in identifying the root cause.
Users should remain vigilant for a platform update or security patch that specifically addresses VPN service handling after app updates. Until a resolution is found, it is prudent to treat post-update reconnects as a critical moment, monitor your status icon, and verify your tunnel after each update—especially on devices utilizing always-on or lockdown mode.