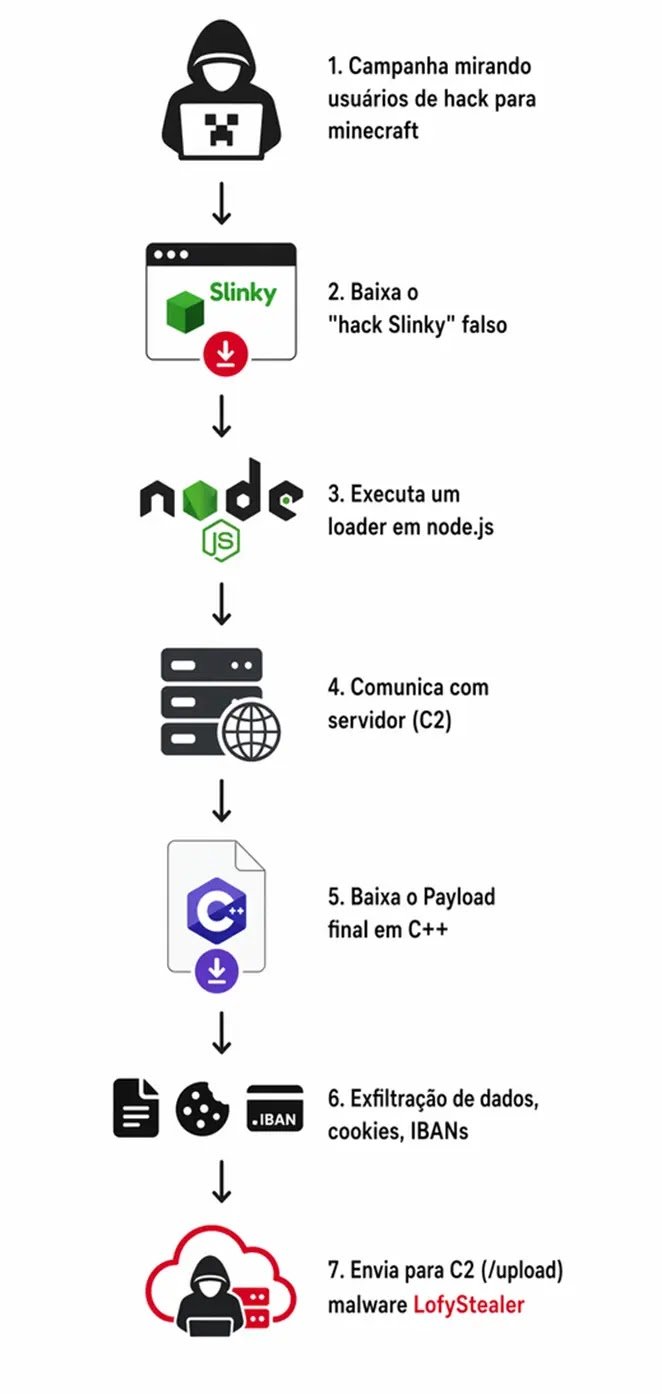
A new wave of cyber threats has emerged, with a particularly dangerous infostealer malware known as LofyStealer targeting the gaming community, specifically players of Minecraft. This malware cleverly disguises itself as a game cheat tool called “Slinky,” making it all the more enticing for unsuspecting users.
The LofyStealer operates through a sophisticated two-stage attack, stealthily extracting sensitive information from popular web browsers while remaining largely undetected by conventional security software. This level of sophistication marks a significant evolution in gaming-related malware, as LofyStealer combines a Node.js-based loader with a native C++ payload that is injected directly into the live memory of browsers during execution.
Notably, LofyStealer casts a wide net, targeting eight major browsers including Chrome, Edge, Brave, Opera GX, and Firefox. It meticulously siphons off cookies, saved passwords, payment card information, active session tokens, and IBANs from each of these platforms.
Researchers at Zenox.ai made the initial identification of this malware during their active threat hunting on the ANY.RUN sandbox platform. Their analysis linked the campaign to the LofyGang group, a Brazilian cybercrime organization first noted by Checkmarx in October 2022. This attribution is supported by the presence of hardcoded Brazilian Portuguese strings within the malware’s code, a command-and-control server located in a small Brazilian datacenter, and branding that identifies the operation as “LofyStealer, Advanced C2 Platform V2.0.”
The spread of LofyStealer relies entirely on social engineering tactics. The malware is packaged as a Minecraft cheat, complete with the game’s official icon, which lends it an air of legitimacy. This approach is particularly effective given Minecraft’s appeal to a younger demographic that is more likely to download cheats or mods from unofficial sources.
Upon execution, the malware initiates its infection process silently, leaving no visible warning signs for the user. This stealthy operation is indicative of a well-structured business model, as LofyStealer functions as a Malware-as-a-Service (MaaS) platform. It offers both Free and Premium tiers to criminal buyers through a web-based dashboard, with Premium users enjoying access to a victim management panel, a custom executable builder named “Slinky Cracked,” and real-time monitoring of compromised machines.
In-Memory Browser Injection: How LofyStealer Bypasses Security Tools
The technical prowess of LofyStealer is particularly evident in its second-stage payload, chromelevator.exe, which is injected into active browser processes without triggering common security defenses. Once the loader, load.exe, is executed on the victim’s machine, it queries the Windows registry to identify installed browsers. It then launches the identified browser in a suspended state, temporarily pausing the process before it becomes fully active.
The loader maps the payload directly into the browser’s memory space using kernel-level Windows calls. Instead of relying on commonly monitored API functions, it resolves low-level functions from ntdll.dll at runtime through direct syscalls. This technique allows it to evade endpoint detection and antivirus hooks that typically monitor high-level KERNEL32.dll calls, providing the payload with a clean entry into the running browser process.
Once injected, the payload activates within the browser, extracting a wealth of sensitive data, including cookies, stored passwords, session tokens, payment card details, and IBANs across the targeted browsers. The stolen data is then compressed using a hidden PowerShell command, encoded in Base64, and transmitted to the command-and-control server via an HTTP POST request, complete with a SHA-256 integrity signature. The server subsequently makes all stolen records accessible to operators through a live web dashboard.
To mitigate the risks associated with LofyStealer, users and organizations are advised to refrain from downloading Minecraft mods, cheats, or game utilities from unofficial or untrusted sources, particularly those disseminated through Discord channels or unknown file-sharing sites. Endpoint security solutions that can detect in-memory injection behaviors provide stronger protection against this malware than traditional file-based scanning methods.
Additionally, enabling multi-factor authentication on all gaming, streaming, and financial accounts can significantly reduce the risk of credential theft. Security teams should consider blocking outbound traffic to the IP address 24.152.36.241 on port 8080 and monitoring systems for hidden PowerShell executions, as these are key behavioral indicators of compromise.
Follow us on Google News, LinkedIn, and X to Get More Instant Updates, Set CSN as a Preferred Source in Google.