Surge in NFC Fraud: A Growing Concern for Android Users
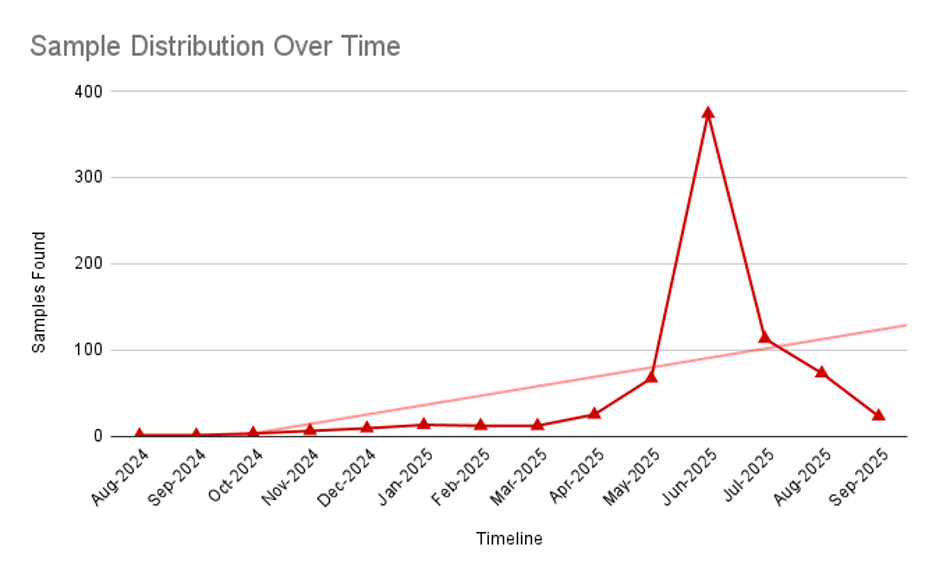
In a troubling development, researchers from Zimperium zLabs have identified over 760 Android applications that are exploiting Near-Field Communication (NFC) and Host Card Emulation (HCE) technologies to illicitly acquire payment data. This alarming trend has seen a significant uptick in NFC relay fraud since April 2024, raising concerns among financial institutions and users alike.
The malicious software targets a wide array of entities, including banks, payment services, and government portals across the globe. Notable victims include Russian banks, various European financial institutions such as PKO, ČSOB, and NBS, as well as Brazilian banks and Google Pay. These deceptive applications masquerade as trusted organizations to ensnare unsuspecting users.
Variants of this malware operate in two primary configurations: as paired “scanner/tapper” toolchains or as standalone data collectors. Both types are adept at exfiltrating sensitive EMV data, which includes device IDs, card numbers, and expiration dates, often transmitting this information to Telegram channels. Users are frequently prompted to set these applications as their default NFC payment handlers, while background services manage Application Protocol Data Unit (APDU) exchanges.
Operators maintain remote control over these applications via command-and-control (C2) servers, issuing straightforward commands that enable them to log in, register devices, relay card terminal requests, provide PINs, check statuses, pair devices, push updates, and send alerts through Telegram. This level of control allows for the execution of fraudulent transactions with minimal user involvement.
The dynamic nature of device registration and command flows poses significant challenges for detection and response efforts. Zimperium’s findings indicate that since April 2024, more than 70 C2 servers and numerous Telegram bots have been deployed to target over 20 institutions worldwide, predominantly focusing on Russian banks through a multitude of malicious NFC-enabled app variants.
As highlighted in Zimperium’s report, the rise of “Tap-to-Pay” transactions has made NFC an increasingly appealing target for cybercriminals. The report emphasizes that these harmful applications exploit Android’s NFC permissions to directly pilfer payment data from users’ devices, underscoring the urgency of addressing this growing threat.
In light of these developments, it is crucial for financial institutions, mobile vendors, and users to regard any unfamiliar application requesting NFC payment privileges as a potential risk. Zimperium has made available Indicators of Compromise (IOCs) related to this campaign in a dedicated repository, providing valuable resources for those looking to safeguard their systems.