A new wave of social engineering attacks, dubbed ClickFix, is making its presence felt in the hospitality sector across Europe. This campaign employs a clever ruse involving fake Windows Blue Screen of Death (BSOD) screens to deceive users into unwittingly compiling and executing malware on their systems.
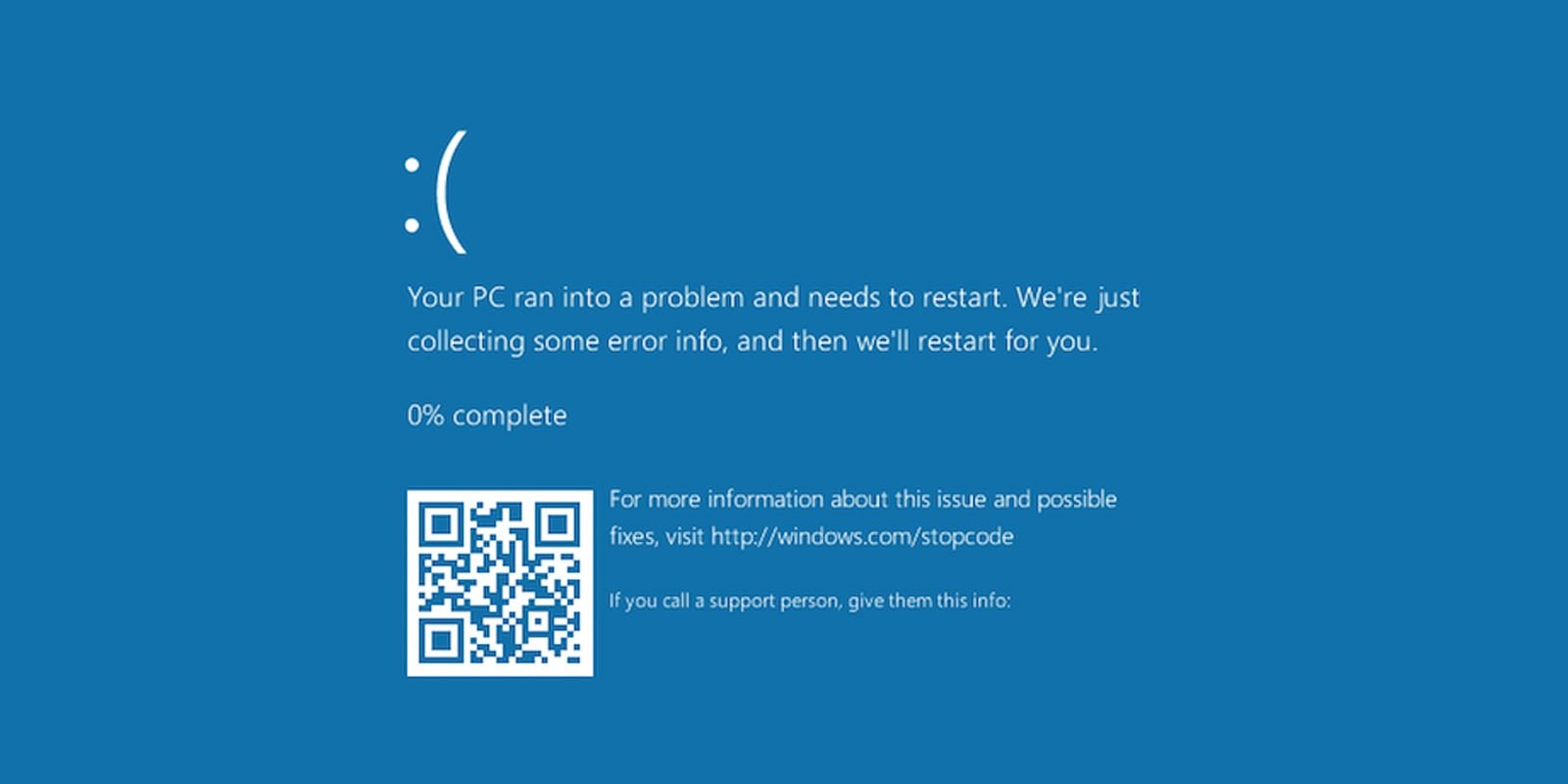
The BSOD, a notorious crash screen that appears when Windows encounters a critical error, serves as the backdrop for this sophisticated phishing scheme. Initially identified in December and tracked by researchers at Securonix under the moniker “PHALT#BLYX,” the campaign involves phishing emails that masquerade as notifications from Booking.com, leading unsuspecting recipients into a trap that deploys malware.
ClickFix attack impersonated BSOD crashes
ClickFix attacks are designed to present users with fabricated error messages or warnings, enticing them to seek solutions that ultimately compromise their systems. These deceptive prompts can take the form of security alerts, CAPTCHA challenges, or update notices, all instructing users to execute commands that inadvertently install malicious software.
In this particular campaign, attackers send emails that impersonate hotel guests canceling their reservations through Booking.com, often targeting hospitality firms. The emails typically mention a substantial refund, creating a false sense of urgency that compels recipients to act quickly.
Source: Securonix
Upon clicking the link in the email, victims are redirected to a counterfeit Booking.com website hosted on ‘low-house[.]com.’ Securonix describes this site as a “high-fidelity clone” of the genuine Booking.com platform.
“The page utilizes official Booking.com branding, including the correct color palette, logos, and font styles. To the untrained eye, it is indistinguishable from the legitimate site,” Securonix reports.
The malicious site employs JavaScript to display a fabricated “Loading is taking too long” error, prompting the target to click a button to refresh the page.
Source: Securonix
However, clicking this button triggers a full-screen display of a fake Windows BSOD crash screen, marking the onset of the ClickFix social engineering attack.
Source: Securonix
This screen instructs the user to open the Windows Run dialog box and press CTRL+V, which pastes a malicious command that has been copied to the clipboard. The user is then prompted to execute the command by pressing OK or Enter.
Unlike authentic BSOD messages, which only display error codes and reboot instructions, these fabricated screens may mislead inexperienced users or hospitality staff under pressure to resolve disputes.
Executing the provided command launches a PowerShell script that opens a decoy Booking.com admin page while simultaneously downloading a malicious .NET project (v.proj) and compiling it using the legitimate Windows MSBuild.exe compiler.
Once executed, the malware adds exclusions to Windows Defender and triggers User Account Control (UAC) prompts to gain administrative rights. It then downloads the primary loader via the Background Intelligent Transfer Service (BITS) and establishes persistence by placing a .url file in the Startup folder.
The malware, known as DCRAT, is a remote access Trojan that grants threat actors control over infected devices. It is injected into the legitimate ‘aspnet_compiler.exe’ process using process hollowing and runs directly in memory.
Upon establishing contact with the command-and-control (C2) server, the malware transmits a complete system fingerprint and awaits further instructions. It is equipped with functionalities such as remote desktop access, keylogging, reverse shell capabilities, and the ability to execute additional payloads in memory. In one instance observed by Securonix, the attackers deployed a cryptocurrency miner.
With remote access secured, the threat actors gain a foothold within the target’s network, enabling them to spread to other devices, exfiltrate sensitive data, and potentially compromise additional systems.